Last Updated on 11 Aug 2025
Defending the Freight Industry Against Fraud and Cybersecurity Threats
Share in

Key Notes
•
Over $800 million in freight fraud losses were reported in the U.S. alone in recent years.•
Insider threats account for nearly 35% of all security incidents in logistics.•
Double brokering scams have risen by over 400% since 2021.
Introduction to the Freight Industry
The freight industry forms the backbone of global commerce, connecting producers to consumers across continents. It encompasses shipping carriers, freight brokers, logistics platforms, and a growing network of digital systems. With increased digitization and interconnected operations, the attack surface for cybercriminals and fraudsters has expanded significantly. Today, freight is not just about trucks and cargo, it involves data, automation, identity verification, compliance, and secure collaboration across the supply chain.
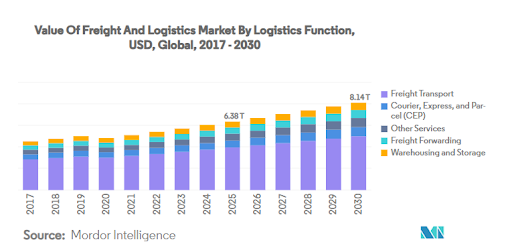
Market Size of the Global Freight and Logistics Sector
The global freight and logistics market is projected to surpass $16 trillion by 2030, driven by e-commerce, global trade, and tech-driven optimization. According to Statista, over 5 million freight companies operate worldwide, with digital freight platforms serving more than 80 countries. Thousands of implementation partners provide fleet management software, TMS solutions, and GPS-integrated tools, but many still lack robust fraud defense mechanisms.
The Alarming Scale of Freight Fraud
Freight fraud is growing in both complexity and scale. In 2023, the U.S. alone recorded more than $800 million in losses due to fraudulent activities in the freight space. Global phishing attacks targeting freight brokers surged by 126%, with scammers spoofing carrier identities and intercepting sensitive logistics data. As the industry embraces digital solutions, fraudsters are exploiting outdated defenses, human errors, and system gaps.
Real-World Cases of Fraud in the Freight Industry
Real-world freight fraud incidents are becoming more frequent and advanced, with bad actors exploiting loopholes in freight management, TMS platforms, and human workflows:
- Double Brokering Scam: A fraudulent actor accepts a load from a broker and re-brokers it to another carrier without disclosure. The original carrier may not get paid, and the load becomes untraceable. This form of scam grew over 400% between 2021 and 2024.
- Carrier Identity Theft: Scammers clone legitimate carrier MC numbers, create fake documents and emails, and impersonate trusted partners. They hijack freight contracts and vanish before delivery.
- Phishing-Based Load Diversion: Criminals use email spoofing to alter load pickup or delivery details, often tricking dispatchers into rerouting trucks based on fake emails or calls.
- Invoice and Settlement Fraud: Fraudsters issue duplicate or fake invoices to payment departments, using forged delivery proofs and bank details to redirect funds.
- Insider Credential Abuse: Temporary employees or subcontractors exploit internal access to reroute loads, share credentials, or download sensitive TMS data before leaving.
The High Cost of Ignoring Cybersecurity in Freight
The freight industry is often reactive rather than proactive when it comes to cybersecurity. However, this delay in adopting security best practices can lead to significant damages:
- Direct Financial Losses: Companies have reported losing millions due to rerouted cargo, unrecoverable loads, legal settlements, and regulatory penalties.
- Reputation and Client Attrition: Carriers or brokers that experience fraud or data breaches often lose long-term clients and market share due to broken trust.
- Operational Chaos: Cyberattacks on route planning tools, GPS trackers, or TMS software can bring entire logistics operations to a standstill.
- Insurance Issues: Failure to implement preventive security measures can disqualify freight businesses from claiming cyber insurance, exposing them to full liability.
- Legal Exposure: A growing number of fraud cases are resulting in lawsuits due to failure to verify identities or protect user access.
Compliance Challenges in Freight and Logistics
Compliance in freight is a growing challenge as regulations become more stringent across countries. The complexity of supply chain networks amplifies this challenge:
- Identity Verification Compliance: Regulatory frameworks like FMCSA, DOT, and CTPAT require verified carrier identity and recordkeeping. Fake MC numbers and impersonation scams violate these mandates.
- Data Privacy and Retention Laws: Freight operations span multiple jurisdictions, requiring adherence to laws like GDPR, CCPA, and cross-border data sharing policies.
- Broker-Carriers Contracts and Chain of Custody: Ensuring signed, traceable agreements with verified parties is vital to preventing fraud disputes.
- ESG and Cyber Readiness Standards: Logistics companies are under pressure to prove resilience and cyber hygiene as part of ESG compliance.

Types of Freight Fraud: Trends, Stats, and Case Studies
Fraud in freight logistics takes many forms. Understanding the patterns helps carriers and brokers develop tailored defenses:
- Double Brokering: Estimated to cost the industry over $500 million annually. Involves accepting a load and reassigning it without broker consent. Often results in unpaid invoices and stolen freight.
- Carrier/Broker Identity Theft: Cloned MC numbers and DOT credentials are used on fake websites, load boards, and email addresses. Attackers fool shippers into assigning real cargo to fake operators.
- Fake Load Boards: Fraudulent online platforms collect real load data and credentials from users, then use them to execute fraud on legitimate boards.
- Phishing Attacks: Email-based fraud aimed at dispatchers and brokers. Victims unknowingly update shipment instructions or vendor details based on spoofed messages.
- Load Diversion and GPS Spoofing: Criminals hijack telematics and ELD devices to mislead tracking systems and delay fraud detection.
- False Invoicing: Fraudulent actors submit multiple invoices for the same load, often exploiting paper-based or poorly monitored settlement systems.
Insider Threats in the Freight Industry: A Silent Risk
Insider threats are among the most damaging yet under-monitored risks in freight. Based on this CrossClassify post, they often arise from lack of visibility and awareness:
- Negligent Insiders: Dispatchers or clerks accidentally fall for phishing, use weak passwords, or share login credentials across systems.
- Malicious Insiders: Disgruntled employees or former partners deliberately reroute cargo, leak access credentials, or manipulate invoices.
- Third-Party Vendor Access: Technology or TMS vendors with weak security protocols can be a backdoor into core freight platforms.
- Shadow Tools and BYOD: Staff using unapproved tools or mobile devices can create unmonitored access to freight and route data.
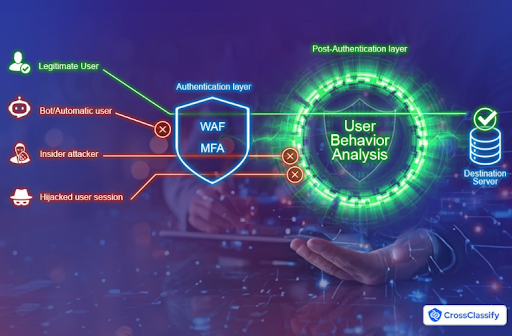
Why MFA and WAF Alone Can't Stop Freight-Specific Cyber Threats
MFA (Multi-Factor Authentication) and WAF (Web Application Firewall) are important but not comprehensive. As highlighted in this article, they fail to address many freight-specific fraud patterns:
- Session Hijacking: MFA tokens can be intercepted or replayed by attackers using phishing kits.
- Credential Stuffing: Freight portals are often targeted by bots using leaked password lists. WAFs rarely stop low-rate credential testing.
- Device Spoofing: Users bypass location restrictions using VPNs or fake GPS, evading both WAF and MFA.
- Insider Exploits: MFA cannot stop a legitimate user with bad intentions. Behavioral indicators are needed.
Emerging Freight-Specific Threats
New threat vectors in freight are closely tied to rising fraud techniques and digital vulnerabilities:
- Freight Broker Identity Theft: Attackers copy logos, register domains similar to real brokers, and use cloned MC numbers to fool shippers.
- Double Brokering Freight Scam: A rampant issue where fraudsters pose as brokers and reassign freight to unsuspecting carriers, then disappear with payment or load.
- Phishing-Based Cargo Theft: Spoofed emails to carriers or dispatchers trick them into rerouting deliveries or updating vendor details.
- Carrier MC Number Spoofing: Criminals create fraudulent paperwork with stolen MC numbers to pass safety audits and win jobs.
- Insider Manipulation in Dispatch Systems: Authorized dispatchers can override routing or payment information undetected.
- AI-Generated Phishing Attacks: Phishing emails crafted using AI tools appear more legitimate and evade filters.
- Cyberattacks on Trucking Fleets: Ransomware, GPS manipulation, and ELD data theft targeting telematics and on-board systems.
- Zero Trust Misconfigurations: Gaps in partial implementations leave lateral access paths open across dispatch and carrier systems.
How CrossClassify Helps Protect Freight Organizations Against Evolving Threats
CrossClassify's AI-driven fraud defense framework is built for the multi-actor, multi-device ecosystem of freight networks. Here's how it helps:
Continuous Monitoring in Freight Networks: Real-time user, session, and device behavior monitoring across TMS systems and load boards. Stop threats before damage. Learn more in this article.
Behavior Analysis for Fleet Access: Profile behavior of brokers, dispatchers, and carriers. Detect unusual routing, access time, or click-path deviations. See this article.
Geo Analysis of Load Access: Track geolocation behavior tied to logins, documents, and dispatch actions. Detect anomalies like remote spoofed access. Read more in this article.
Link Analysis for Broker-Carrier Fraud Rings: Discover relationships between users, devices, and accounts to uncover hidden fraud rings or coordinated double brokering. Refer to this article.
Enhanced Security and Accuracy for Load Verification: AI engines trained on freight fraud patterns minimize false positives while detecting actual load rerouting, MC spoofing, and identity abuse. More in this guide.
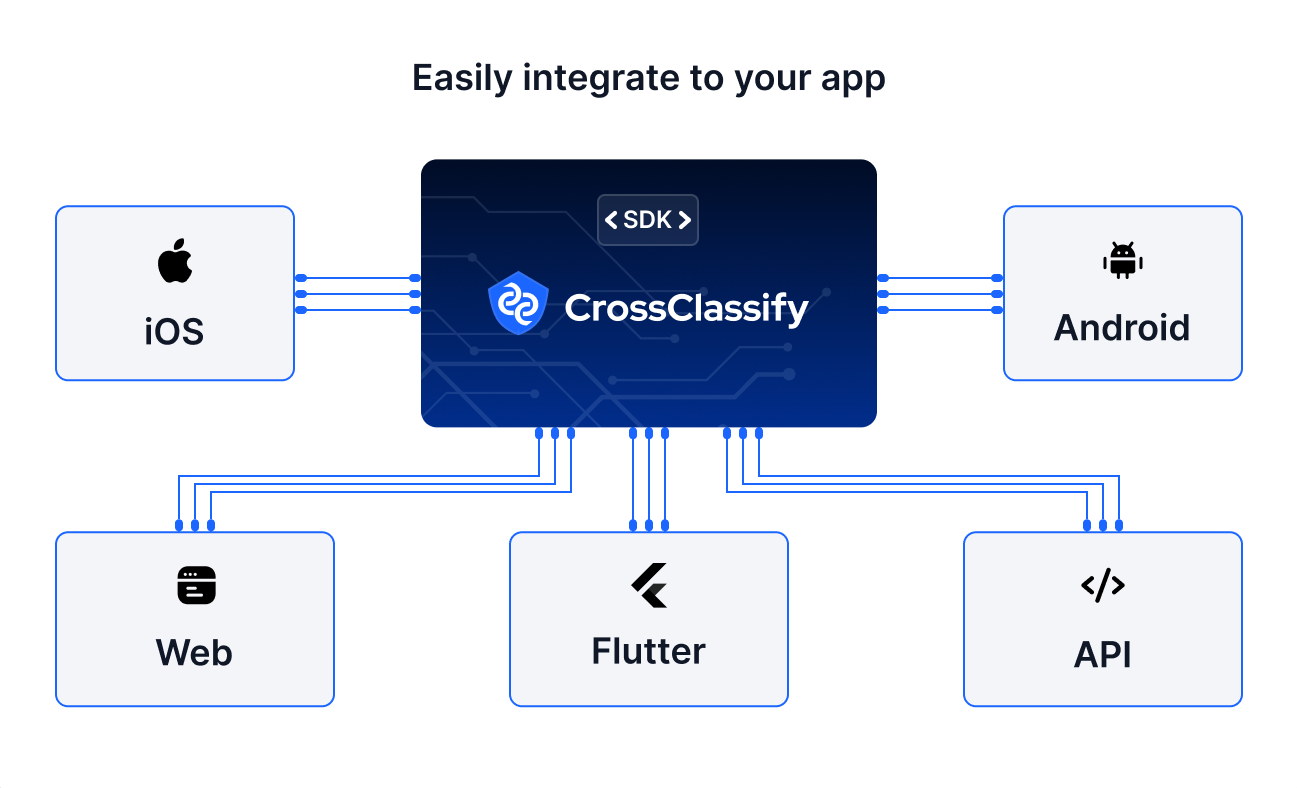
Seamless Integration with Freight Platforms: APIs enable deployment in existing dispatch, carrier, or fleet management tools without friction. Explore integration details.
Alerting and Notification: Real-time alerts based on behavioral anomalies, session manipulation, or spoofed devices. Give dispatchers and security teams immediate context to act.
Continuous Monitoring in Freight Networks: Real-time user, session, and device behavior monitoring across TMS systems and load boards. Stop threats before damage. Learn more in this article.
Behavior Analysis for Fleet Access: Profile behavior of brokers, dispatchers, and carriers. Detect unusual routing, access time, or click-path deviations. See this article.
Geo Analysis of Load Access: Track geolocation behavior tied to logins, documents, and dispatch actions. Detect anomalies like remote spoofed access. Read more in this article.
Link Analysis for Broker-Carrier Fraud Rings: Discover relationships between users, devices, and accounts to uncover hidden fraud rings or coordinated double brokering. Refer to this article.
Enhanced Security and Accuracy for Load Verification: AI engines trained on freight fraud patterns minimize false positives while detecting actual load rerouting, MC spoofing, and identity abuse. More in this guide.
Seamless Integration with Freight Platforms: APIs enable deployment in existing dispatch, carrier, or fleet management tools without friction. Explore integration details.
Alerting and Notification: Real-time alerts based on behavioral anomalies, session manipulation, or spoofed devices. Give dispatchers and security teams immediate context to act.
Conclusion: Building a Secure and Fraud-Resistant Freight Future
Fraud in freight is no longer rare or niche. It's a systematic, organized, and evolving threat. From double brokering to insider threats and AI-driven impersonation, the risks are targeting every part of the supply chain. Relying on legacy firewalls or two-factor authentication is no longer sufficient. Companies must adopt a dynamic, behavior-driven approach to fraud defense.
CrossClassify empowers freight organizations with real-time visibility, advanced analytics, and AI-powered fraud detection tailored to their industry. Its platform addresses the modern freight ecosystem's complexities, identifying bad actors before they inflict damage and giving control back to trusted brokers, carriers, and platforms.
CrossClassify empowers freight organizations with real-time visibility, advanced analytics, and AI-powered fraud detection tailored to their industry. Its platform addresses the modern freight ecosystem's complexities, identifying bad actors before they inflict damage and giving control back to trusted brokers, carriers, and platforms.
Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Frequently asked questions
Account takeover protection in freight systems is essential, as phishing and credential stuffing allow attackers to access TMS dashboards and reroute cargo. CrossClassify defends against this using device fingerprinting, behavioral monitoring, and session intelligence. Learn More →
How to detect double brokering freight scam starts with identifying unusual access and rerouting behavior. CrossClassify uses link analysis and geo-behavioral insights to spot suspicious multi-actor activity across brokers and carriers. Explore the Solution →
Prevent freight broker identity theft by verifying behavioral consistency, device use, and domain activity. CrossClassify identifies cloned MC numbers and login anomalies using fingerprinting and trust scoring. Full Article →
Cargo theft via phishing attacks prevention is urgent, as spoofed emails redirect loads to fraudsters. CrossClassify's behavioral analysis detects abnormal instruction flows and alerts teams in real time. Learn More →
Freight industry insider threat mitigation requires visibility into user actions and intent. CrossClassify flags credential abuse, unusual access patterns, and internal privilege misuse. Learn About Insider Types →
Why MFA and WAF are not enough for freight cybersecurity is clear, these tools miss behavioral anomalies and insider misuse. CrossClassify adds contextual scoring and post-login monitoring to fill the gap. Detailed Explanation →
Carrier MC number spoofing protection involves verifying identity context across sessions and payloads. CrossClassify uses session fingerprinting and network analysis to catch inconsistencies and identity abuse. Explore Fraud Prevention →
AI phishing detection for freight companies stops emails that alter dispatch instructions or payment routing. CrossClassify analyzes content, delivery behavior, and resulting system actions to flag threats. See Detection Methods →
Cybersecurity solutions for trucking fleets should include GPS access protection and session-level analysis. CrossClassify flags spoofed geolocation, manipulated device data, and compromised telematics. Read More Here →
Zero trust architecture for logistics cybersecurity requires dynamic authentication and behavior-driven access control. CrossClassify enables zero trust enforcement by combining device trust, user scoring, and continuous monitoring. Learn How It Works →
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required
