Last Updated on 05 May 2026
Fake Job Detection for Glassdoor Style Recruitment Platforms
Share in
Introduction
A fake job posting does not always look fake anymore.
It may use a real company name. It may copy a real job description. It may use a normal title, a believable salary range, and professional language. It may even come from an account that looks established.
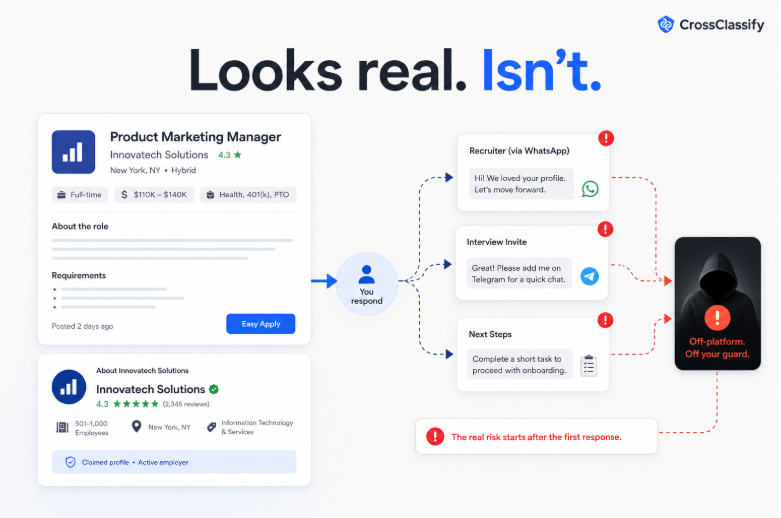
The scam often begins after the candidate responds.
The attacker may move the candidate to text, WhatsApp, Telegram, email, or another channel outside the platform. Then the fake job turns into a fake check scam, a task scam, a request for personal information, or a payment demand.
The FTC warned in April 2026 about fake recruiter text messages offering fake jobs and stealing real money. That matters directly for recruitment marketplaces because fake job discovery often starts in environments where candidates already expect employment related contact.
For platforms like Glassdoor, fake job detection is no longer only a content moderation issue. It is a candidate safety issue, a brand trust issue, and a marketplace integrity issue.
Why fake job scams are hard to catch
A fake job can pass simple checks because the visible content is often copied from real employers.
The title may be normal.
The job description may be copied.
The salary may be attractive but not impossible.
The company name may be real.
The recruiter name may sound credible.
The message may avoid obvious scam words.
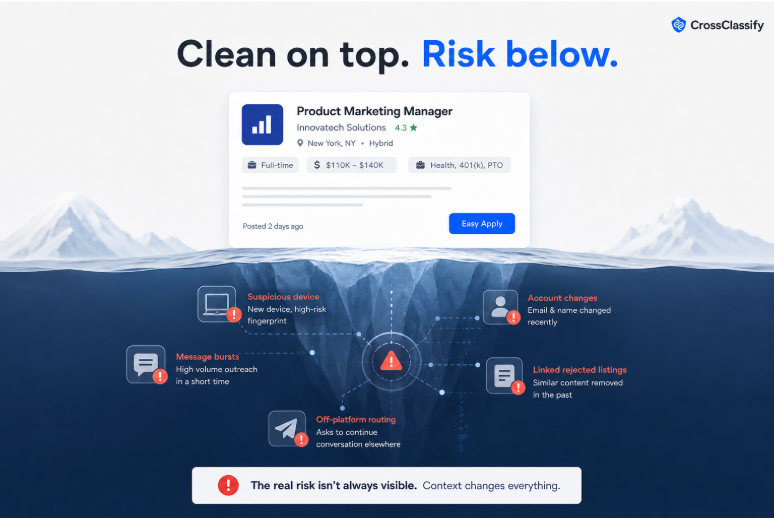
If the platform only evaluates the job text, it may miss the hidden risk.
The suspicious behavior may appear somewhere else. The employer account may have logged in from a new device. The profile may have changed contact details shortly before posting. The recruiter account may be sending many similar messages. The account may be connected to devices already linked to rejected listings. The job may ask candidates to move off platform after the first contact.
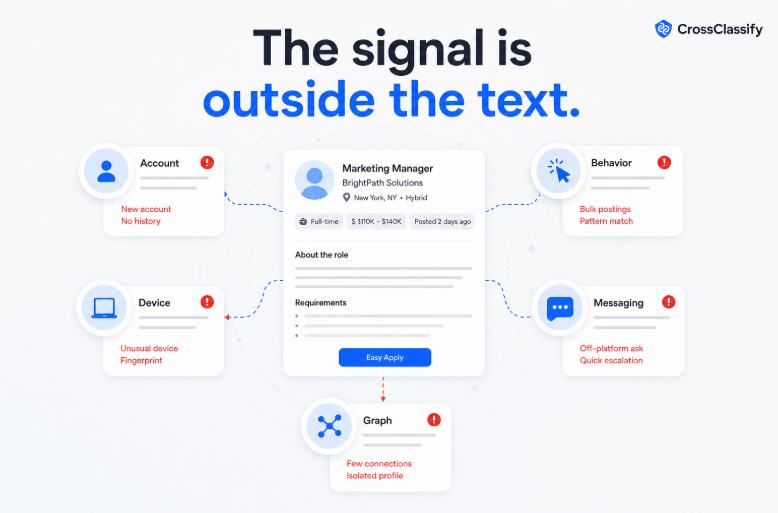
This is why fake job detection needs account, device, behavior, content, and graph intelligence.
The Glassdoor trust problem
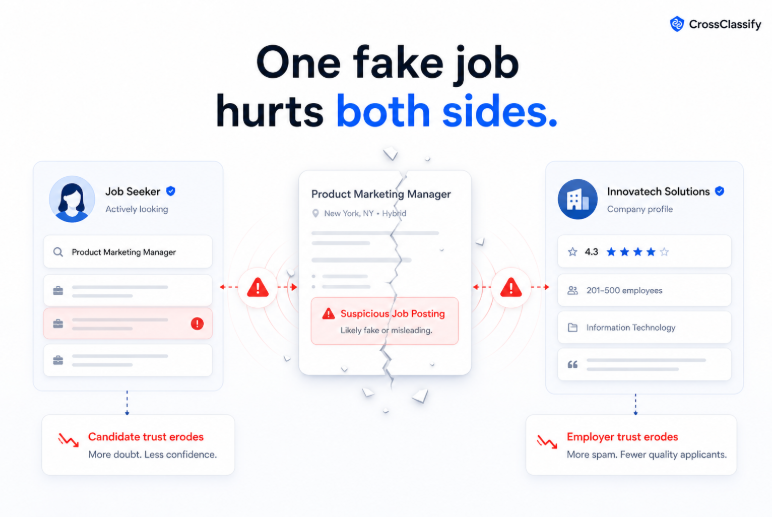
Glassdoor is a trust destination. Candidates use it to evaluate companies, read employee reviews, compare salaries, and search for jobs. When a job scam appears in that environment, the damage can be larger than the individual listing.
The candidate may not separate the scammer from the platform. They may remember that the job was found near a trusted employer profile or during a trusted research journey. That perception matters.
A recruitment marketplace depends on two sided trust. Employers need to believe they are reaching real candidates. Candidates need to believe they are interacting with real employers.
Fake job posts attack both sides at once.
Why CrossClassify is relevant
CrossClassify can help detect fake jobs before candidates are exposed. It does this by scoring risk at the moments where job scams form.
Those moments include employer account creation, employer login, company profile edits, job posting creation, recruiter messaging, contact field changes, and unusual application routing.
CrossClassify’s recruitment solution explains how behavioral analysis and device fingerprinting help verify authenticity across recruitment workflows. That same architecture can be extended to detect suspicious employer behavior, fake recruiter patterns, and scam job posting signals.
CrossClassify’s Job Scam and Recruiter Impersonation Monitor adds a dedicated layer for fake job detection. It evaluates posting behavior, recruiter messaging patterns, external contact requests, employer account trust, device signals, and suspicious account connections.
The signals that expose fake job activity
A strong fake job detection system should inspect several categories of risk.
Employer account risk matters first. A trusted employer account that suddenly logs in from a new device or country, changes profile details, and posts new remote roles may require review.
Job posting behavior matters next. A sudden posting burst, repeated job templates, unusual salary language, vague tasks, and external communication instructions can indicate scam risk.
Recruiter behavior is another key layer. High message velocity, repeated outreach, newly added recruiter users, and attempts to move users off platform can reveal abuse even when the job listing itself looks clean.
Device and network signals are also important. Many fake employer accounts may appear separate while sharing suspicious device fingerprints, browser profiles, proxy patterns, or automation environments.
Graph signals complete the picture. CrossClassify can connect fake employer accounts, recruiter accounts, job posts, devices, review activity, and message flows. The platform can then detect repeat scam operations, not only single suspicious listings.
Why employer account takeover and fake jobs are connected
Some fake jobs are posted from newly created fake employer accounts. Others come from compromised legitimate employer accounts.
The second scenario is especially dangerous because the job inherits trust from the employer profile.
If an attacker takes over a real employer account, the listing may look much more credible. Candidates may be less cautious. The platform may not flag the employer as new. The employer may only discover the issue after candidates complain.
CrossClassify’s account takeover solution combines device fingerprinting, behavioral biometrics, and real time risk scoring to detect suspicious account access. For Glassdoor style platforms, this means employer account protection becomes part of fake job prevention.
Instead of waiting for scam content, the platform can score the risky session before the fake job is posted.
Why fake job detection needs to be low friction
A recruitment platform cannot make every employer go through heavy review for every job post. That would slow legitimate hiring, frustrate employers, and damage revenue.
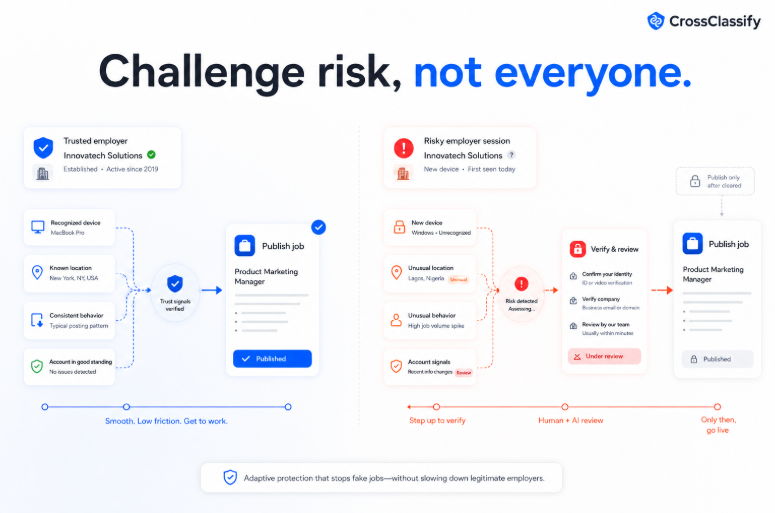
The right approach is adaptive.
A known employer using a familiar device, normal behavior, and typical posting pattern should continue smoothly. A risky session with unusual device, unusual behavior, recent profile changes, and suspicious posting content should face extra review.
CrossClassify supports this risk based model. It can return a score and reason codes. The platform can then decide whether to approve, review, challenge, delay, or block an action.
This is especially important for commercial job boards where employer experience and fraud prevention must work together.
How CrossClassify can integrate into fake job workflows
At employer signup, CrossClassify can score device, behavior, velocity, and identity risk. If a fake employer account appears suspicious, it can be reviewed before it posts.
At employer login, CrossClassify can compare the current session to known employer behavior. If the session looks risky, the platform can require additional verification.
At job posting, CrossClassify can combine account trust, device trust, content risk, and historical behavior.
At recruiter messaging, CrossClassify can detect suspicious outreach velocity, repeated templates, external contact requests, and account graph links.
At report review, CrossClassify can help trust teams investigate by showing why a listing, account, or recruiter pattern is suspicious.
This creates a practical operating model. The platform does not need to block everything. It can create graduated decisions.
What this means for Glassdoor style platforms
Fake job detection should not be positioned only as scam prevention. It should be positioned as candidate trust protection.
Candidates come to Glassdoor style platforms during vulnerable moments. They may be unhappy at work. They may need income. They may be relocating. They may be comparing offers. A fake job scam can exploit that moment.
A platform that protects users from fake jobs earns more trust than a platform that only removes scams after users report them.
CrossClassify helps recruitment platforms move from reactive takedown to proactive risk detection.
Conclusion
Fake jobs are becoming harder to detect because they often look legitimate on the surface. The real signals live in account behavior, device history, recruiter messaging, profile changes, and graph connections.
CrossClassify’s Job Scam and Recruiter Impersonation Monitor gives Glassdoor style platforms a practical way to detect fake jobs earlier, protect candidates, reduce scam reports, and preserve marketplace trust.
The goal is simple. Real employers should post smoothly. Scam operators should be detected before candidates are exposed.
Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Related articles
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required



