Last Updated on 12 May 2026
How to Detect Unauthorized Job Ads Using Your Company Name
Share in
Introduction
When a candidate sees your company name on a job ad, they assume the job belongs to you.
That assumption creates risk.
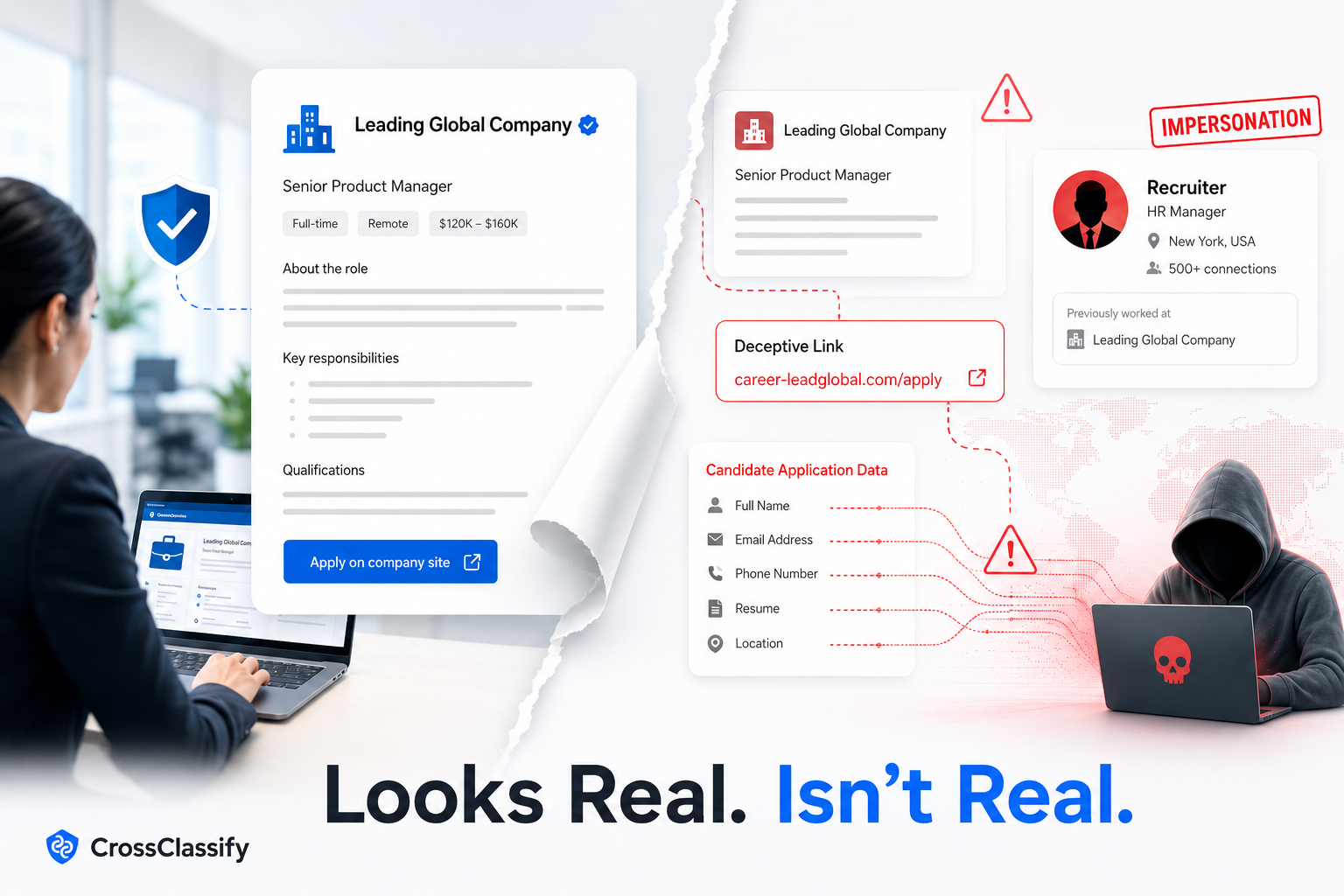
An unauthorized job ad can use your brand, your job description, your office location, and your hiring language. It can appear on a known job board. It can ask candidates to apply through a form that does not belong to your company. It can collect resumes and personal information before your team even knows the listing exists.
For companies with multiple brands, local branches, acquisitions, and decentralized hiring, this becomes a serious visibility problem. A security team may monitor domains. A recruitment team may manage the ATS. A local branch may post jobs independently. An attacker can exploit the gaps between those systems.
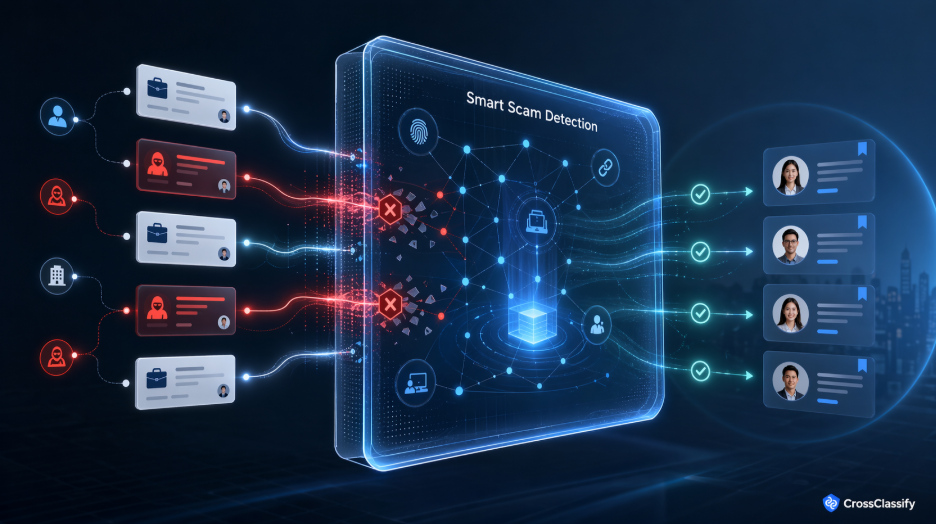
CrossClassify helps companies detect unauthorized job ads by verifying public job listings against trusted hiring sources, monitoring recruitment brand abuse, analyzing suspicious recruiter behavior, and giving human reviewers clear fraud evidence.
What is an unauthorized job ad?
An unauthorized job ad is any public job listing that uses your company name, brand, role, location, or job description without approval.
Some unauthorized ads are caused by internal confusion. A branch may post a job outside the approved process. A staffing partner may repost a role without clear permission. An old job may remain live after the role closes.
Other unauthorized ads are malicious. Attackers may copy real postings and redirect candidates to fake application pages. They may offer unrealistic salaries, request paid training fees, collect identity documents, or move candidates into private messaging channels.
The risk is the same for the applicant. They do not know whether the ad is official.
Why this is hard for multi brand companies
A single brand company may already struggle to monitor public job ads. A multi brand enterprise has a much harder problem.
It may have dozens or hundreds of brand names. It may have acquired companies that still hire under their original names. It may have local branches that operate with autonomy. It may have many domains, many career pages, many recruiter accounts, and many agency relationships.
This creates a fragmented recruitment surface.
Attackers benefit from fragmentation. They can choose a smaller brand, a local branch, a regional office, or an acquired business unit because candidates are less likely to know the exact official hiring path.
This is why CrossClassify recruitment fraud protection focuses on the whole hiring workflow. It helps teams move from scattered manual checks to a centralized trust layer for recruitment fraud signals.
Step 1: Build an approved job source of truth
The first step is to define what counts as an authorized job.
That means creating a trusted inventory of active jobs from your ATS, career site, hiring portal, and approved agency feeds. Each approved job should have a title, location, brand, department, job ID, approved posting channels, canonical application URL, and owner.
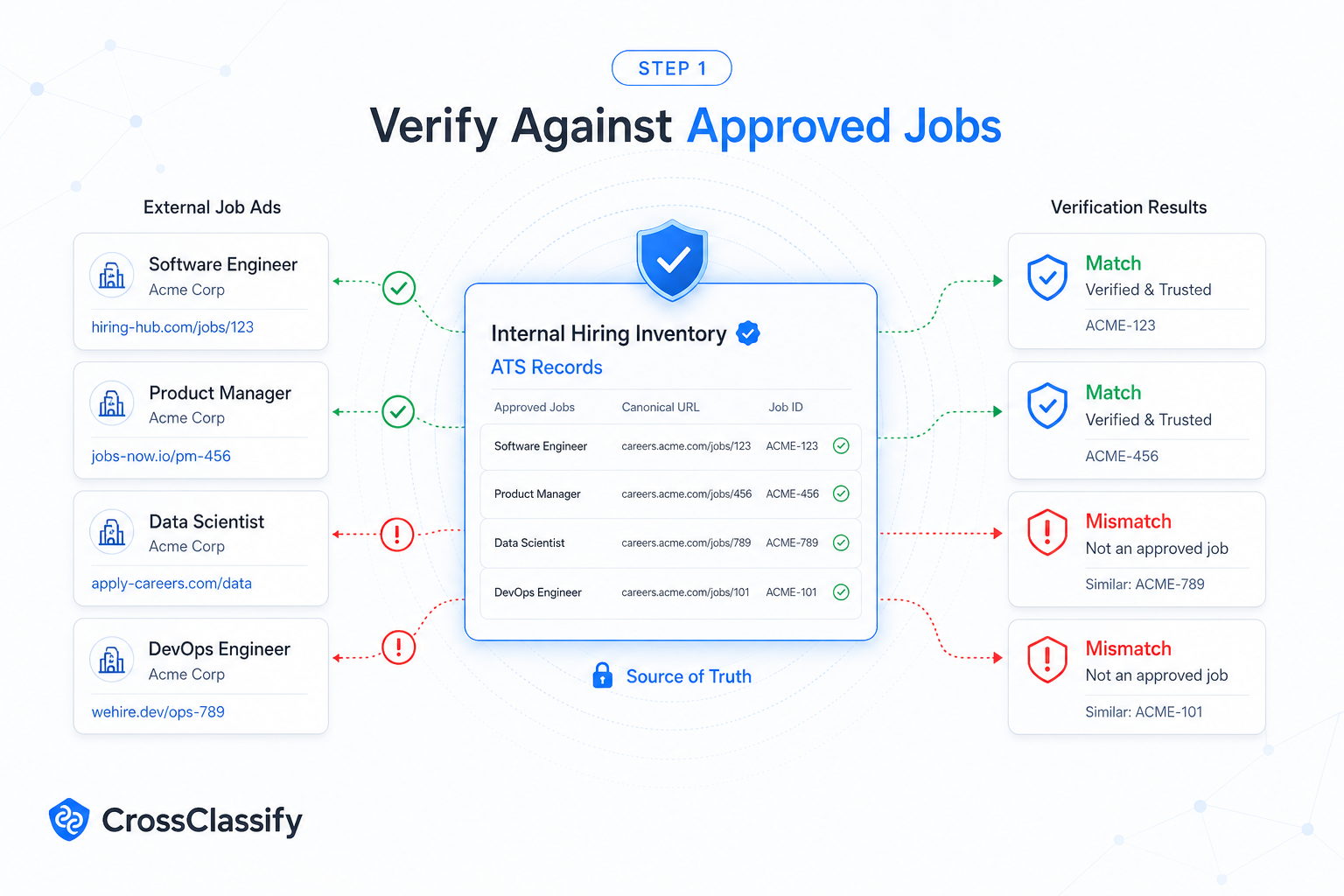
Without this source of truth, every external listing becomes a debate.
CrossClassify’s Authorized Job Ad Verification connects external monitoring to internal job records. When a public listing appears, the platform checks whether the job matches an approved record and whether the application path is trusted.
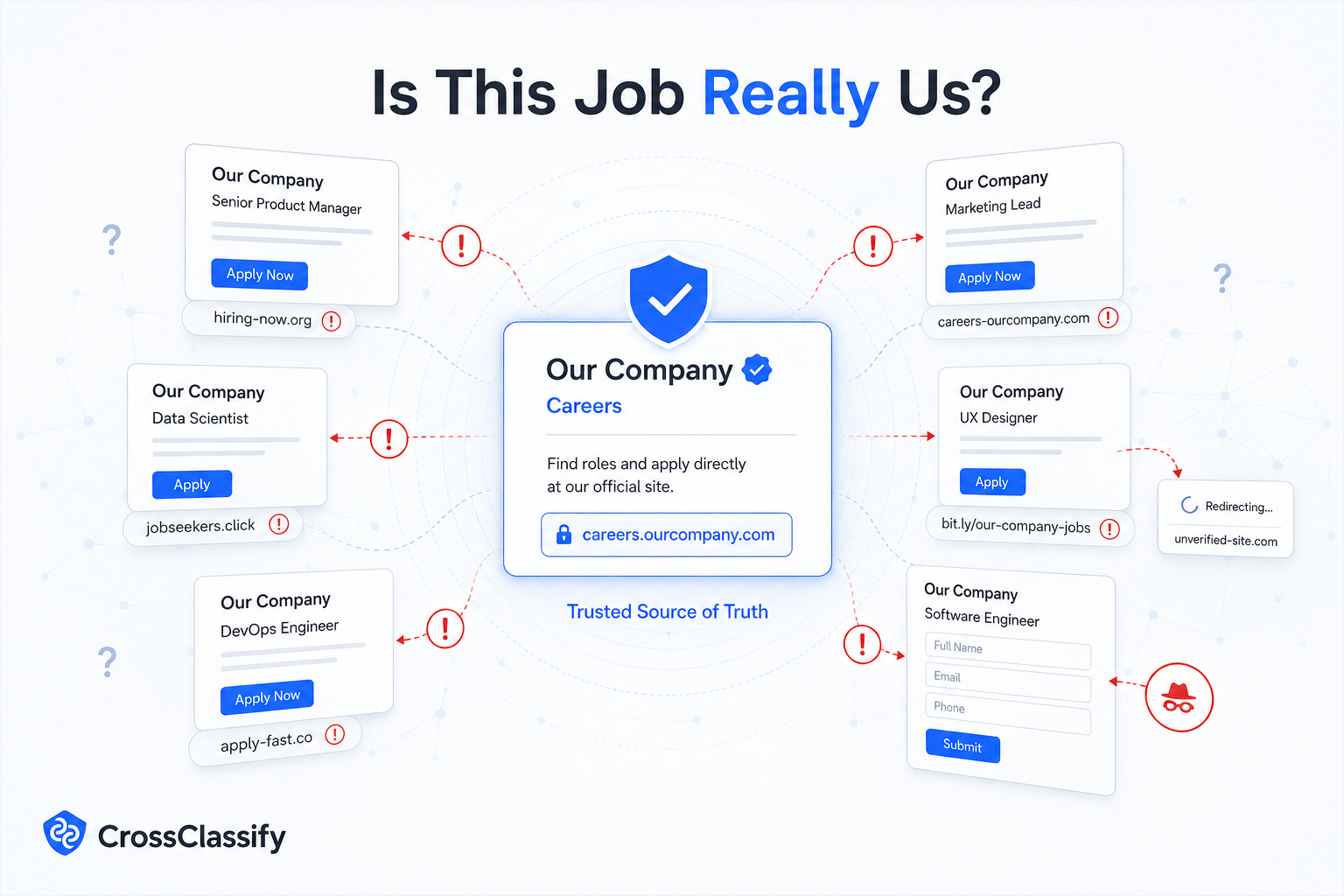
Step 2: Monitor company names and brand variants
Attackers may not use only the main company name.
They may use DBA names, acquired company names, local branch names, product brands, abbreviations, recruiter names, and common misspellings. A useful monitoring system must understand the full brand map.

CrossClassify’s Recruitment Brand Monitoring can track these variants and connect them to approved hiring sources. This helps enterprises detect brand abuse across job boards, social channels, and recruitment marketplaces.
This is especially useful for companies that already use CrossClassify account takeover protection to protect internal portals and user accounts. Recruitment brand abuse and account abuse often overlap when attackers compromise recruiter accounts or create lookalike profiles.
Step 3: Compare job descriptions against approved content
Copied job descriptions are a common signal.
If a job ad uses your exact description but points to an unapproved application form, that is suspicious. If the salary range is unrealistic compared with the approved role, that is suspicious. If the job location or remote work promise does not match the original, that is suspicious.
CrossClassify compares public job text against approved job records and flags mismatches that matter.
The goal is not to flag every variation. The goal is to identify differences that increase fraud risk, such as changed application links, unauthorized recruiter contacts, paid training language, identity document requests, or suspicious onboarding steps.
Step 4: Verify the application destination
The application destination is one of the most important signals.
A fake job ad may look legitimate until the candidate clicks apply. The link may lead to a fake form, a personal email address, a messaging app, a file sharing page, or a cloned hiring portal.
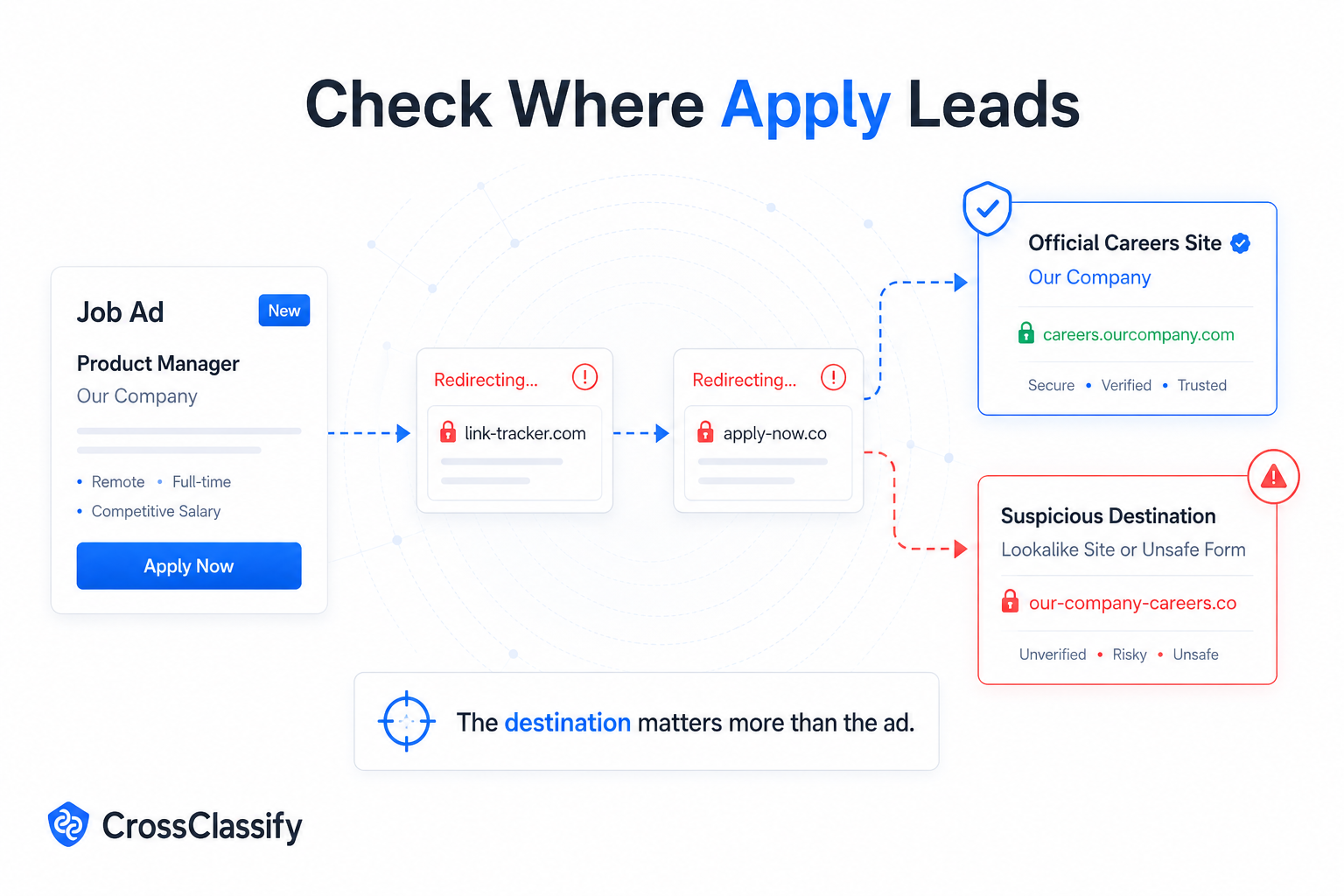
CrossClassify checks whether the application URL matches approved domains, ATS links, career site links, and partner systems. It can also flag suspicious redirects, newly created domains, risky forms, and untrusted collection flows.
This connects naturally with CrossClassify bot attack protection, because fake job campaigns may use automation to create accounts, publish listings, scrape roles, or submit repeated content.
Step 5: Analyze recruiter account behavior
Unauthorized job ads often involve fake or compromised recruiter accounts.
A profile may claim to represent your company. It may use a real employee name. It may message candidates directly. It may post jobs across multiple groups or platforms.
CrossClassify evaluates account behavior, device consistency, browser environment, IP and proxy signals, account velocity, and links between accounts. If multiple recruiter profiles share hidden infrastructure or suspicious patterns, the platform can group them into one campaign.
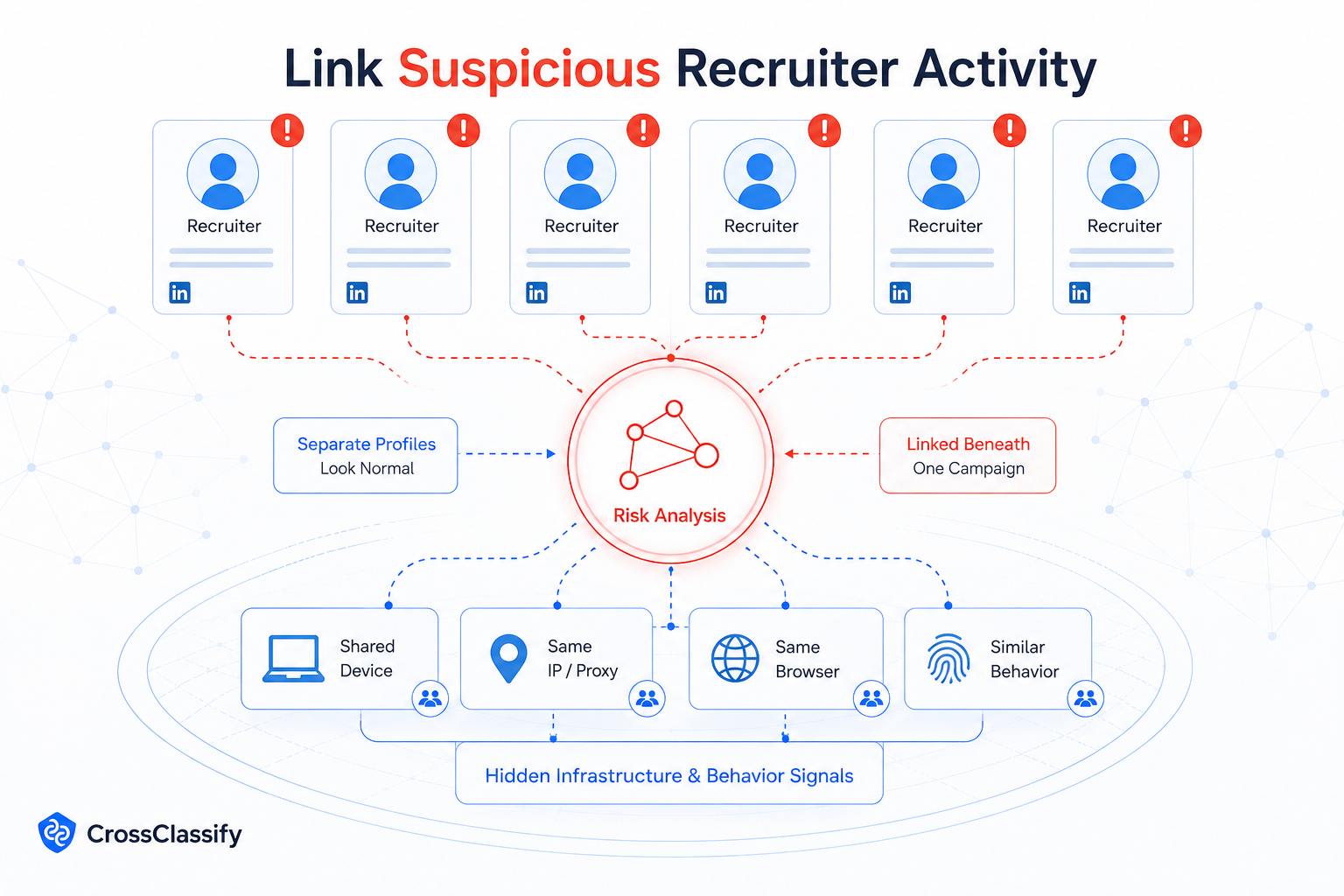
This is where CrossClassify behavioral biometrics adds value. Behavior signals can help distinguish normal recruiter activity from automation, account farms, or coordinated abuse.
Step 6: Create a review workflow
Detection is not enough. Teams need action.
A strong workflow should route alerts to the right owner. Recruitment operations should confirm whether the job is approved. Security should assess impersonation and data theft risk. Brand protection should manage takedown. Legal should support serious cases. Candidate support should prepare a clear response if applicants ask whether the job is real.
CrossClassify provides explainable alerts so each team can see why a listing was flagged. Evidence may include brand match, job text match, missing ATS record, risky application URL, suspicious recruiter account, and related campaign activity.
Conclusion
Unauthorized job ads are a growing enterprise risk because they sit outside one clean ownership lane.
They are part brand abuse, part phishing, part recruitment fraud, part candidate trust problem, and part data protection risk.
The best defense is not manual search. It is verified source control.
CrossClassify helps companies detect unauthorized job ads by connecting public job monitoring with ATS verification, brand intelligence, device signals , recruiter behavior, and human review workflows. This helps security and recruitment teams answer the question candidates care about most.
Is this job really from us?
Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Related articles
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required