Last Updated on 14 May 2026
Fraud Detection for MSSPs: The Missing Layer in Customer Facing Security
Share in
Introduction
Many MSSPs already protect endpoints, cloud systems, identity platforms, email, networks, and SIEM environments. That work is still essential. But for customers with customer facing web apps, mobile apps, portals, marketplaces, and account systems, one of the fastest growing risks happens inside the application journey itself.
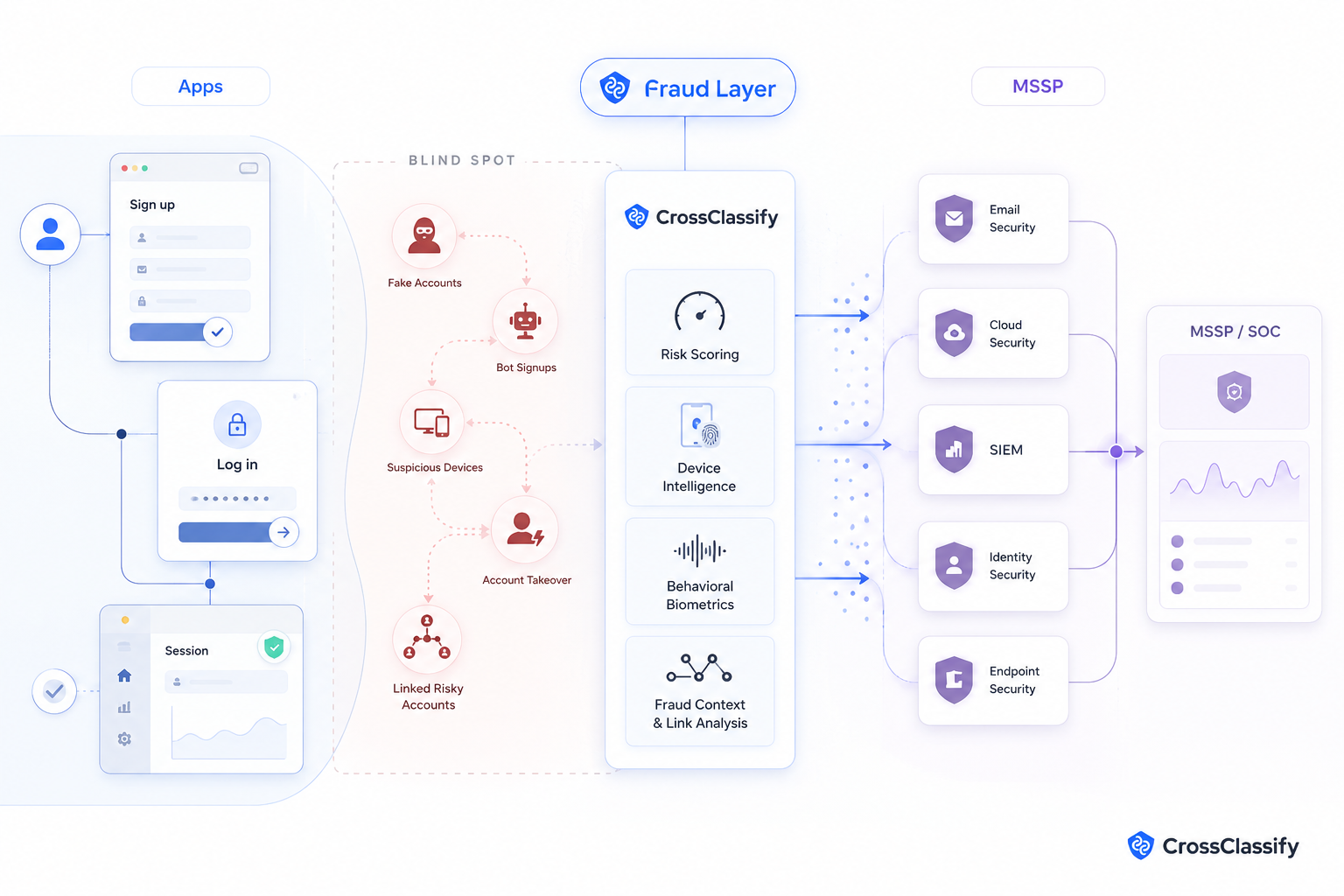
A fake account does not always look like malware. A suspicious device does not always trigger an endpoint alert. A bot signup campaign may never look like a classic intrusion. An account takeover attempt can pass through normal login infrastructure and only become obvious when the behavior, device, location, and account history no longer match.
That is why fraud detection for MSSPs is becoming a serious partner opportunity. The customer already trusts the MSSP to monitor risk. The missing piece is account abuse visibility inside the customer facing product.
CrossClassify gives managed security providers a fraud intelligence, device intelligence, behavioral biometrics, and account abuse detection layer that fits into customer facing digital platforms. It does not replace the SOC, SIEM, MFA, identity provider, fraud analyst, or existing security stack. It enriches those systems with the signals they often do not have.
Why customer facing fraud belongs in the MSSP conversation
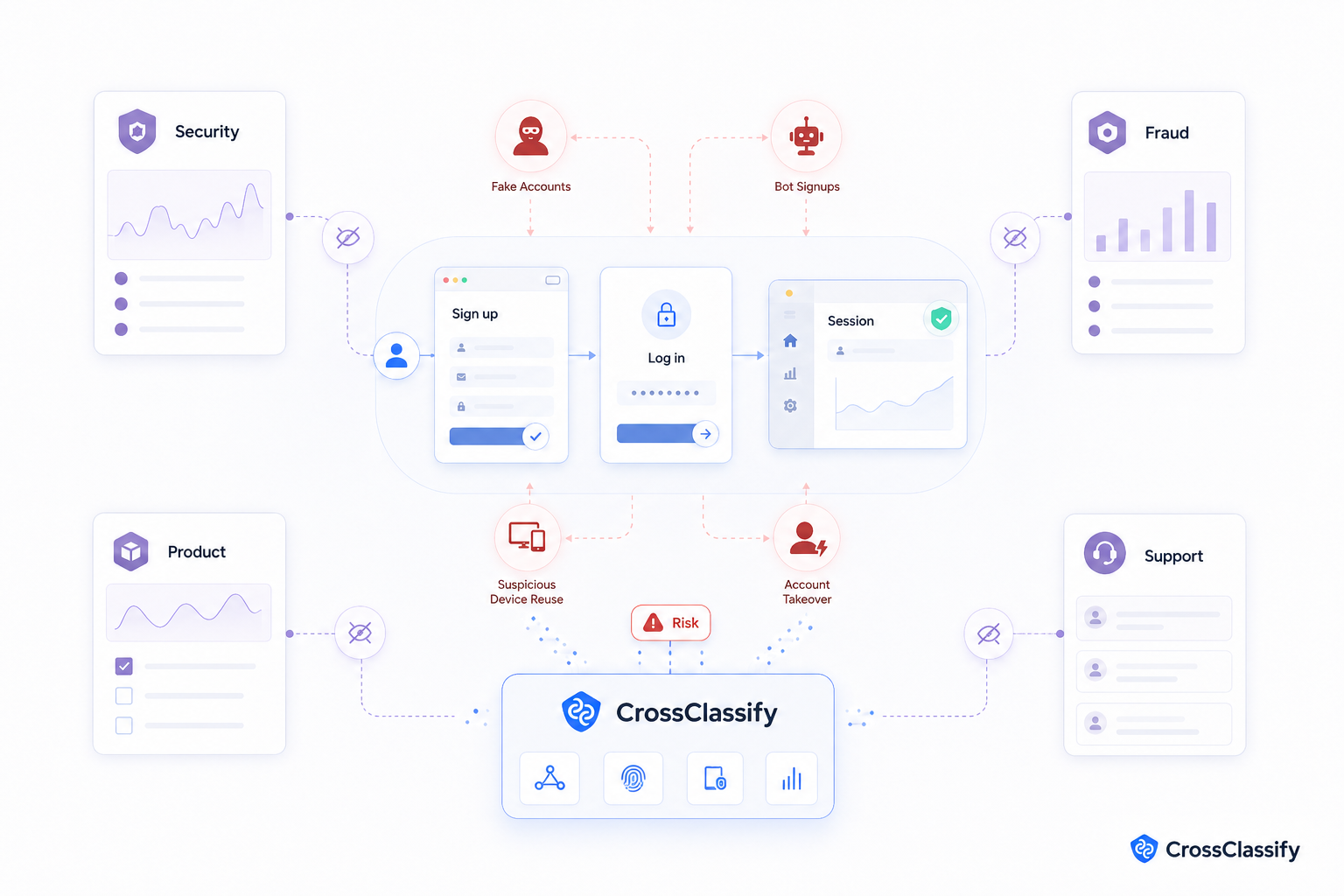
MSSPs are trusted because they help customers see security risk across complex environments. Yet many customers still separate cybersecurity from fraud operations. Security teams watch infrastructure. Fraud teams review suspicious accounts. Product teams worry about conversion and friction. Customer support handles complaints when accounts are abused. The result is a gap where account abuse can grow quietly.
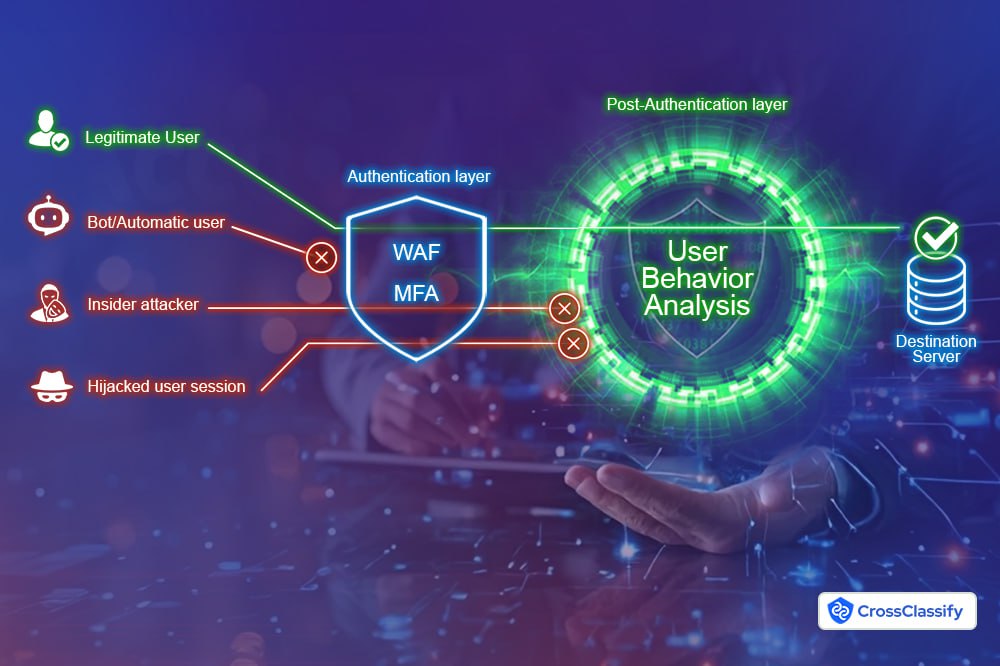
A customer may already have MFA, SIEM, WAF, endpoint security, and email protection. Those tools are useful, but they may not explain why the same device is creating repeated accounts, why a login looks normal at the authentication layer but behaves differently after access, or why multiple accounts share similar device and behavior patterns.
This is where an MSSP can create new value. The partner can help the customer extend security monitoring into signup, login, account recovery, sensitive account changes, web sessions, and mobile sessions.
CrossClassify helps close this gap by monitoring identity, behavior, network, and device signals in real time. It assigns risk scores that help teams detect account takeover, fake account creation, bots, suspicious devices, multi accounting, fraud rings, and abnormal user behavior.
For organizations that need stronger account protection, CrossClassify connects naturally with account takeover protection. That layer helps security and fraud teams evaluate risky login and session behavior with more context than static controls alone.
The MSSP service opportunity
The best MSSP opportunity is not to sell fraud detection as a detached software product. It is to package it as a managed account abuse detection service.
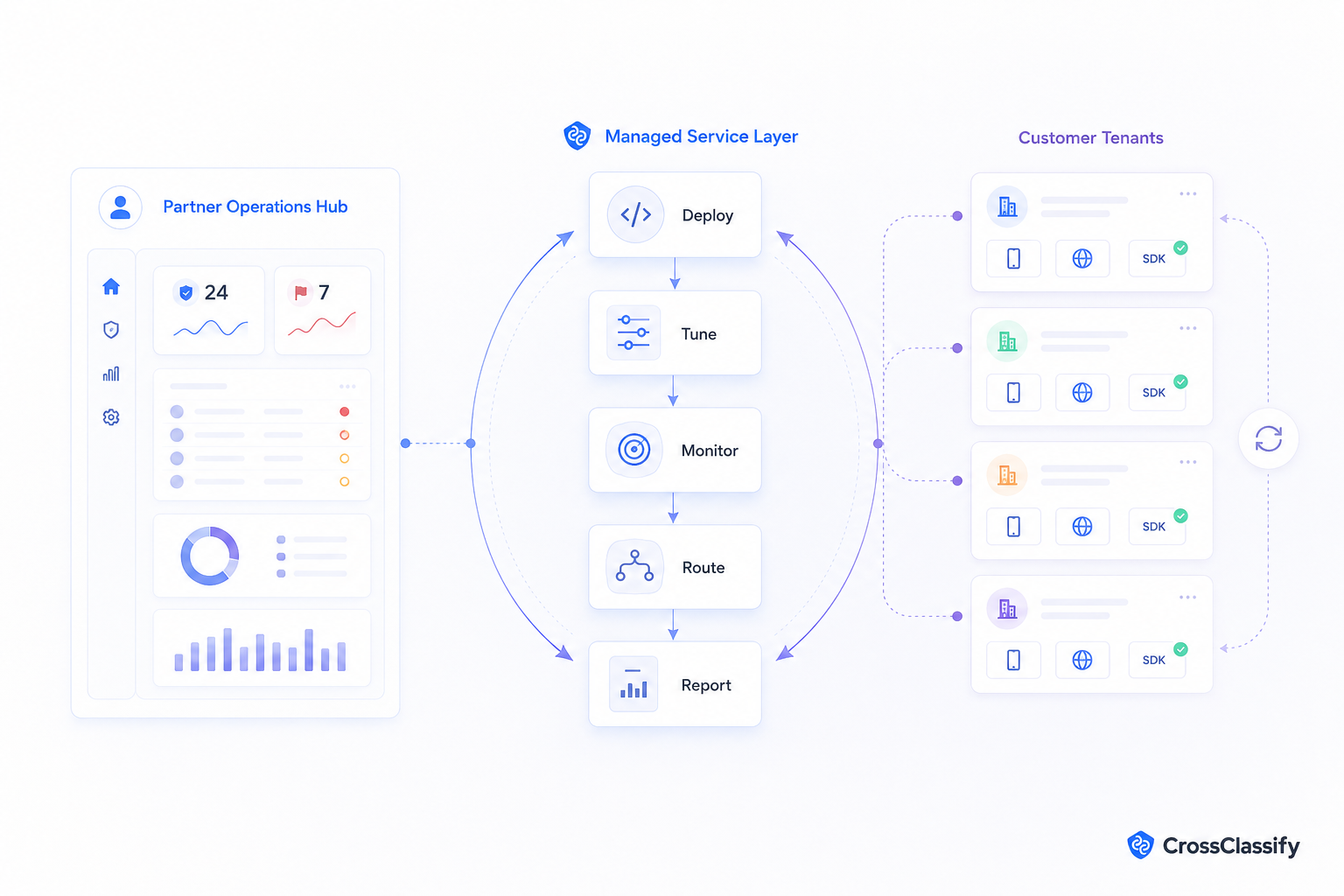
The partner can help the customer deploy SDKs, connect backend risk checks, map events into SOC workflows, create review queues, tune thresholds, and report risk trends each month. This creates recurring value because account abuse is not a one time problem. Fraud patterns change, devices rotate, bots adapt, and attackers test controls continuously.
A strong partner package can include suspicious device monitoring, signup fraud detection, account takeover alerting, bot detection for customer facing apps, fraud risk scoring for SOC teams, and SIEM fraud detection integration.
CrossClassify’s Partner Admin Console, Multi Tenant Customer Management, Managed Fraud Detection Dashboard, and SOC Alert Enrichment Pack make this easier for MSSPs to operationalize. A partner can manage several customers, monitor risk trends, route fraud events into customer workflows, and show monthly evidence of value.
Why SIEM alone is not enough
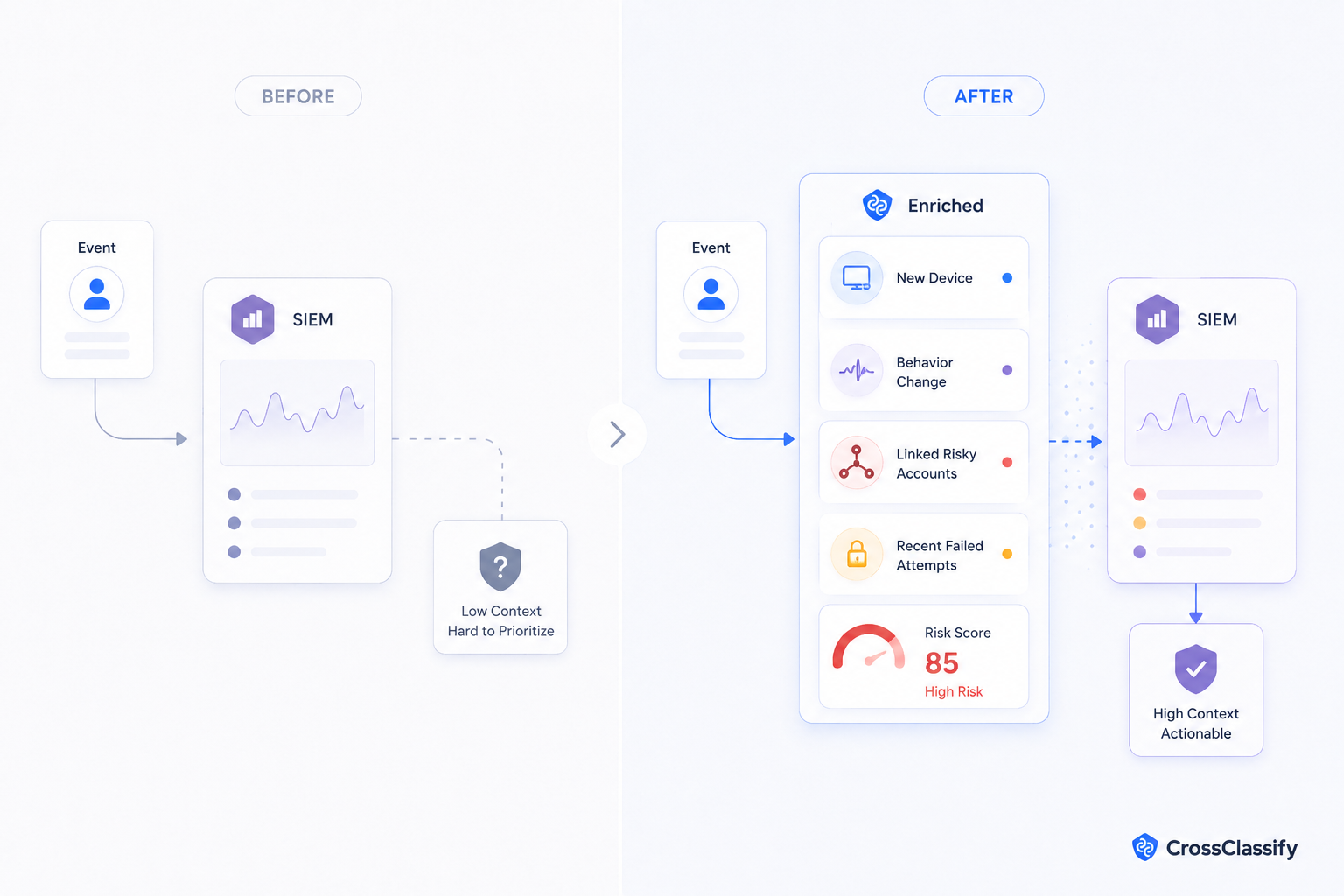
SIEM platforms are powerful for collecting and correlating security events. But a SIEM is only as useful as the context it receives. If it receives a login event without device history, behavioral pattern, account relationship, or fraud risk score, the analyst may not know whether the event matters.
For example, a customer may see a successful login from a known country. On its own, that may not look suspicious. But if the device is new, the behavior pattern changed, the account is linked to several recent failed login attempts, and the same environment has touched other risky accounts, the risk picture changes.
CrossClassify enriches the SOC workflow with fraud signals. Instead of only seeing that a login happened, the customer can see whether the device is suspicious, whether behavior is abnormal, whether the account is linked to other risky accounts, and whether the session matches known abuse patterns.
For customers building deeper device visibility, CrossClassify’s device fingerprinting solution adds persistent device intelligence to web and mobile journeys. This helps teams detect repeat abuse even when attackers change accounts, emails, IP addresses, or browsers.
How MSSPs can package the first use case
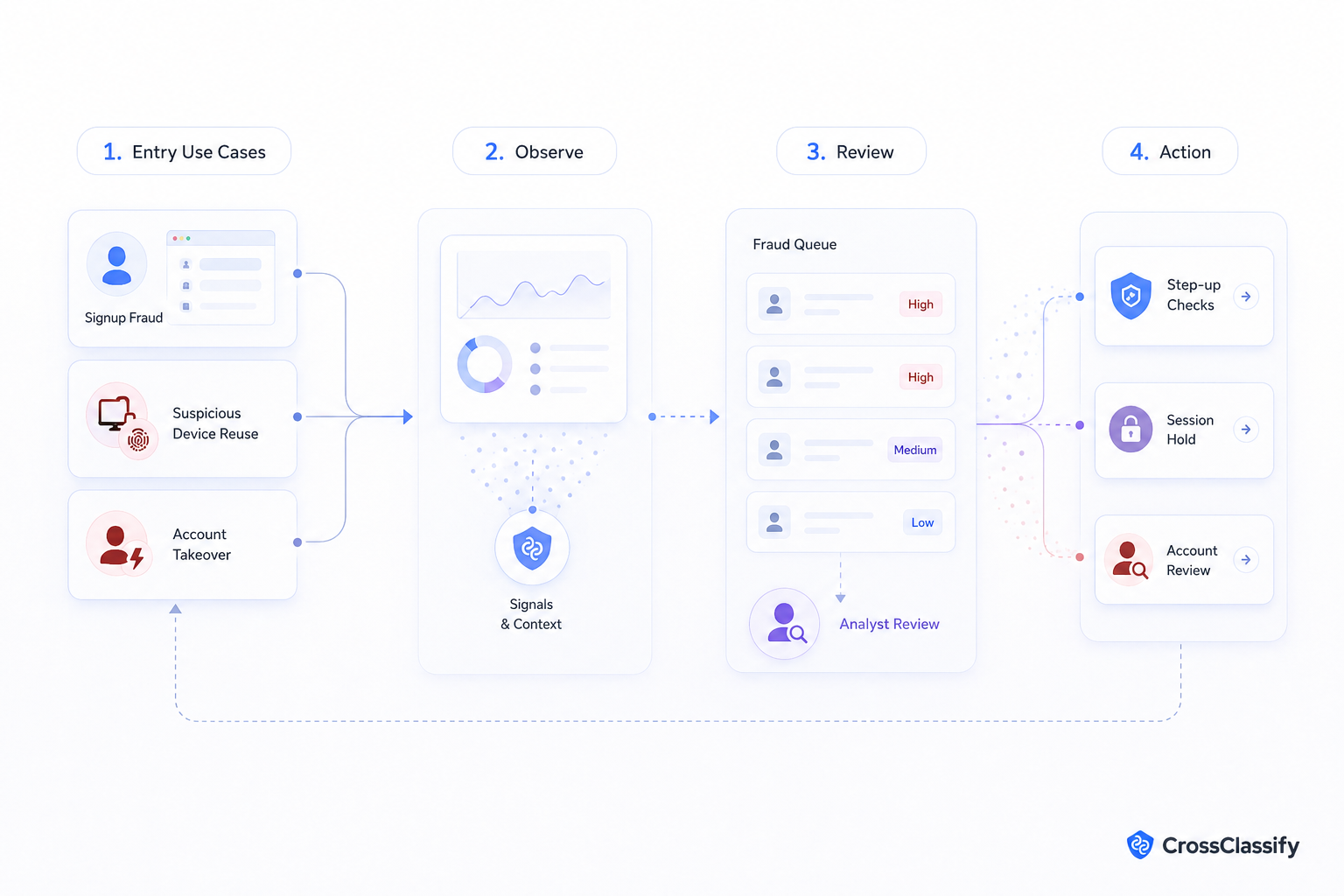
The first service should be narrow enough to sell, deploy, and measure. The best entry points are usually signup fraud detection, suspicious device detection, and account takeover protection.
Signup fraud detection helps customers stop fake accounts before they pollute the platform. Suspicious device detection helps customers understand repeated abuse across accounts. Account takeover protection helps customers identify risky logins, abnormal sessions, and sensitive account changes.
The MSSP can begin with observe mode. In this phase, CrossClassify collects signals and assigns risk scores without forcing immediate blocking. This lets the customer understand baseline behavior, review false positives, and align thresholds with business risk.
After baseline validation, the MSSP can move to monitored review. High risk events can route to a fraud queue, SOC workflow, support case, or customer system. Later, the customer can apply step up checks, session holds, or account review actions based on risk policy.
CrossClassify’s bot attack protection can support customers whose account systems are being hit by scripted signups, automated login attempts, fake traffic, and abuse patterns that damage platform trust.
What the customer gets
The customer gets better fraud visibility without rebuilding their platform. They can see which signups, logins, devices, sessions, and account changes are risky. They can prioritize manual review. They can reduce blunt controls that create friction for legitimate users.
The customer also gets a clearer bridge between security, fraud, product, and operations. The SOC can see enriched events. The fraud team can see risk explanations. The product team can reduce unnecessary friction. The partner can provide monthly evidence of risk reduction and service value.
What the partner gets
The MSSP gets a new recurring service line that is differentiated from standard security monitoring. It can create revenue from implementation, managed detection, SOC enrichment, SIEM integration, tuning, reporting, and ongoing customer review.
This also helps the partner become more strategic. Instead of only monitoring infrastructure events, the MSSP can help customers protect the parts of the business where trust is created, the signup journey, the login journey, the account session, and the customer facing platform.
Conclusion
MSSPs do not need to replace fraud teams or rebuild customer identity systems. They need a way to bring fraud context into the security workflows they already manage.
CrossClassify gives MSSPs a partner friendly way to add device intelligence, behavioral biometrics, account abuse detection, and risk scoring to customer facing applications. The result is a stronger managed service offer, better SOC context, fewer fake accounts, and clearer visibility into fraud patterns that traditional security tools may miss.
See How CrossClassify Stops Bot and Account Abuse
Detect suspicious automation, stop fake traffic, and reduce abuse at scale
Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Related articles
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required