Last Updated on 30 Mar 2026
How to Prevent OWASP A05:2025 Injection Attacks
Share in

Introduction
OWASP Top 10:2025 remains one of the most widely used baselines for application security, and the 2025 release explicitly positions Injection at A05, after Broken Access Control, Security Misconfiguration, Software Supply Chain Failures, and Cryptographic Failures. OWASP describes the Top 10 as a consensus awareness document for developers and web application security teams, built from current data and security trends rather than theory alone. That matters because Injection is not an academic flaw category. It is still one of the most tested and most operationally relevant risk areas in modern applications.
For Injection specifically, the OWASP 2025 data is striking. OWASP says 100 percent of tested applications were examined for some form of injection, the category maps to 37 CWEs, and it had the largest number of CVEs of any category. OWASP also highlights that this category includes more than 30,000 XSS CVEs and more than 14,000 SQL injection CVEs, which shows both breadth and persistence across the application ecosystem.
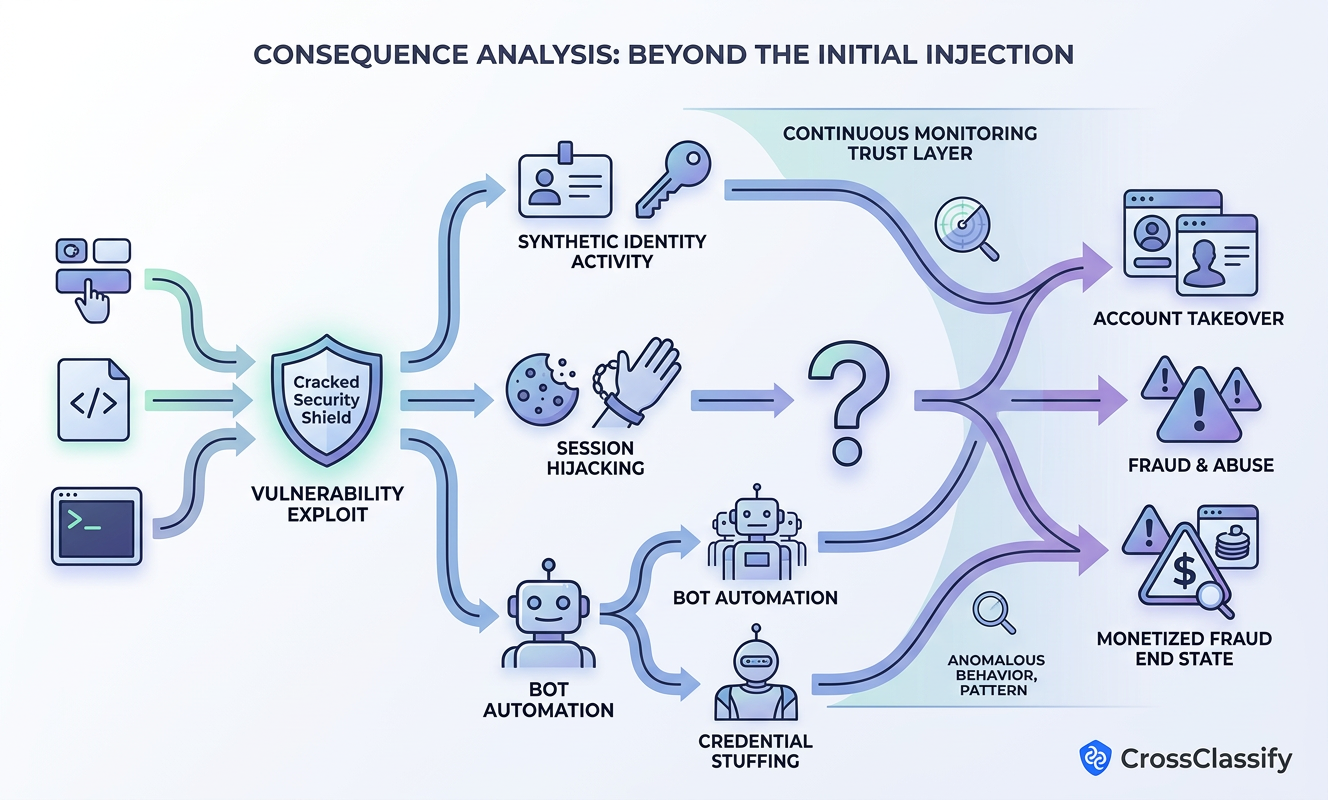
That is exactly why Injection deserves a broader business discussion than "just sanitize inputs." A single injection weakness can become a path to data theft, session hijacking, account takeover, bot abuse, fake account creation, or downstream fraud against customers and partners. In other words, Injection begins as an AppSec flaw, but often ends as an identity trust and fraud problem.
Top 10:2025 List
•
A01:2025 Broken Access Control
This category covers failures that let users act outside their intended permissions, such as forced browsing, CORS mistakes, or tampering with access control tokens. In practice, it is about users reaching data, functions, or flows they should never be able to reach.•
A02:2025 Security Misconfiguration
OWASP defines this as systems, applications, or cloud services being set up insecurely, such as leaving default accounts enabled, exposing unnecessary services, or missing hardening. It is dangerous because a secure design can still fail in production if the environment is configured badly.•
A03:2025 Software Supply Chain Failures
This category focuses on insecure dependencies, weak change management, poor CI and CD controls, and untrusted components entering production. OWASP ties it directly to missing SBOM discipline, weak patching, and weak oversight across the software pipeline.•
A04:2025 Cryptographic Failures
OWASP places cryptographic failures at number four and frames them around weak or missing cryptography, weak randomness, leaked keys, and related implementation errors. These failures often turn protected data into exposed or reusable credentials.•
A05:2025 Injection
Injection happens when untrusted input reaches an interpreter and gets executed as part of a command or query. It remains one of the most tested categories and still spans high volume XSS and high impact SQL injection.•
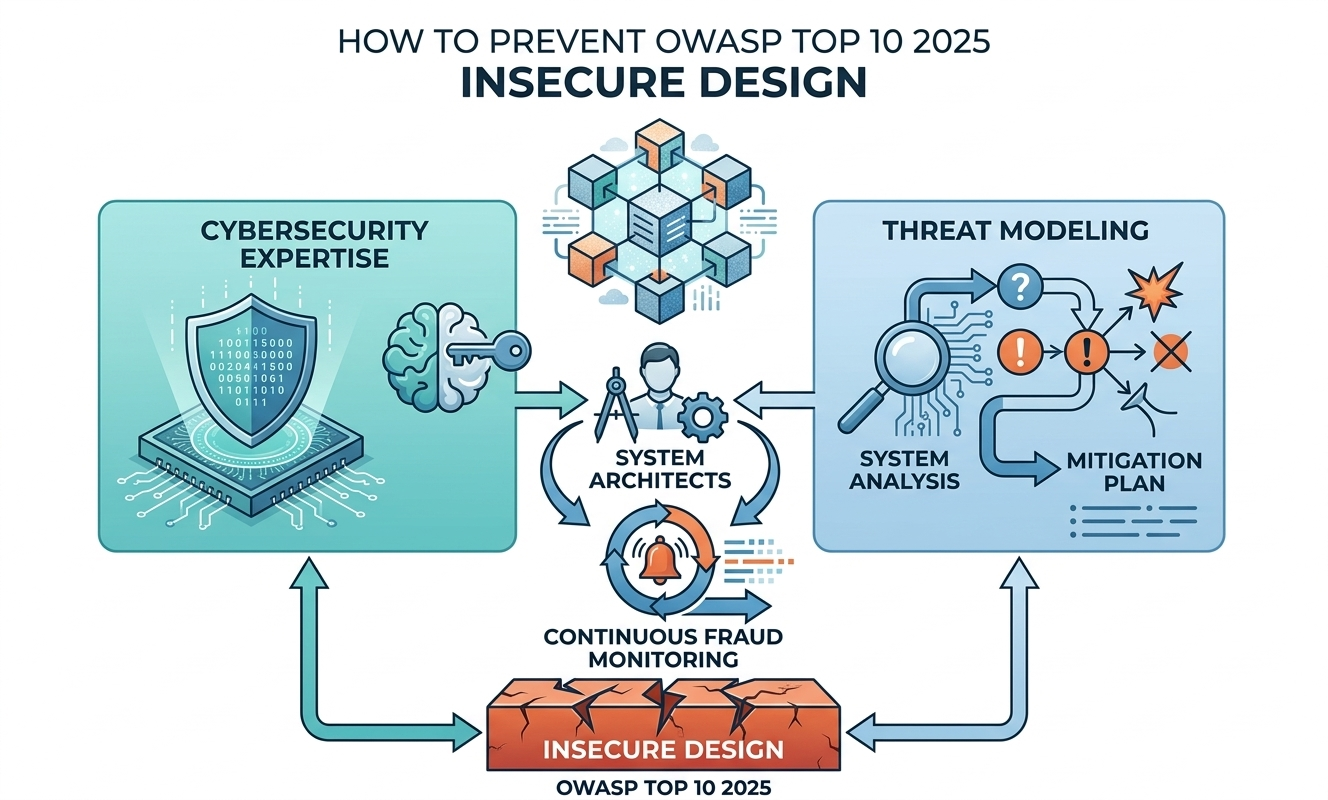
A06:2025 Insecure Design
OWASP describes insecure design as architectural or business logic flaws that exist before coding mistakes even happen. The remedy is not only better code, but better threat modeling, secure design patterns, and pre code security thinking.•
A07:2025 Authentication Failures
This category covers weaknesses in login, credential recovery, credential validation, and identity proofing. OWASP's guidance around breached password checking, modern password policy, and account enumeration resistance shows how much of this risk sits in operational identity design.•
A08:2025 Software or Data Integrity Failures
OWASP says this category is about trusting software, updates, artifacts, or data that have not been properly verified. It includes issues such as insecure deserialization, untrusted repositories, and missing integrity checks in CI and CD.•
A09:2025 Security Logging and Alerting Failures
This is about failing to log, alert, or investigate effectively, or even exposing sensitive data through logs themselves. OWASP also notes that poor encoding of log data can make logging systems vulnerable to injection too.•
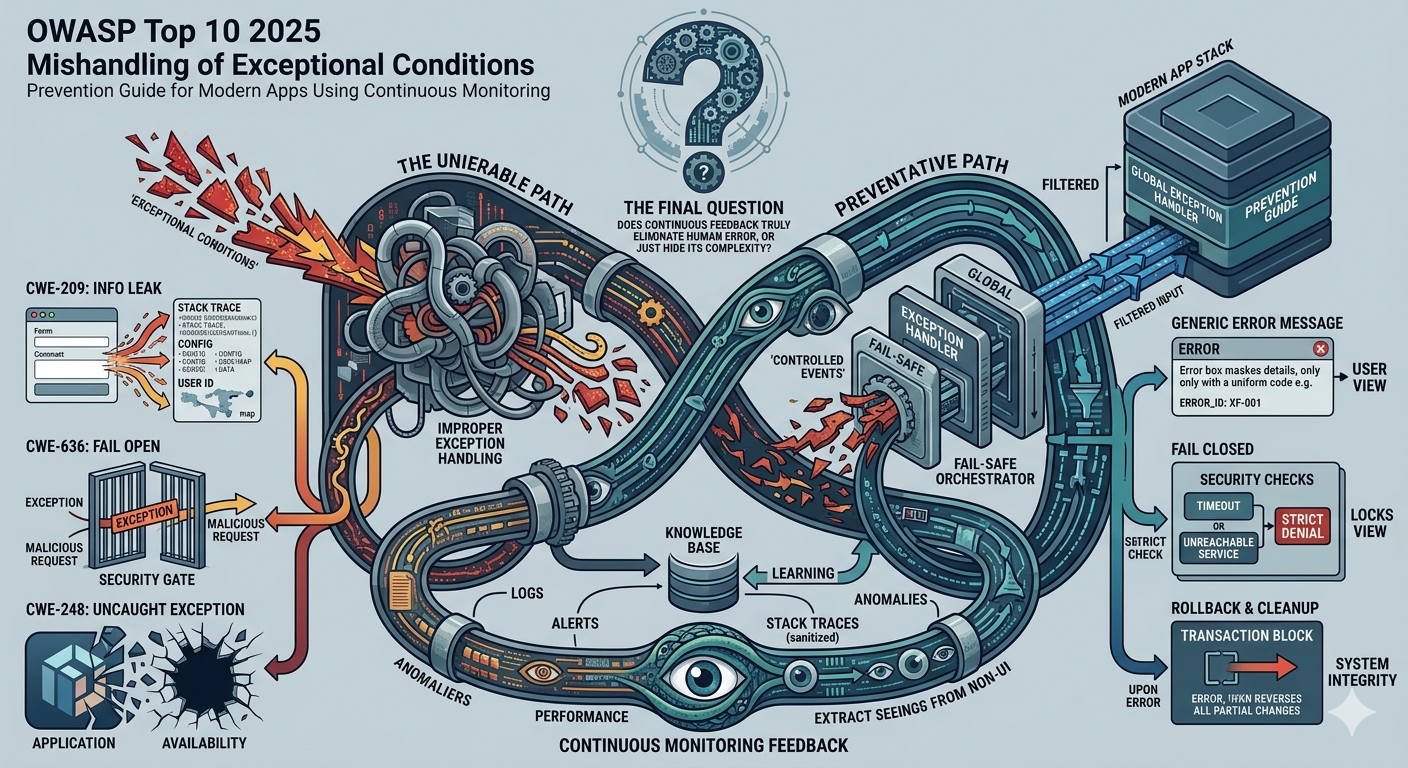
A10:2025 Mishandling of Exceptional Conditions
New in 2025, this category focuses on failing open, poor error handling, null dereferences, and broader failures to prevent, detect, or respond safely to abnormal situations. It matters because systems often become exploitable precisely when they are confused, stressed, or outside expected conditions.
Definition and Causes of Injection
Injection is an application flaw that allows untrusted input to be sent to an interpreter, such as a browser, database, template engine, or command shell, and causes the interpreter to execute part of that input as commands. OWASP's official A05 page says an application is vulnerable when user supplied data is not validated, filtered, or sanitized; when dynamic queries or non parameterized calls are used directly; when hostile input is concatenated into SQL or command strings; or when unsanitized data is passed through ORM search parameters.
OWASP also makes clear that common injection families include SQL, NoSQL, OS command, ORM, LDAP, EL, and OGNL injection. The concept is the same across all of them: the system stops treating the input as passive data and starts treating it as instructions. Once that happens, the attacker may read records, alter records, run commands, pivot to other systems, or manipulate what end users see in their browser.
The official 2025 numbers reinforce how widespread the problem remains. OWASP reports 37 mapped CWEs, a 100 percent testing coverage rate for some form of injection, 1,404,249 total occurrences in the dataset, and 62,445 total CVEs mapped into the category.
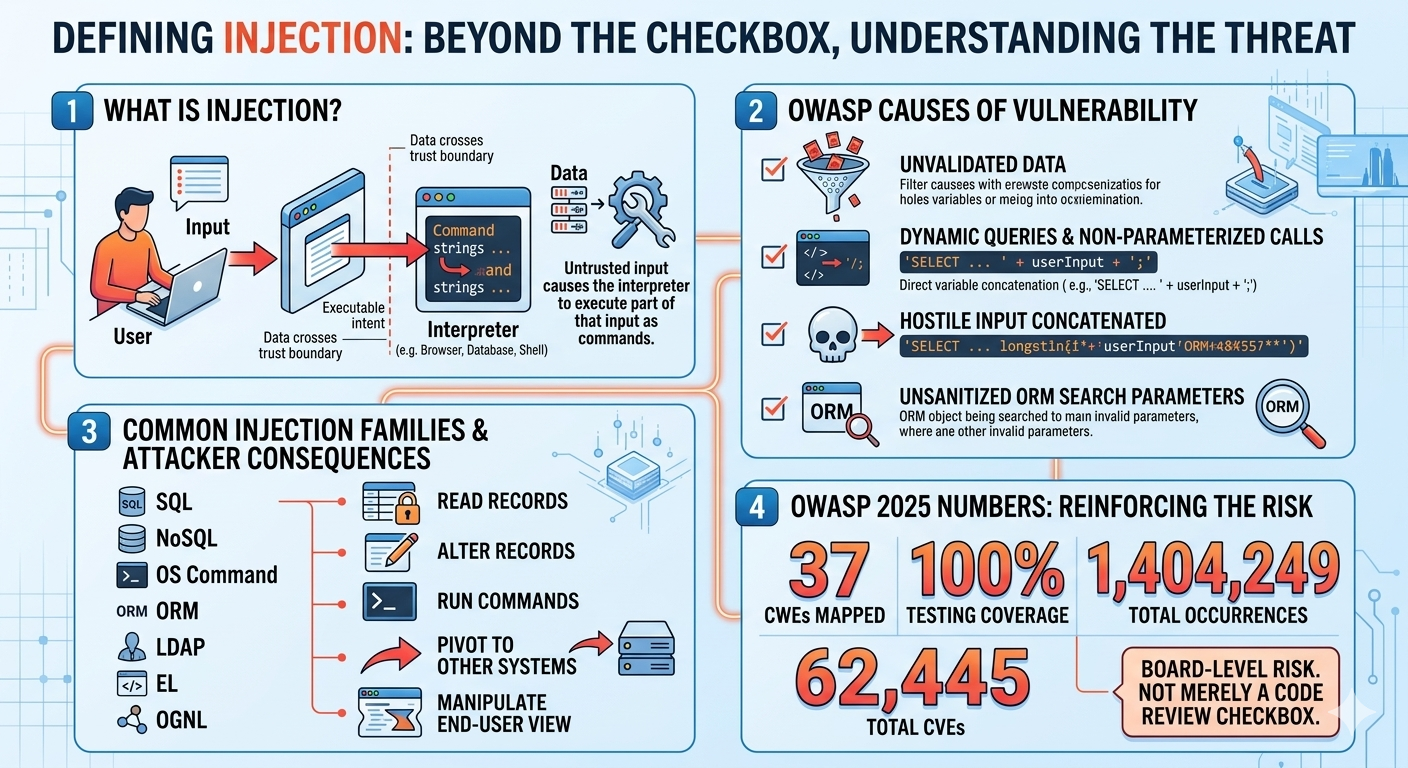
Variations of Injection
The most visible forms of Injection are still SQL injection and cross site scripting. OWASP's A05 page says the category includes more than 14,000 SQL injection CVEs and more than 30,000 XSS CVEs, with XSS lowering the average weighted impact because it is extremely common while SQL injection often carries more concentrated data exposure risk.
SQL injection lets an attacker interfere with the database queries an application makes. PortSwigger notes that successful SQL injection can reveal unauthorized data, modify or delete content, and in some cases compromise the underlying server or create a long term foothold. Blind SQL injection is especially dangerous because the application may not visibly return query results, yet attackers can still extract information through conditional behavior, timing, or out of band interaction.
Cross site scripting, or XSS, is another injection family inside A05. OWASP explains that XSS usually falls into reflected, stored, and DOM based forms, and that consequences can include cookie theft, session abuse, malicious redirects, and actions performed under the trust of the vulnerable site. In practical fraud terms, that means XSS can become a path to account takeover, session hijacking, and silent user impersonation.
Beyond SQLi and XSS, OWASP also calls out NoSQL injection, OS command injection, ORM injection, LDAP injection, EL injection, and OGNL injection. The technical lesson is clear: wherever an interpreter accepts attacker controlled input, the same trust boundary failure can reappear in a different syntax.
Real Examples of Injection
Group IB reported that the attackers compromised at least 65 websites between November and December 2023, primarily in the APAC region, using SQL injection and XSS to steal databases containing names, phone numbers, emails, dates of birth, and job seeker history. BleepingComputer, citing Group IB, reported that more than 2 million job seekers were affected. This is the exact pattern security leaders should notice: a web flaw turns into personal data theft, then into phishing fuel, identity abuse, and further fraud targeting.
Freepik and Flaticon breach
SecurityWeek reported that roughly 8.3 million users were affected after attackers exploited an SQL injection vulnerability in Flaticon, and Bitdefender summarized that the breach exposed 4.5 million email addresses plus 3.77 million email and hashed password combinations. Even when passwords are hashed, the business impact remains substantial because email lists, credential reuse risk, and user trust damage all persist after the initial intrusion.
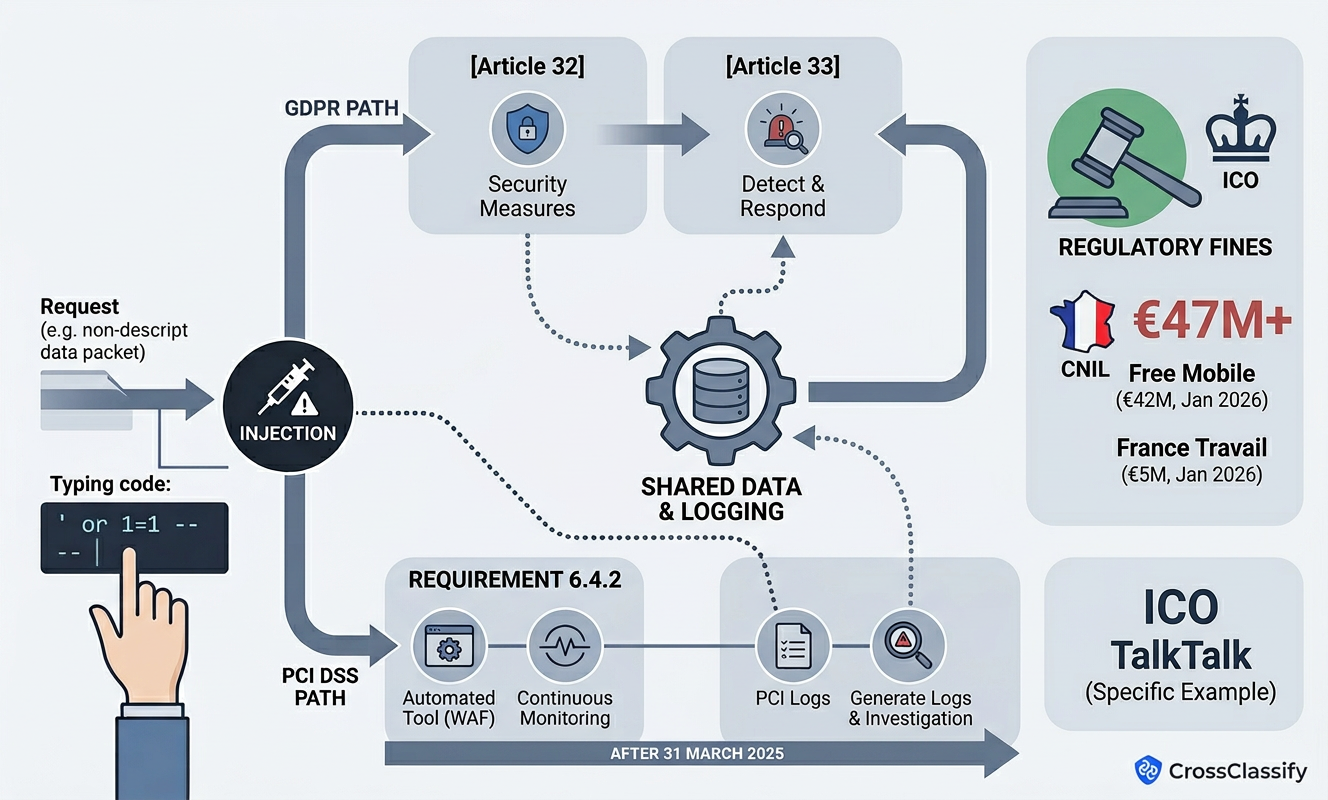
TalkTalk: a classic regulatory lesson
The UK ICO's official write up says the 2015 attack was an SQL injection attack, that known defenses existed, and that TalkTalk had failed to remove or secure legacy pages, patch outdated database software, and proactively monitor the vulnerable pages. The attack exposed personal data from 156,959 customers, including bank details in 15,656 cases, and resulted in a £400,000 fine under the pre GDPR regime.
Regulatory Compliance of Injection
From a GDPR perspective, Injection becomes a compliance issue the moment it threatens confidentiality, integrity, or availability of personal data. The EDPB's security and breach notification digest says Article 32 requires controllers and processors to implement appropriate technical and organizational measures for security appropriate to the risk, and Article 33 generally requires notification to the supervisory authority without undue delay and, where feasible, within 72 hours after awareness of a breach.
That means Injection is not only a prevention problem. It is also a detection, response, and evidence problem. On enforcement, the cleanest injection specific regulatory example is still TalkTalk, where the ICO explicitly tied the incident to SQL injection and inadequate security controls. Recent CNIL decisions show the scale regulators will use when essential security measures are inadequate: CNIL fined FREE MOBILE and FREE a combined €42 million in January 2026 for inadequate security of subscriber data, and fined FRANCE TRAVAIL €5 million in January 2026 for failing to ensure the security of job seekers' data under Article 32.
From a PCI DSS perspective, Injection is directly relevant because public facing payment applications are prime targets for web based attacks. PCI DSS v4.0.1 Requirement 6.4.2 requires an automated technical solution in front of public facing web applications that continually detects and prevents web based attacks, generates audit logs, and either blocks attacks or generates alerts that are immediately investigated. PCI SSC also states that 6.4.2 became effective after 31 March 2025.
Protection and Prevention Methods for Injection
OWASP says the preferred defense is to keep data separate from commands by using safe APIs, parameterized interfaces, or ORM tools where possible. This should be applied by backend engineers, API teams, database developers, and architects because it addresses the flaw at the source of execution. It is usually the most effective prevention control because it changes the query construction model itself, although OWASP warns that even stored procedures can still become vulnerable if developers concatenate hostile data inside them.
2. Positive server side input validation
OWASP recommends positive server side input validation when data cannot be fully separated from commands. This is mainly the responsibility of backend developers, API owners, and application architects because the server must define what valid input looks like before processing it. It is highly useful for shrinking attack surface, but OWASP explicitly says it is not a complete defense since many applications legitimately need special characters and flexible input.
3. Context aware escaping for residual dynamic queries
OWASP also allows escaping as a residual defense when dynamic queries cannot be eliminated, but only with great caution. OWASP warns that these techniques are error prone, fragile under change, and cannot safely solve user controlled SQL structure names such as table names or column names. The benefit is short term risk reduction for legacy paths; the drawback is that it is not robust enough to be your strategic defense.
4. Source code review, fuzzing, and runtime testing
OWASP says detection is best achieved by combining source code review with automated testing, including fuzzing, across parameters, headers, URLs, cookies, JSON, SOAP, and XML inputs. The strength is coverage across many input surfaces that developers may forget; the weakness is that testing still finds only what is exercised, not every latent flaw in business logic or traffic patterns.
5. DAST, SAST, and IAST in the pipeline
OWASP's A05 page says SAST, DAST, and IAST can help identify injection flaws before production deployment. DAST is defined as black box testing against running applications that can uncover flaws such as SQL injection, XSS, authentication issues, and server configuration mistakes. The advantage is earlier detection and repeatable scanning; the limitation is that scanners do not replace secure design, secure coding, or runtime controls.
Protection Tools for Injection
OWASP's DevSecOps guideline lists DAST as a practical way to test running applications for injection and related flaws without requiring source code access. It also references tools such as OWASP ZAP, Burp Suite, Acunetix, and other automated scanners that can help surface exploitable paths before release.
For compliance driven environments, especially payments, tooling now extends beyond scanning. PCI DSS v4.0.1 explicitly requires an automated technical solution for public facing web applications that continually detects and prevents web based attacks, generates logs, and blocks or rapidly escalates alerts. In effect, scanning helps you find weaknesses, while real time protective controls help you survive the ones you missed, the ones newly introduced, or the ones attackers discover first.
The Gap That Still Exists After Secure Coding
Here is the gap many technical teams still leave open. OWASP's prevention advice for Injection is correct and necessary, but real systems are large, fast moving, and never fully static. A team can parameterize most queries, validate most inputs, scan most endpoints, and still miss one legacy report builder, one hidden admin flow, one partner callback, one template sink, or one post login session abuse pattern.
That is where runtime trust monitoring becomes strategically important. Injection often starts as a code flaw, but the attacker's objective is rarely "run a payload just for fun." The objective is usually to steal data, hijack a session, abuse an account, create fake accounts, scrape content, automate actions, or move money. When seen from that angle, the real defensive question is not only "did we prevent every injection flaw," but also "can we detect the abnormal device, session, and behavior patterns that appear when an injection path is actually being exploited?"
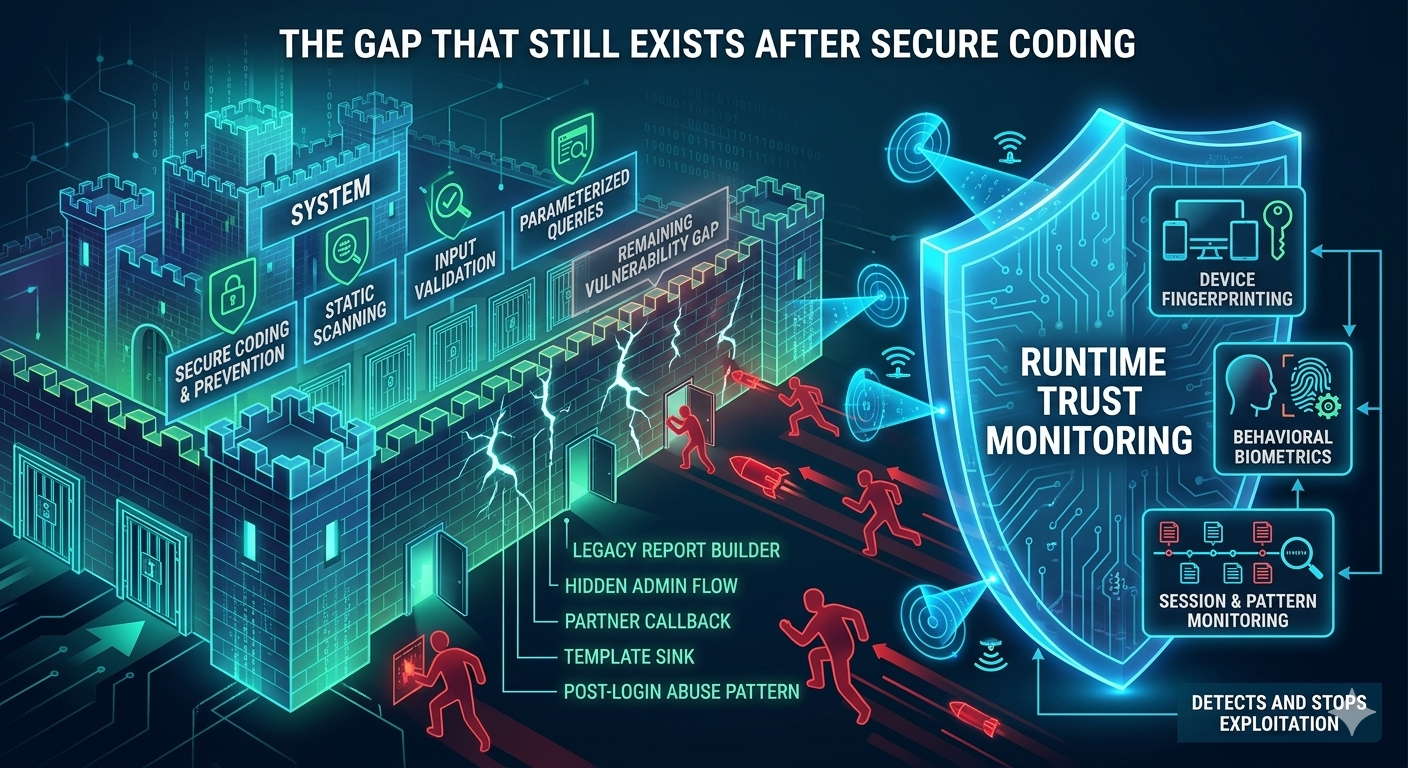
The device fingerprinting solution positions device intelligence as a continuous monitoring layer rather than a one time login check. CrossClassify says it gathers and correlates hardware and software attributes to build a resilient device identity across sessions, even when IPs, browsers, or cookies change, and uses that to detect returning fraudsters, manipulation attempts, multi account abuse, and unusual device signatures during sensitive actions. For Injection defense, that matters because an exploited XSS or session theft event often still reveals itself through abnormal device continuity, suspicious device shifts, spoofing attempts, or reuse of risky infrastructure.
Device fingerprinting does not replace secure coding, DAST, or parameterized queries. It closes the runtime gap by helping teams recognize when a compromised session or injected client side path is being operated from a device profile that does not fit the historical trust pattern of the user.
Behavioral biometrics as a continuous authentication layer
The behavioral biometrics solution adds a second layer: how the user behaves after access begins. CrossClassify describes continuous authentication based on keystroke dynamics, pointer trajectory, touch pressure, scroll rhythm, accelerometer tilt, and session context, with risk based step up for high risk flows such as payouts, profile edits, and other sensitive actions. For Injection scenarios, especially XSS, stolen sessions, or injected browser side actions, this is critical because the session may technically be valid while the live behavior is not.
CrossClassify also states that behavioral biometrics can reduce friction by distinguishing natural user variability from automation, and can trigger enriched real time alerts for fail to success login flips, device binding breaks, payout edits, and bot velocity.
Why Continuous Monitoring Is Necessary for Injection
Injection risk has always been larger than the initial payload. SQL injection can expose identity data, XSS can steal cookies or ride trusted sessions, and command injection can create footholds that later support fraud or abuse. The final monetization often looks like account takeover, bot automation, synthetic identity activity, or session hijacking rather than a textbook vulnerability scan result.
That is why a platform like CrossClassify fits most naturally as the runtime trust layer beside traditional AppSec controls, not instead of them. The account takeover solution highlights continuous monitoring for session hijacking, phishing based takeovers, stolen tokens, and behavioral mismatches, while the bot attack solution emphasizes real time detection of scraping, credential stuffing, automated abuse, and anomalous traffic patterns. Those are exactly the downstream manifestations that many successful injection campaigns eventually produce.
Conclusion
OWASP A05 Injection remains one of the clearest reminders that modern application security is still built on fundamentals. Parameterized queries, safe APIs, strong input validation, disciplined code review, and DAST remain essential because they prevent the flaw from existing in the first place. OWASP, PCI DSS, and GDPR aligned guidance all point in the same direction: prevention matters, but timely detection, protective controls, and reliable response matter too.
That is where the second half of the strategy becomes valuable. The device fingerprinting solution adds persistent device continuity and anomaly detection across sessions, while the behavioral biometrics solution adds continuous authentication based on how the user actually interacts with the application. Together, they help application owners detect the fraud, abuse, and session misuse that can still occur after one missed control, one unpatched endpoint, or one injected client side path slips through.
So the best practical framing is this: secure coding and security testing are your first line for OWASP Injection, but continuous device and behavior monitoring is your safety net when reality gets messy. That makes the digital world safer not only because fewer flaws are exploitable, but because fewer successful exploits remain invisible long enough to become fraud.
Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Related articles
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required