Last Updated on 13 May 2026
Why Domain Monitoring Alone Does Not Stop Fake Job Posting Scams
Share in
Introduction
Domain monitoring is useful.
It can detect lookalike domains, spoofed websites, suspicious MX records, and phishing infrastructure. For many security teams, it is one of the first tools used to protect a brand online.
But fake job posting scams often bypass this layer.
A scammer does not always need to create a fake domain. They can post a fake job on a real job board. They can copy a real job description. They can use a fake recruiter profile. They can move candidates into email, chat, or a fake application form after trust has already been created.
That is why domain monitoring alone does not stop fake job posting scams.
Enterprises need recruitment specific monitoring that verifies whether job ads are authorized, whether application destinations are trusted, and whether recruiter behavior matches legitimate hiring workflows.
CrossClassify fills this gap with recruitment brand monitoring, authorized job ad verification, device fingerprinting, behavioral signals, link analysis, and explainable human review workflows.
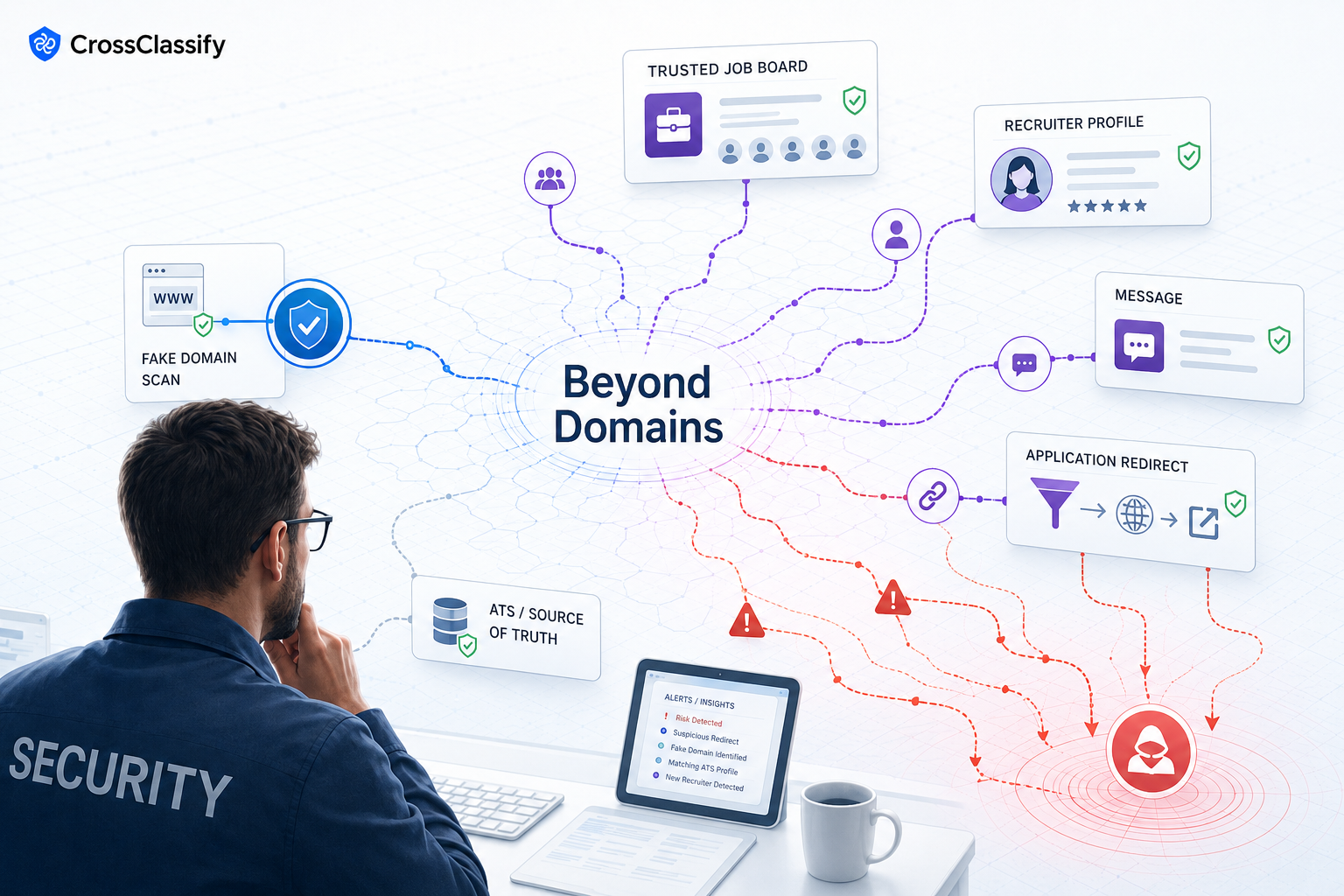
The domain is no longer the whole attack surface
Traditional phishing often depends on a fake domain.
Recruitment impersonation can be different. The fake listing may live on a trusted platform. The candidate may first encounter the scam on LinkedIn, Indeed, a niche job board, a social post, a private message, or a recruiter profile.
The domain appears later, if it appears at all.
This changes the detection problem. Security teams cannot rely only on domain similarity, DNS records, or email authentication. They need to know whether a job post itself is authorized.
The FTC warns that scammers advertise jobs through job sites and social media, which means the recruitment attack surface extends far beyond company owned domains. Consumer Advice
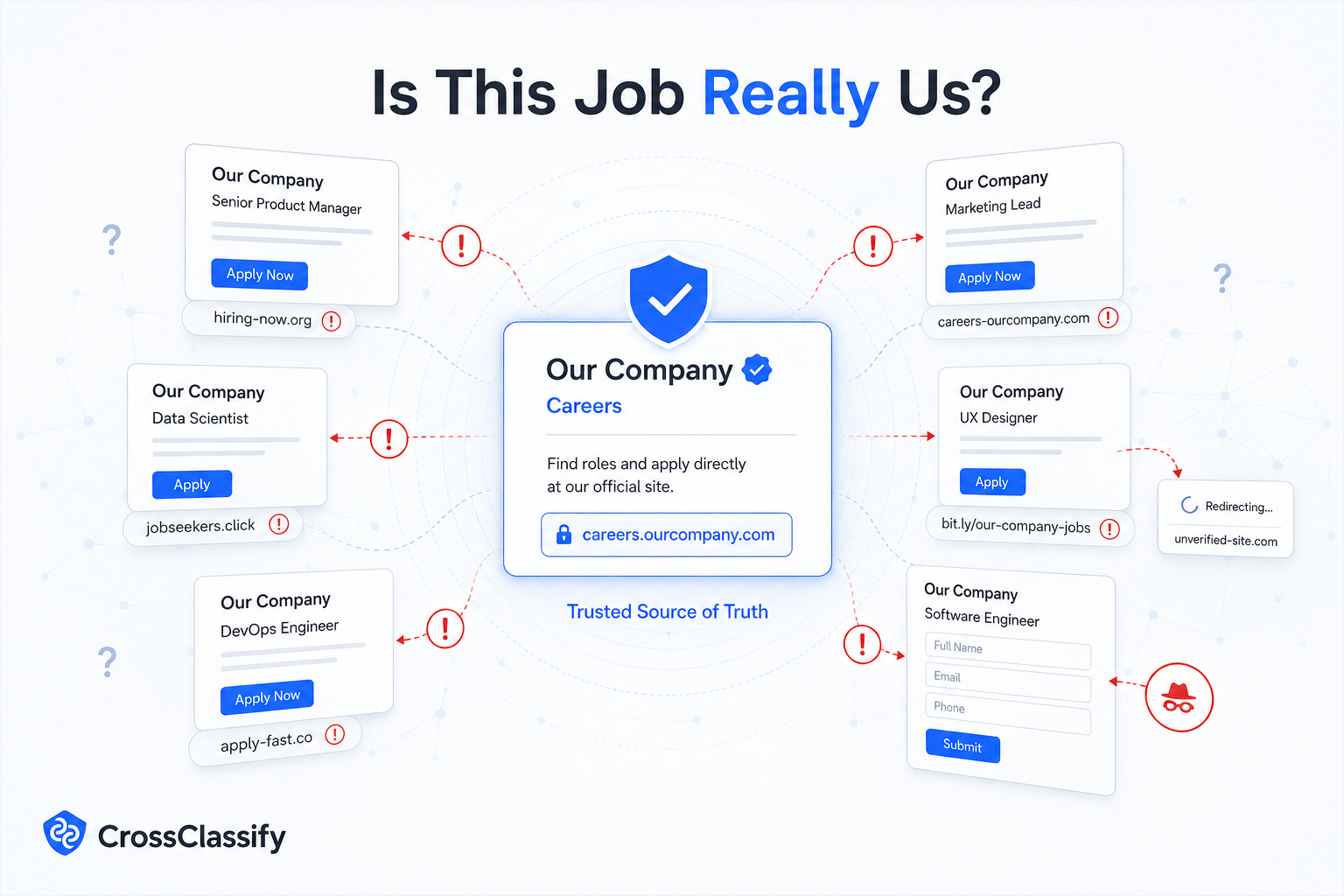
Fake job posts can use real content
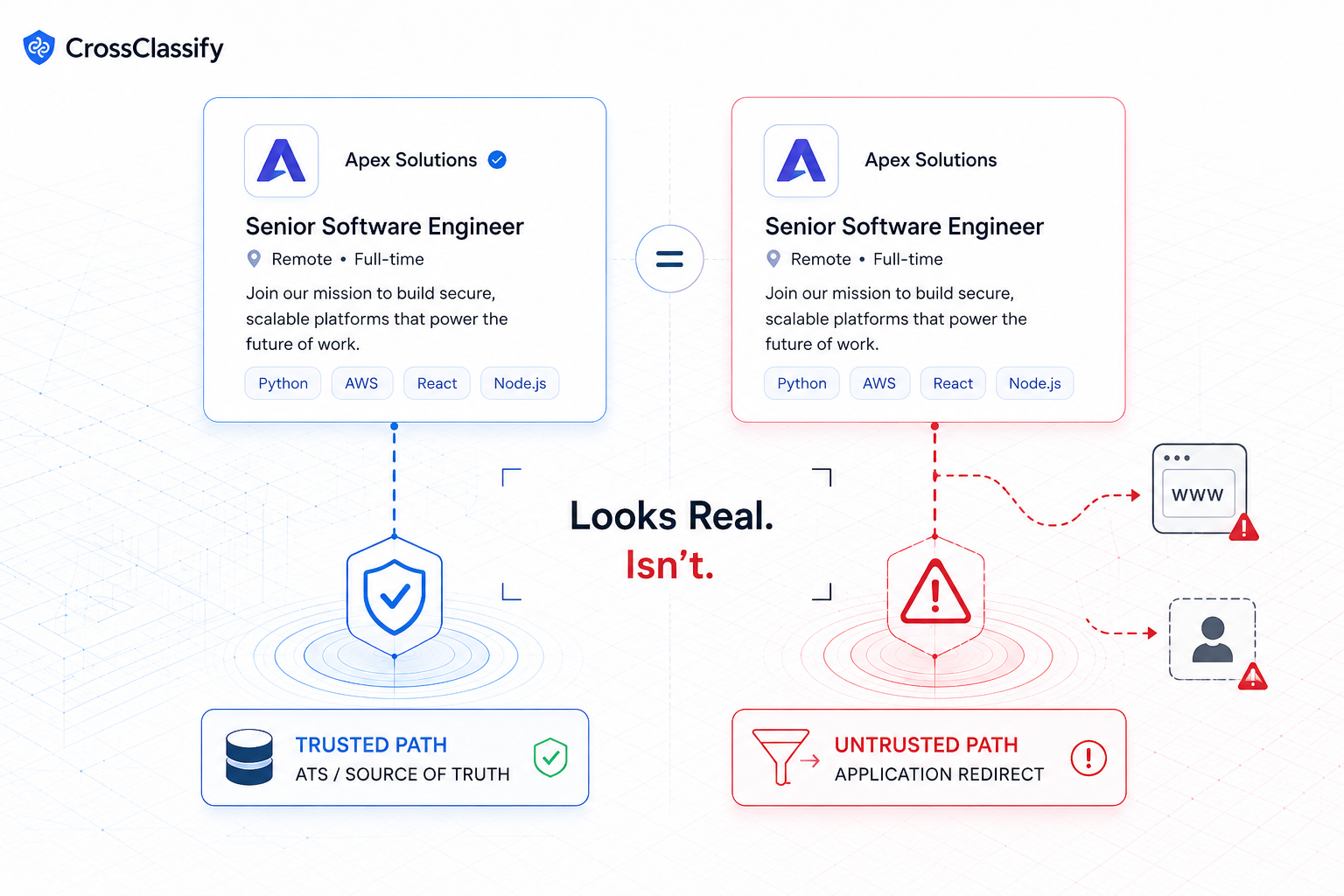
A major weakness of domain monitoring is that it does not inspect job source truth.
A fake job post can copy a real role from the career site and publish it elsewhere. The description may match the company perfectly. The logo may be correct. The location may be correct. The title may be correct.
The problem is not the wording. The problem is that the listing is not connected to an approved hiring flow.
CrossClassify solves this by comparing public job ads against trusted ATS and hiring portal records. It looks for source mismatch, application URL mismatch, recruiter account risk, posting channel risk, and campaign patterns.
This is why CrossClassify recruitment fraud protection is different from simple brand mention monitoring. It evaluates the trust behind the posting, not only the appearance of the posting.
Job board abuse needs platform level signals
A legitimate job board may host a fraudulent listing.
This does not mean the job board is bad. It means attackers abuse open platforms because open platforms are designed for scale. Employer accounts, recruiter profiles, agency accounts, and job posting tools all create entry points.
To detect this abuse, platforms need signals around account creation, device reuse, suspicious browsers, automation, posting velocity, application redirects, and repeated campaign behavior.
CrossClassify can support job boards and recruitment platforms through account opening protection . Fake employer and recruiter accounts can be assessed at creation and monitored over time as they begin posting jobs or contacting candidates.
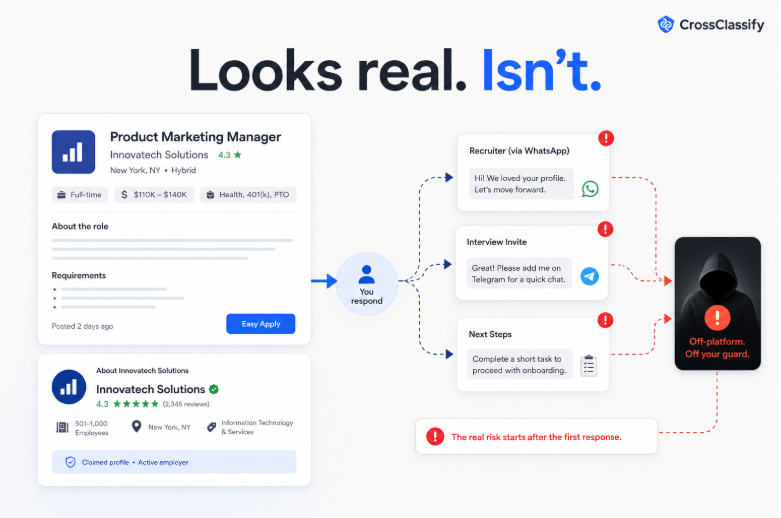
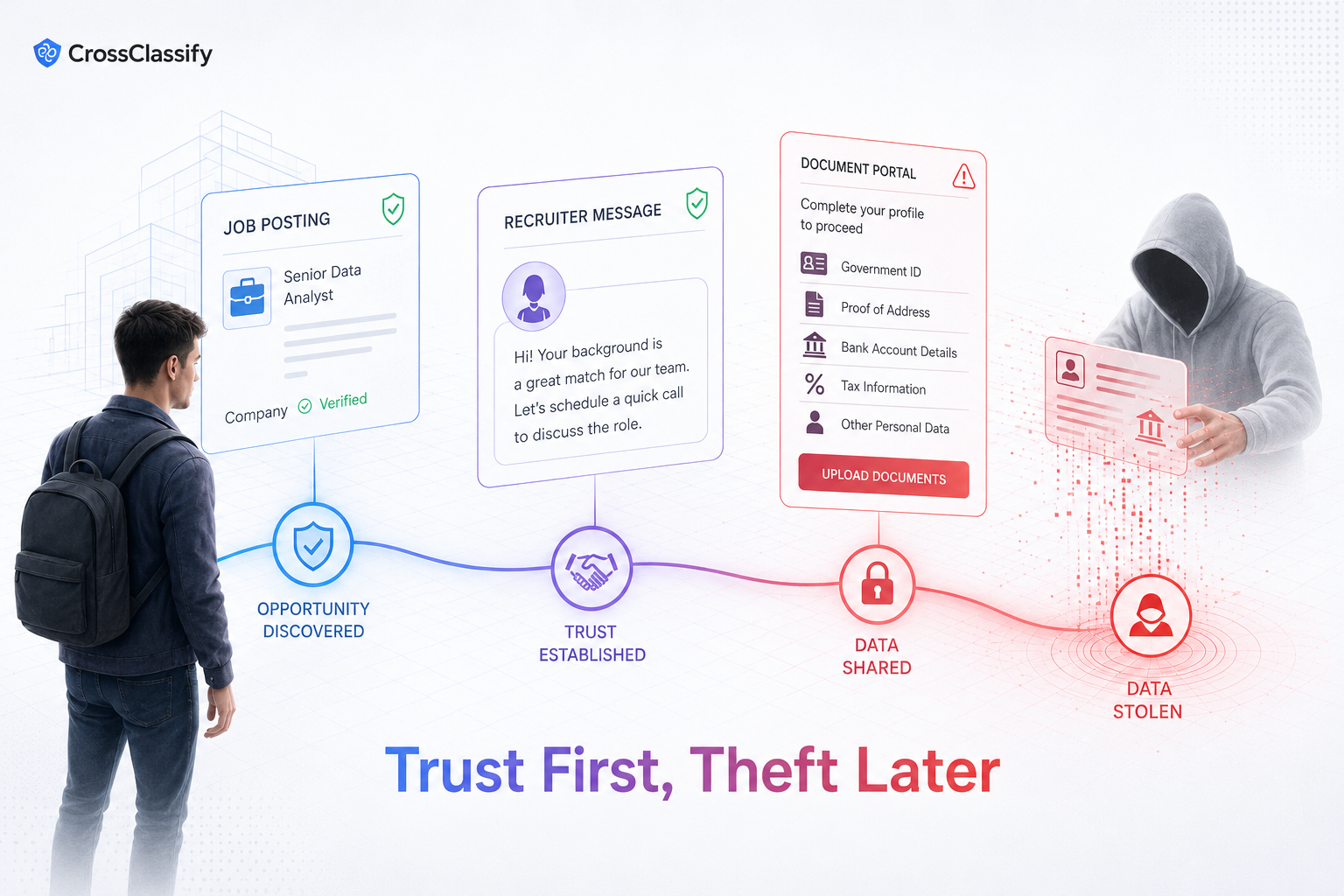
Candidate PII theft happens after trust is created
The most damaging moment may happen after the candidate believes the job is real.
Once trust is created, the scammer can ask for resumes, identity documents, bank information, home address, tax information, or paid training fees. Some scams may also ask candidates to buy equipment or software.
Domain monitoring may not catch this if the conversation moves through messaging apps, personal emails, or forms hosted on common services.
CrossClassify helps by detecting risky application destinations, suspicious redirects, unusual data collection flows, and campaign links between fake postings.
This connects with CrossClassify device fingerprinting because fraud patterns often repeat across devices, browsers, sessions, and accounts, even when visible identities change.
Why security and recruitment data must be connected
Domain monitoring usually sits with security.
Job inventory usually sits with recruitment operations.
Brand approvals may sit with marketing or legal.
Recruiter permissions may sit inside the ATS or HR tech stack.
Fake job posting scams exploit the gaps between these systems.
A better model connects them. The security team sees external risk. Recruitment operations confirms whether the job is authorized. The ATS provides the source of truth. Brand protection manages escalation. Legal supports serious abuse. Candidate support communicates clearly with affected applicants.
CrossClassify acts as the shared risk intelligence layer across these teams.
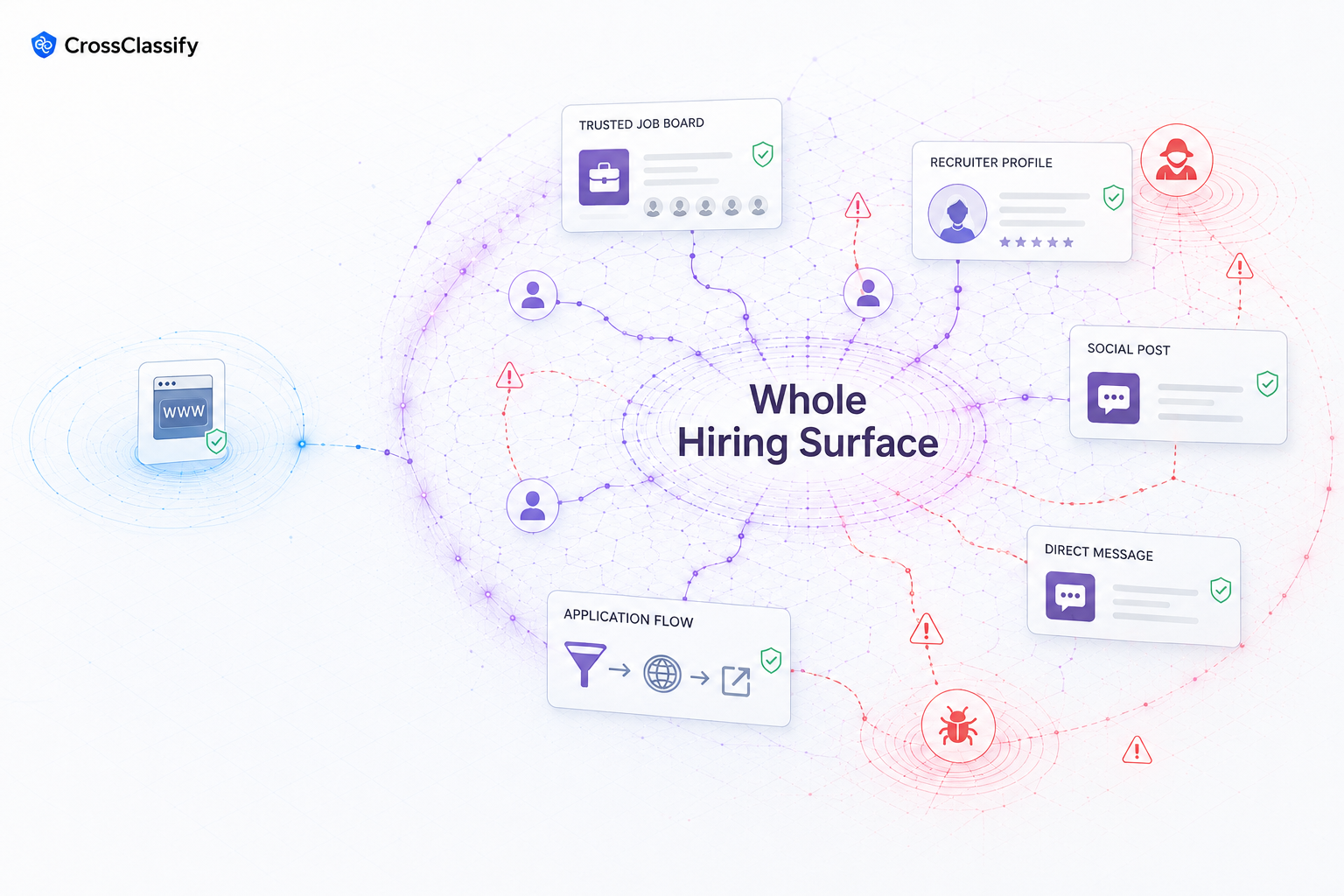
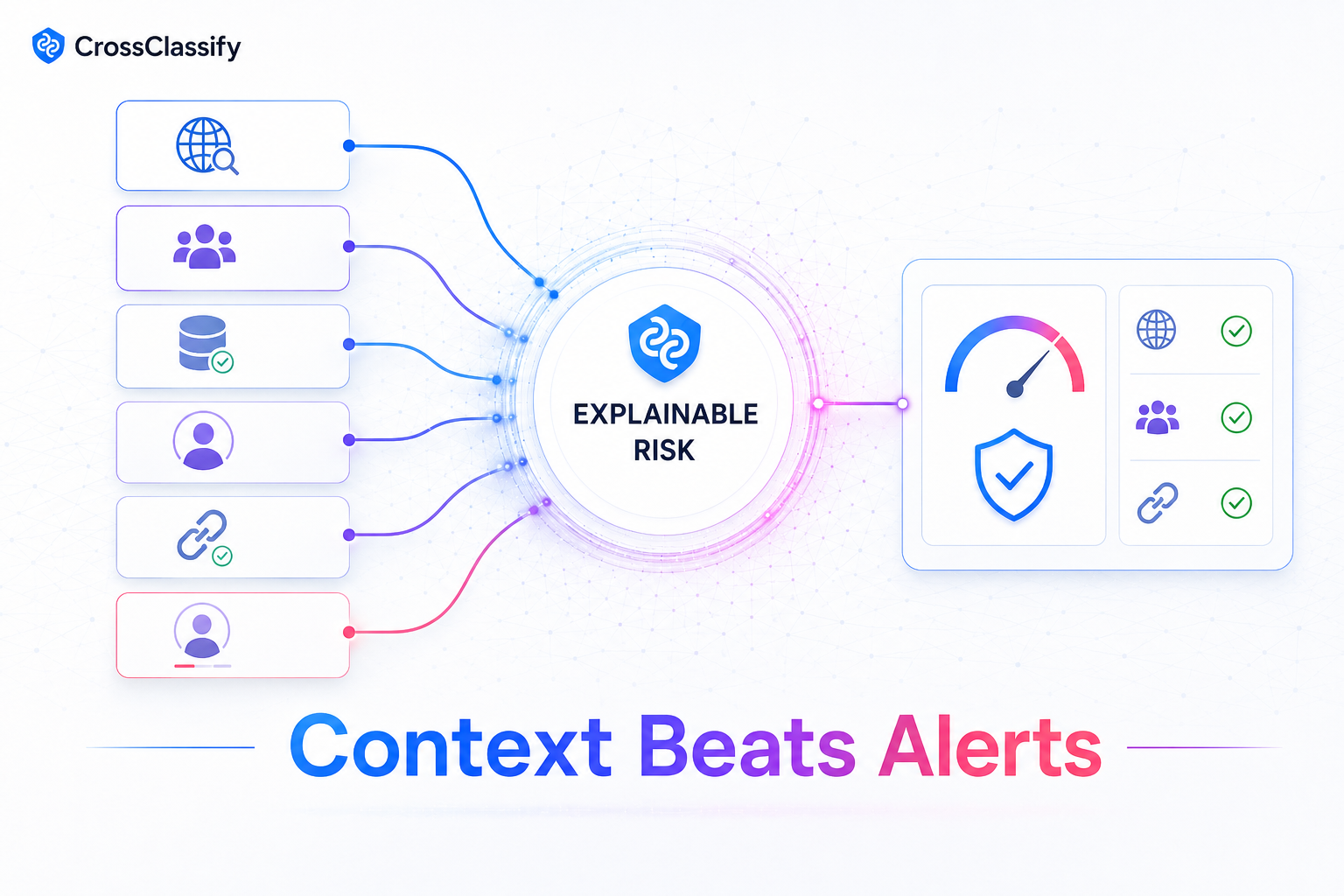
What a better approach looks like
A stronger fake job scam defense includes domain monitoring, but adds recruitment specific verification.
It should monitor company and brand names across public job channels. It should compare job ads against approved ATS records. It should verify application URLs. It should evaluate recruiter account trust. It should detect copied job descriptions that point to untrusted destinations. It should group related fake postings into campaigns. It should produce evidence that humans can review.
CrossClassify’s Recruitment Brand Monitoring and Job Posting Fraud Intelligence Dashboard provide this operating model.
The result is not just more alerts. The result is better context.
Teams can see which listings are likely unauthorized, why they were flagged, what evidence supports the alert, and which workflow should handle the response.
Conclusion
Domain monitoring is necessary, but it is incomplete.
Fake job posting scams can happen on trusted platforms, through copied job descriptions, fake recruiter accounts, and unapproved application paths. The domain may not be the first signal, and sometimes it may not be the main signal at all.
CrossClassify helps enterprises, recruitment platforms, ATS systems, and job boards close this gap with job source verification, recruitment brand monitoring, behavioral intelligence, device signals, and human review support.
The future of recruitment brand protection is not only watching domains.
It is verifying trust across the whole hiring surface.
See How CrossClassify Protects Recruitment Platforms
Detect fake recruiters, fraudulent resumes, and job scams instantly

Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Related articles
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required