Last Updated on 06 May 2026
Glassdoor Employer Account Takeover Protection for Recruitment Trust
Share in

Introduction
An employer account on a recruitment platform is not just a login. It is a trusted control point.
- It can manage a company profile.
- It can post jobs.
- It can respond to reviews.
- It can edit employer information.
- It can influence candidate trust.
- It can shape how a company appears in the market.
That makes employer accounts valuable targets.
For Glassdoor style platforms, employer account takeover is not only an authentication problem. It can become fake job posting, recruiter impersonation, reputation abuse, candidate data exposure, and employer brand damage.
CrossClassify helps protect these accounts by scoring behavior, device trust, session context, and high risk actions in real time. The goal is not to slow every employer down. The goal is to detect when a trusted account suddenly stops behaving like a trusted account.
Why employer accounts are attractive to attackers
Attackers prefer trusted surfaces.
A fake job from a new unknown company may raise suspicion. A fake job from a known employer profile feels more believable. A suspicious message from a new recruiter may be ignored. A message from a trusted employer account may be taken seriously.
That is why employer account takeover can be more dangerous than fake account creation.
A compromised employer account may allow attackers to post jobs, change contact fields, add fake recruiter users, respond to reviews, redirect candidates, or create reputational confusion.
For a platform, the damage spreads across several audiences.
- Candidates may fall for scams.
- Employers may lose trust in the platform.
- Moderation teams may face urgent investigations.
- Sales teams may face angry customers.
- Product teams may need emergency controls.
- Legal teams may need to assess user harm.
This is why employer account protection should be treated as a core recruitment trust layer.

Why passwords and MFA are not enough
Passwords fail because credentials are stolen, reused, phished, or leaked. MFA helps, but it does not solve every attack. Attackers can use stolen sessions, social engineering, malware, proxy networks, or compromised employee devices.
A login may pass authentication and still be risky.
That is why CrossClassify focuses on continuous risk scoring. CrossClassify’s account takeover solution combines device fingerprinting, behavioral biometrics, and real time risk scoring to detect suspicious account access. For recruitment platforms, this means protection continues after login, especially when the user performs sensitive employer actions.
This matters because the riskiest activity often happens after authentication. The platform should score not only who logged in, but what they do next.

The high risk employer actions that need protection
A Glassdoor style platform should apply risk scoring to employer actions that can create trust damage.
Profile edits are one example. If an attacker changes company details, links, contact information, or branding elements, candidates may be redirected or misled.
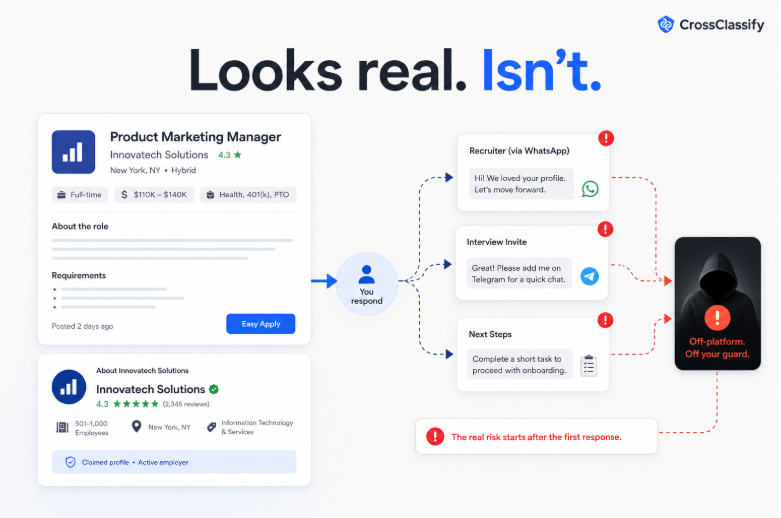
Job posting is another major action. A compromised account can publish scam jobs under a trusted employer name.
Recruiter messaging is also sensitive. If attackers can contact candidates through a trusted account, they can move victims off platform.
Review responses matter as well. A hijacked employer account can post inappropriate replies, reveal sensitive details, or damage brand perception.
User management is a major risk. Attackers may invite new users to preserve access.
Billing and subscription changes can also indicate account misuse.
Export or access to candidate related information should be treated as high risk when available.
CrossClassify can score all these events. A normal employer session continues smoothly. A suspicious session receives added verification, delayed execution, manual review, or blocking.

How CrossClassify detects risky employer sessions
CrossClassify creates a trust profile around normal employer behavior.
- It can evaluate whether the device is familiar.
- It can detect whether the browser or environment looks manipulated.
- It can observe whether navigation and interaction behavior match the expected pattern.
- It can identify whether the user is acting unusually fast.
- It can see whether risky changes happen immediately after login.
- It can connect the session to past suspicious accounts, devices, or infrastructure.
This is where device fingerprinting becomes especially useful. CrossClassify’s device fingerprinting solution is built to detect suspicious devices, reveal repeat abuse, and support continuous device monitoring. That helps recruitment platforms recognize when attackers change emails, cookies, or IP addresses but still leave technical and behavioral traces.
Behavioral biometrics adds another layer. A legitimate employer user has typical interaction patterns. A fraudster using stolen credentials may move differently, paste more often, skip normal steps, or rush toward sensitive actions.
CrossClassify combines these signals into a practical risk score.
Employer account takeover and fake job scams
Employer account takeover and fake job detection are closely connected.
If a scammer creates a fake employer account, the platform can inspect signup risk. But if a scammer compromises a real employer account, the platform must detect that the session has changed.
This is why the CrossClassify Job Scam and Recruiter Impersonation Monitor should be connected to employer account protection.
For example, a session may look risky because it uses a new device, changes company contact details, posts multiple remote jobs, and sends messages asking candidates to continue by text. Any one signal may be explainable. Together, they form a strong risk story.
The system can then block the message, hold the job post for review, or require stronger verification before the action goes live.
This is better than waiting for candidates to report the scam.
Employer account takeover and review abuse
A compromised employer account can also affect review trust.
The attacker may respond to reviews in ways that damage the company. They may try to change employer profile information. They may trigger disputes that create moderation burden. They may help coordinate fake positive review campaigns by creating a false appearance of employer activity.
CrossClassify’s Employer Reputation Abuse Graph helps connect these events. It can show whether suspicious employer access overlaps with unusual review activity, rating spikes, fake account clusters, or repeated devices.
This is important because reputation abuse is often not a single event. It is a sequence.
- Login.
- Profile change.
- Review activity spike.
- Job posting.
- Candidate messaging.
- Off platform contact.
A graph view helps trust teams see the sequence rather than isolated incidents.

How silent mode creates a low risk pilot
The easiest way for a Glassdoor style platform to start is silent mode.
In silent mode, CrossClassify scores employer sessions and actions without blocking users. The platform can compare risk scores against known incidents, moderator decisions, employer reports, and account recovery cases.
This helps product and trust teams answer practical questions.
- Which signals are most predictive.
- How many high risk sessions appear each week.
- How many false positives occur.
- Which employer actions carry the highest risk.
- How often suspicious sessions lead to fake job or review abuse.
- Which step up controls would be most effective.
After validation, the platform can begin active enforcement only for high confidence cases.
That lowers change management risk and builds internal trust.
Why this should be positioned as trust protection
Employer account security can sound like an internal platform problem. But for recruitment marketplaces, it affects external trust.
Candidates trust employer accounts. Employers trust the platform to protect their brand. Review readers trust that responses and company profiles are authentic.
CrossClassify should position employer account takeover protection as part of recruitment trust protection.
That framing makes it relevant to product, trust and safety, employer experience, legal, and revenue teams.
Conclusion
Employer accounts on Glassdoor style platforms are high value control points. If attackers compromise them, the damage can spread into fake jobs, scam outreach, profile manipulation, review abuse, and employer reputation harm.
CrossClassify protects employer accounts with real time risk scoring, device fingerprinting, behavioral biometrics, and graph analysis. It helps platforms challenge only suspicious sessions while keeping legitimate employer workflows smooth.
The strongest approach is not more friction for every employer. It is smarter trust scoring at the moments where account abuse creates the most damage.
Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Related articles
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required