Last Updated on 31 Mar 2026
OWASP A07:2025 Authentication Failures Prevention Guide
Share in

Introduction
OWASP Top 10:2025 remains the clearest industry baseline for understanding the most important web application risks that repeatedly create real business damage. It is not just a developer checklist. It is a decision making framework for product leaders, security teams, fraud teams, and compliance owners who need to understand which weaknesses translate into data loss, account abuse, customer churn, and regulatory exposure.
Within that list, A07:2025 Authentication Failures keeps its number seven position and maps to 36 CWEs, with 1,120,673 total occurrences and 7,147 total CVEs in OWASP's 2025 dataset. OWASP's own description makes clear that this category is broader than passwords alone. It includes credential stuffing, brute force abuse, weak recovery flows, missing or ineffective MFA, exposed session identifiers, poor session invalidation, and misuse of tokens or credential scope.
The business urgency is easy to see in current breach data. Verizon's 2025 DBIR says compromised credentials were the initial access vector in 22 percent of breaches, and its supporting research notes that in the median case only 49 percent of a user's passwords across services were distinct. That means password reuse and account level trust failures are still feeding real intrusions at scale, even when organizations believe their perimeter or login stack is "good enough."
That is why OWASP authentication failures prevention, credential stuffing prevention, account takeover protection, and device fingerprinting for authentication security have become commercial and operational priorities rather than optional hardening tasks. MFA remains important, but by itself it does not solve session hijacking, stolen cookies, emulator abuse, synthetic account creation, or human operated fraud that passes a valid login. The strongest modern approach is layered: hardened authentication controls first, then continuous monitoring of the account, session, device, and behavior after the login moment.
Top 10:2025 List
•
A01:2025: Broken Access Control. This category is about users doing things they should not be allowed to do, such as viewing, editing, or deleting other users' data. It remains the top risk because authorization mistakes routinely expose sensitive systems and business logic.
•
A02:2025: Security Misconfiguration. This covers dangerous defaults, exposed admin surfaces, weak cloud settings, and poorly hardened platforms. It matters because many breaches happen without sophisticated exploitation at all, only by discovering what was left open.
•
A03:2025: Software Supply Chain Failures. This focuses on trust failures in dependencies, build pipelines, third party packages, and software provenance. It reminds teams that insecure code can enter an environment through vendors and tooling, not only through in house development.
•
A04:2025: Cryptographic Failures. This category deals with weak or misused encryption, poor key handling, and unsafe storage or transmission of sensitive data. It is about confidentiality and integrity failing even when a team believes data is "encrypted."
•
A05:2025: Injection. Injection happens when untrusted input is interpreted as commands or queries. It still matters because one unsafe path can let attackers read, modify, or control critical systems.
•
A06:2025: Insecure Design. This category is about flawed workflows, unsafe assumptions, and missing abuse resistance in product design itself. Clean code cannot compensate for a system that was architected to trust the wrong signals.
•
A07:2025: Authentication Failures. This risk appears when a system recognizes the wrong user as legitimate or lets attackers stay trusted too easily. It includes password abuse, session weakness, recovery flaws, missing MFA, and token misuse, making it directly relevant to account takeover and bot driven fraud.
•
A08:2025: Software or Data Integrity Failures. This covers failures to verify the trustworthiness of code, updates, and data artifacts. It becomes dangerous when systems accept tampered packages, unsigned updates, or unverified data as genuine.
•
A09:2025: Security Logging and Alerting Failures. This category concerns missing visibility, weak detection, and slow incident response. Even strong controls lose value if attacks are not logged, correlated, or escalated fast enough.
•
A10:2025: Mishandling of Exceptional Conditions. This focuses on systems that fail unsafely under errors, overload, race conditions, or rare edge cases. Attackers often look for these stressed states because they expose logic that normal testing misses.
Definition and Causes of Authentication Failures
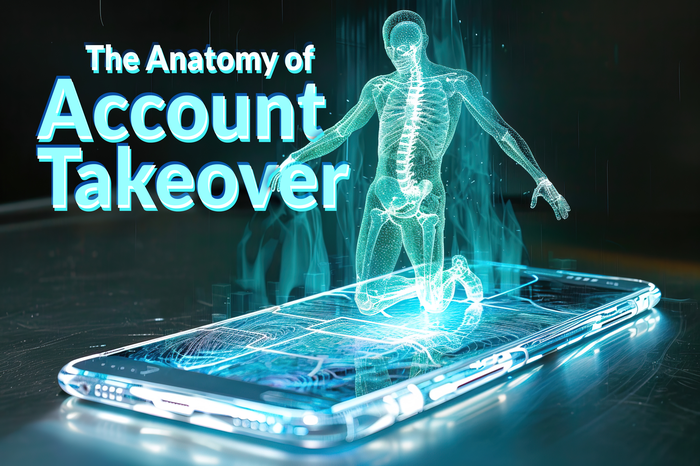
Authentication Failures exist when an attacker can convince a system to accept an invalid identity, a stolen identity, or a still active session as legitimate. OWASP's 2025 definition is intentionally broad because modern authentication abuse is not limited to guessing passwords. It includes situations where the login is technically valid, but the system still places trust in the wrong actor.
OWASP lists a wide range of causes behind this branch. These include automated credential stuffing, brute force attacks that are not throttled quickly enough, default or weak passwords, signups allowed with already breached passwords, unsafe password recovery flows, weak password storage, ineffective MFA, insecure fallback mechanisms, session identifiers exposed to the client in unsafe ways, reused session IDs after login, and sessions or SSO tokens that are not properly invalidated at logout or inactivity. In other words, Authentication Failures are a chain problem involving registration, login, recovery, token use, and session lifecycle management.
The numbers show why this category should concern both security and growth teams. OWASP maps A07 to 36 CWEs and more than 1.12 million occurrences in its 2025 scoring data. Verizon adds the breach lens by showing that compromised credentials were the initial access vector in 22 percent of breaches, which is a strong signal that identity trust remains one of the shortest paths to business damage.
A modern definition of Authentication Failures must also include session trust. OWASP's examples emphasize that even if a password is correct and MFA exists, weak session timeout, weak logout behavior, or broken SSO logout can leave a user effectively authenticated after they think they are done. That is why this OWASP branch overlaps so strongly with account takeover protection, behavioral biometrics fraud prevention, and continuous monitoring of device fingerprints.
Variations of Authentication Failures
Credential stuffing is one of the clearest and most common forms of Authentication Failures. OWASP defines it as automated injection of stolen credentials into login forms, and Cloudflare explains that the attacker relies on users reusing the same credentials across services. Verizon's 2025 research reinforces the scale of this problem by reporting compromised credentials as the initial access vector in 22 percent of breaches and showing how often users still reuse passwords across sites.
This variation matters commercially because it can look like ordinary login traffic until the fraud has already succeeded. It does not require malware on your system or a novel exploit against your app. It only requires that your application remains willing to trust credentials that should no longer be trusted.
Password spraying and hybrid credential attacks
OWASP's 2025 A07 page specifically calls out hybrid credential stuffing and password spray attacks, where attackers adjust likely password variations such as seasonal or incremented passwords. This matters because some organizations still focus too narrowly on classic brute force patterns against one account, while password spraying spreads the attempts across many accounts to avoid lockout controls. It is a quieter trust abuse pattern, not a noisy guessing contest.
This variation also reveals why old password rotation habits can backfire. OWASP's example section says that password rotation and complexity rules, once treated as best practice, can push users toward reused and predictable secrets. NIST 800 63B similarly frames password quality around strong memorized secrets and modern evidence based controls rather than outdated rituals.
Default credentials and weak credentials
Another major variation is use of default, weak, or well known credentials. OWASP explicitly lists default passwords and weak passwords such as "admin" or "Password1" as direct signs of A07 exposure. This is one of the oldest forms of authentication weakness, yet it still creates modern incidents because internet facing devices, consoles, and admin paths are often deployed too quickly or inherited without proper hardening.
Mirai remains the classic real world example. Cloudflare explains that Mirai scanned for vulnerable IoT devices and, if the default username and password had not been changed, it could log in and infect the device. Cloudflare also notes that the Mirai botnet used a hundred thousand hijacked IoT devices in the attack on Dyn, showing how a seemingly "simple" authentication failure can scale into a massive internet event.
Weak recovery and verification flows
Authentication does not end at the login form. OWASP explicitly includes weak password recovery mechanisms, ineffective MFA fallbacks, and poor verification steps during account changes or credential recovery. These are dangerous because attackers often target the easiest trust decision in the identity lifecycle, not necessarily the primary login screen.
The 23andMe enforcement record shows how regulators view this weakness. The ICO said 23andMe failed to implement appropriate authentication and verification measures, including mandatory MFA, secure password protocols, and effective controls over access to raw genetic data. That makes weak recovery and verification a regulatory issue as much as a technical one.
Session fixation, long lived sessions, and weak logout
OWASP includes session fixation, reused session IDs, and poor logout or inactivity handling inside A07 because staying authenticated incorrectly is just as dangerous as logging in incorrectly. OWASP's testing guidance says secure session termination requires visible logout controls, inactivity based termination, and proper invalidation of server side state. The Session Management Cheat Sheet adds that sessions should implement idle and absolute timeouts, enforced server side, to reduce the usefulness of hijacked sessions.
This variation is exactly where many organizations discover the gap between authentication and trust. A user can pass MFA legitimately, but a stolen cookie, a lingering SSO session, or a badly invalidated token can still let an attacker operate as that user afterward. That is why continuous authentication using behavioral biometrics and device fingerprinting for account takeover prevention are becoming essential complements to login time controls.

Real Examples of Authentication Failures
Mirai is one of the most famous examples of Authentication Failures turning into large scale impact. Cloudflare explains that Mirai infected IoT devices when the default username and password had not been changed, then used those compromised devices to form a botnet for DDoS operations. This case matters because it shows how weak authentication is not only an account risk. It can become infrastructure abuse at internet scale.
PayPal and credential stuffing at financial scale
The PayPal incident is a direct example of A07 in a consumer financial context. Maine's breach notice lists 34,942 affected persons and identifies the breach type as credential stuffing. Reuters later reported that New York regulators fined PayPal $2 million and specifically noted that cybercriminals used credential stuffing to view customer tax form data, while PayPal was also criticized for not requiring MFA and controls such as CAPTCHA at the time.
This example is important because it breaks the myth that authentication failures are minor or low sophistication. Financial platforms already know that accounts are high value targets, yet attackers still succeeded by abusing credential reuse and operational gaps around verification controls. In business terms, this is the direct bridge from login abuse to customer data exposure, enforcement action, and reputational loss.
23andMe and the regulatory consequences of reused credentials
23andMe is another strong A07 example because the entry point was credential stuffing, but the impact expanded through connected data features. 23andMe said the attacker accessed roughly 14,000 user accounts through credential stuffing, then used those accounts to access about 5.5 million DNA Relatives profiles and 1.4 million Family Tree profiles. The ICO later said the attack affected 155,592 UK residents and fined the company £2.31 million for failing to implement appropriate authentication and verification measures.
This incident demonstrates a crucial lesson for OWASP authentication failures prevention. Even when the directly compromised account count seems small relative to the total customer base, connected platform features can multiply exposure dramatically. Authentication trust is rarely isolated to one user record anymore. It often unlocks family, payment, identity, or workflow graphs around that user.
Regulatory Compliance of Authentication Failures
Authentication Failures are not only a security engineering problem. They sit directly inside major compliance frameworks because poor authentication exposes personal data, account access, and payment environments. Under GDPR, security is not optional or reactive. Organizations must implement technical and organizational measures appropriate to the risk, and the European Commission's explanation of data protection by design and by default makes clear that privacy and security controls should be built in from the earliest stage, with limited accessibility and privacy protective defaults.
For authentication specifically, GDPR pressure shows up when organizations fail to apply reasonable verification, MFA, password, and monitoring controls for sensitive accounts. The 23andMe ICO enforcement is highly relevant because the regulator explicitly said the company failed to implement appropriate authentication and verification measures, including mandatory MFA, secure password protocols, and effective monitoring and response. That is a strong signal that weak authentication controls can become a direct data protection enforcement issue, not merely a best practice gap.
PCI DSS creates a similar expectation for payment related environments. The PCI Security Standards Council says PCI DSS v4.0.1 includes Requirement 8 updates around MFA, and PCI's guidance on Requirement 8.2.8 explains that reauthentication after 15 minutes of idle time is intended to prevent unauthorized use of unattended sessions. The older but still authoritative Quick Reference materials also frame Requirement 8 as identifying and authenticating access to system components, which directly aligns with A07 concerns such as weak authentication, session handling, and unauthorized reuse of active sessions.
In practice, published GDPR style fines for authentication failures are easier to document than PCI specific penalties. The ICO's £2.31 million fine against 23andMe is a current example tied to credential stuffing and inadequate authentication safeguards. In payments, the more public enforcement example in this set is New York's $2 million settlement with PayPal over cybersecurity failures after a credential stuffing incident; published PCI specific penalties are often handled contractually by card brands and acquiring banks rather than disclosed as a single public regulator fine.
The compliance lesson is simple. If your application handles personal data, financial data, or high risk account actions, authentication cannot be treated as a thin login layer. It must be supported by logging, monitoring, session control, anomaly detection, and evidence that the organization actively manages post login risk. That is where behavioral biometrics for fraud prevention, device fingerprinting for authentication security, and real time alerts strengthen both security and audit readiness.
Protection and Prevention Methods for Authentication Failures
MFA is still one of the strongest baseline controls for reducing password related compromise. OWASP recommends it directly for preventing credential stuffing, brute force, and stolen credential reuse, and the Authentication Cheat Sheet says MFA is the best defense against the majority of password related attacks. The main limitation is that MFA primarily protects the login event, not everything that happens after a compromised session or trusted device context exists.
2. Encourage password managers
OWASP recommends enabling password managers because they reduce reuse and help users create stronger secrets. This matters because Verizon's 2025 credential research still shows how often users reuse passwords across services. Password managers are not a complete defense, but they reduce one of the most persistent fuel sources behind credential stuffing.
3. Remove default credentials completely
OWASP explicitly warns against shipping or deploying with default credentials, especially for admin users. This is one of the simplest and highest value controls because the risk is both old and still very active, as Mirai demonstrated in the real world. When a system starts with known credentials, the organization is effectively publishing a standing invitation to authenticate as an attacker.
4. Block weak and breached passwords
OWASP recommends checking new and changed passwords against weak password lists and known breached credential datasets. NIST 800 63B supports this direction, and Have I Been Pwned provides a practical breached password service designed specifically for this use case. This control matters because it prevents the application from accepting credentials that are already known to attackers before the user even logs in for the first time.
5. Align password policy with modern guidance
OWASP recommends aligning length, complexity, and rotation practices with NIST 800 63B. OWASP's own example section warns that old rotation and complexity rituals can encourage reuse and weak variations rather than real security. Good policy means strong memorized secrets, breached password screening, and rotation only when compromise is suspected, not arbitrary forced churn.
6. Harden registration and recovery against enumeration
OWASP recommends using the same user facing messages for outcomes like invalid username or password, and hardening registration, credential recovery, and API pathways against enumeration. This matters because attackers often begin by discovering which accounts exist and which recovery flows are easiest to abuse. A polished login page with a leaky recovery path is still an Authentication Failure.
7. Throttle, rate limit, and alert on failed logins
OWASP says failed login attempts should be limited or increasingly delayed, while being careful not to create denial of service issues. This is essential for brute force resistance and for making credential stuffing more expensive. However, rate limiting by itself can be bypassed with distributed botnets, proxies, and slower credential abuse patterns.
8. Use secure server side session management
OWASP specifically recommends generating a new random session ID after login, storing it securely in cookies rather than URLs, and invalidating it after logout, idle timeout, and absolute timeout. The Session Management Cheat Sheet reinforces idle and absolute timeouts enforced server side, and the testing guide explains why logout must invalidate server side state rather than simply changing something in the browser. This is one of the most important controls for reducing the damage of session theft.
9. Use well trusted identity systems where possible
OWASP advises using premade and well tested systems for authentication, identity, and session management where feasible. This is sensible because authentication is a deep discipline, and many custom implementations recreate old mistakes around hashing, reset flows, and token handling. Buying or reusing a hardened CIAM or identity layer is often safer than building everything from scratch.
10. Validate JWT audience, issuer, and scope properly
OWASP's A07 page explicitly says teams should verify intended credential use, such as validating aud, iss, and scopes for JWTs. This matters because many modern apps fail not at password entry, but at token handling and trust boundary mistakes between services. A token that is valid in one context should not become a passport everywhere else.

Protection Tools for Authentication Failures
DAST, or Dynamic Application Security Testing, is one of the most useful warm up tools for A07 because it tests the running application from the outside. OWASP's DevSecOps guideline describes DAST as black box testing that can find vulnerabilities in a running application and says it is especially helpful for authentication issues and server configuration mistakes. That makes it valuable for login pages, password reset paths, session handling checks, and insecure error responses.
OWASP's developer guidance also notes that DAST can be manual or automated, and that certain classes of problems, especially business logic issues, may still require human assessment. That limitation is important for Authentication Failures because credential stuffing resistance, session lifecycle flaws, and real world fraud patterns do not always appear as simple scanner findings. A DAST tool can tell you whether an endpoint is weak, but not always whether your trusted user is really the genuine user behind the session.
For practical tooling, OWASP's free tool listing recommends ZAP as a full featured free and open source DAST option. It is a strong starting point for teams that want better coverage of authentication flows, exposed parameters, insecure cookies, session behavior, and input handling in web applications. It should be part of the program, not the whole program.
The best stack for OWASP authentication failures protection usually looks like this: DAST for application level weaknesses, identity platform controls for baseline authentication, rate limiting and logging for attack resistance, and continuous behavioral and device analytics for the post login trust problem. That last layer is where static testing gives way to runtime account protection.
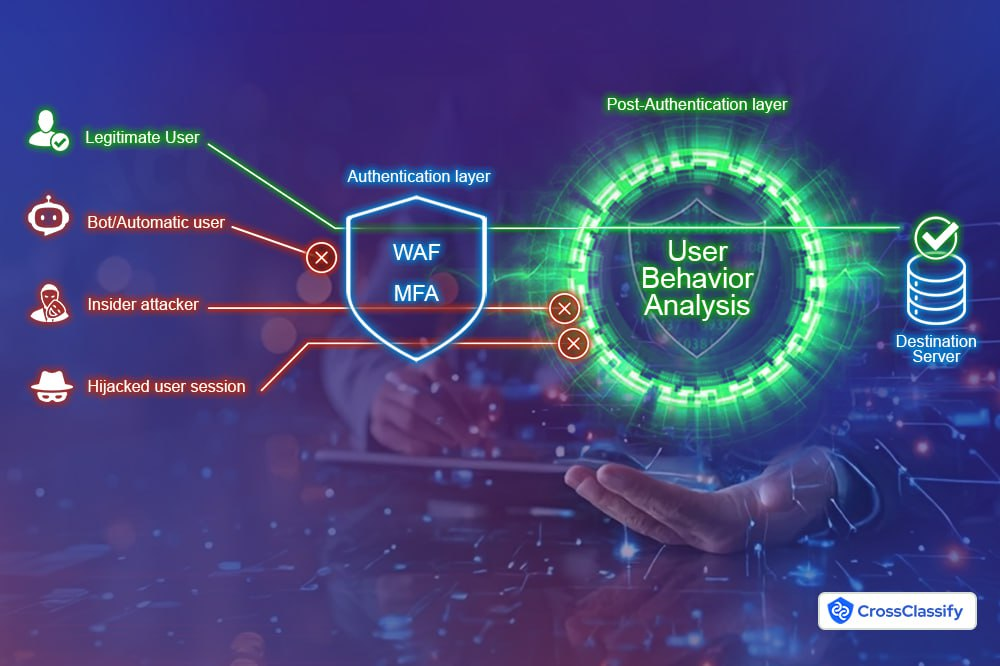
The Gap That Still Exists After MFA and WAF
Here is the strategic gap that matters most for this article. WAF and MFA are necessary, but they are not enough. CrossClassify's own analysis and homepage messaging make this point directly: WAFs help block known web attacks, MFA strengthens login assurance, but both can still miss account takeover, credential stuffing, session hijacking, human fraud, and post login abuse.
That gap exists because modern attacks often happen with apparently valid authentication. A fraudster may use reused credentials, a stolen session, a real device emulator, or a human operated flow that looks normal to a perimeter control. Once that trust boundary is crossed, the application needs another way to decide whether the behavior, device, location, and session pattern still look like the real user.
This is where a pure login mindset fails. Authentication Failures are not just about whether someone got in. They are also about whether the application continues trusting the right actor after login, during profile edits, beneficiary changes, withdrawals, KYC updates, or repeated onboarding attempts. That is exactly why the next step after secure authentication is continuous adaptive trust assessment.

Continuous Monitoring of Device and Behavioral Biometrics
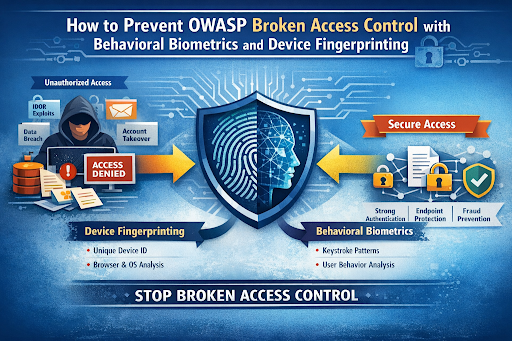
Device fingerprinting gives the platform a persistent identity layer for the machine or environment behind the session. CrossClassify's device fingerprint solution describes continuous device monitoring as correlating hardware and software attributes to build a unique device identity that remains useful even when IPs, browsers, or cookies change. It also highlights use cases highly relevant to A07, including account takeover detection, fake signup blocking, bot and script abuse mitigation, spoofing detection, geo anomaly detection, and device link analysis across fraud rings.
For Authentication Failures, this matters because valid credentials alone should not be enough to reestablish full trust on an unknown or manipulated device. A device fingerprint layer can spot a new emulator, a recycled signup device, a device and region mismatch, or a login from infrastructure that does not match the user's past trust pattern. In commercial terms, this strengthens both account takeover protection and account opening protection without forcing every user through more friction every time.
Continuous monitoring of behavioral biometrics
Behavioral biometrics goes further by modeling how the user interacts, not just which credentials or device are present. CrossClassify describes continuous behavioral monitoring across keystroke dynamics, pointer trajectory, touch pressure, scroll rhythm, accelerometer tilt, micro pauses, and navigation rhythm, with the goal of distinguishing genuine users from impostors, bots, and replayed interaction patterns. That is exactly the kind of runtime evidence MFA and classic login controls cannot provide on their own.
This is especially powerful for A07 because many authentication failures become visible only after a session starts. Credential stuffing may get through, session hijacking may inherit a valid cookie, and a fraudster may pass a challenge. But their cadence, navigation sequence, intent signals, geo velocity, and cross account links often drift away from the real user baseline. Behavioral biometrics adds the continuous confidence layer needed to catch that drift early and act before funds move, data is exported, or more fraud is staged.
Why device intelligence and behavioral intelligence work best together
Used separately, both signals are useful. Used together, they become much harder for attackers to fake consistently. CrossClassify's behavioral biometrics and account takeover pages emphasize this combined model directly, noting that device fingerprinting plus behavioral patterns plus real time risk scoring improve accuracy while reducing false positives and enabling lower friction decisions.
This is the heart of the article's thesis. The strongest protection against OWASP Authentication Failures is not only a better login page. It is a system that keeps verifying trust across the full session, monitors all meaningful activity, raises alerts when normal behavior breaks, and ties the evidence back to the device, account, location, and linked entities involved.
Necessity of Continuous Monitoring of Device Fingerprinting and Behavioral Biometrics
The necessity is practical, not theoretical. OWASP A07 already tells us that authentication can fail through passwords, recovery, MFA gaps, session reuse, and token misuse. CrossClassify's own material then shows why WAF and MFA alone still leave blind spots after the login event. Put together, the lesson is straightforward: trust must be reassessed continuously, not granted once and forgotten.
For application owners, continuous monitoring changes the question from "Did the user authenticate?" to "Does this still look like the same trusted user now?" That is the right question for modern high risk flows such as account recovery, account opening, payout changes, admin actions, profile edits, and value transfer events. It reduces fraud loss while helping legitimate users stay fast because only risky flows are escalated.
For security and compliance teams, this monitoring also improves evidence quality. CrossClassify highlights real time alerting, webhooks, integration with existing controls, and transparent risk scoring, all of which support faster response and better auditability. The bottom line is not just more detection. It is better logging, better monitoring, and better trust decisions throughout the lifecycle of every account and session.
Conclusion
OWASP A07:2025 Authentication Failures is far broader than weak passwords. It covers the full trust lifecycle of an account, from signup and login to recovery, token handling, session timeout, and logout. The official OWASP material, current breach data, and public enforcement actions all point to the same conclusion: authentication is still one of the shortest routes to real business damage.
That is why effective OWASP authentication failures prevention needs layers. Start with strong identity controls such as MFA, breached password screening, secure session management, throttling, and safe recovery. Then close the remaining gap with continuous monitoring that can see what static controls cannot, especially session hijacking, credential reuse, bot driven abuse, synthetic signups, and behavior that no longer matches the real user.
In that layered model, CrossClassify is most compelling where traditional controls lose visibility. Its Behavioral Biometrics solution focuses on continuous authentication, anomaly detection, and real time behavioral risk scoring across the session, while its Device Fingerprint solution focuses on persistent device identity, spoofing resistance, and repeated fraud detection across accounts and sessions. Together they provide a practical path from point in time authentication to continuous trust.
That also aligns well with CrossClassify's Account Takeover and Account Opening solutions, which apply device and behavior intelligence directly to the two fraud domains most tightly connected to A07. If your goal is not just secure login but lower fraud loss, lower false positives, and stronger evidence for action, these linked solution areas are the right place to continue.
Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Related articles
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required