Last Updated on 15 May 2026
Device Fingerprinting for Cybersecurity Service Providers
Share in

Introduction
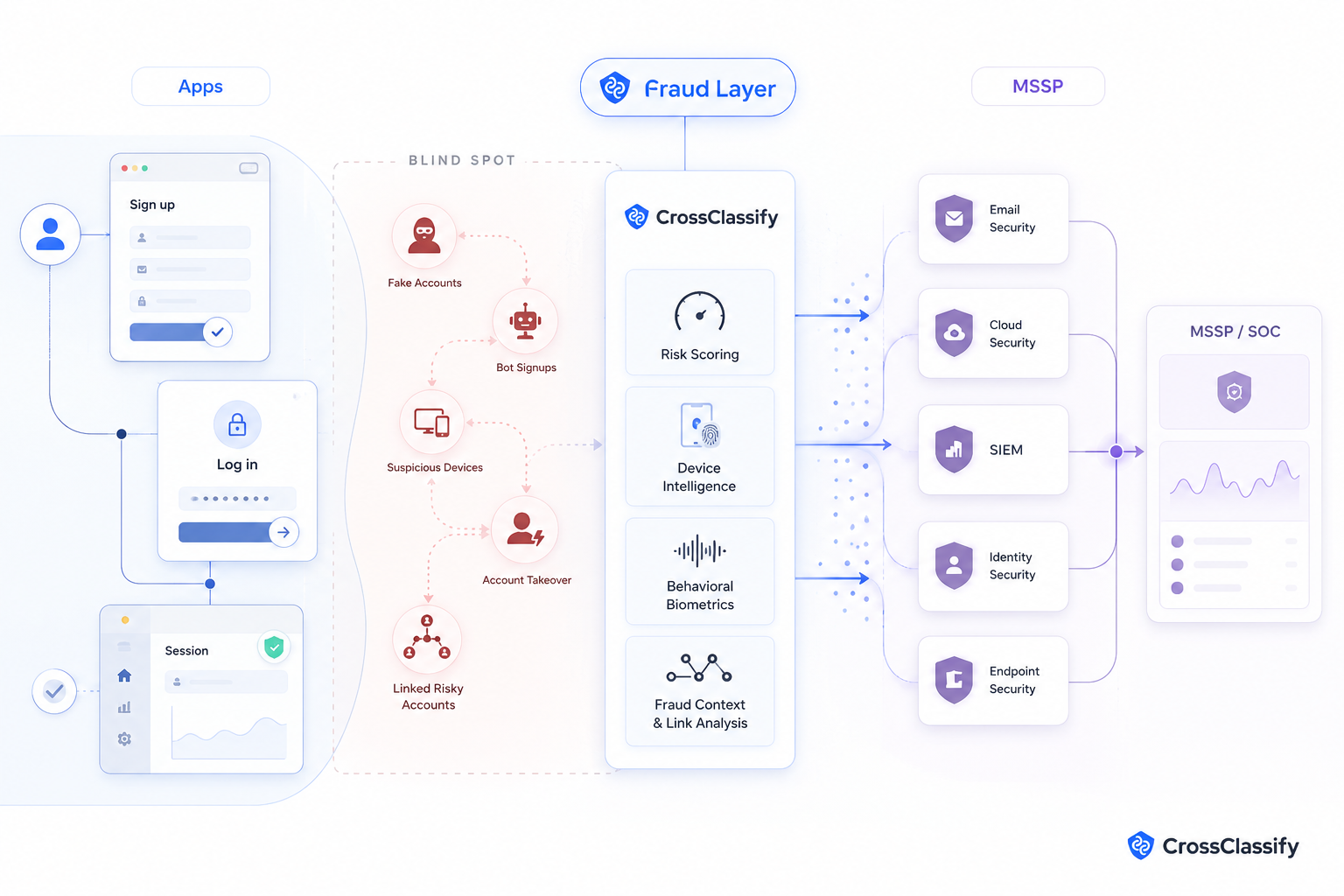
Cybersecurity service providers are used to protecting systems, identities, networks, endpoints, and cloud environments. But many customers now face a different problem. Their digital platforms are being abused by devices that create fake accounts, rotate identities, bypass bans, trigger suspicious login patterns, and return again under new details.
Device fingerprinting gives cybersecurity partners a new way to help customers understand who is really interacting with their web and mobile platforms. It does not replace MFA, SIEM, WAF, identity tools, or manual review. It adds a device intelligence layer that helps reveal repeat abuse and suspicious patterns across customer facing journeys.
CrossClassify makes device fingerprinting useful for partner led services by combining it with behavioral biometrics, account risk scoring, bot detection, suspicious device monitoring, graph relationships, and SIEM ready alerts.
Why device identity matters
Fraud teams often see accounts. Security teams often see logs. Product teams often see sessions. Attackers exploit the gaps between these views.
One person or automation setup can create many accounts. One emulator farm can test many signups. One suspicious device can return after cookies are cleared. One account takeover attempt can appear normal until the device, location, and behavior no longer match the account history.
That makes device identity one of the most important missing signals in customer facing security. The account may change. The email may change. The IP address may change. The session may look new. But device, environment, behavioral, and consistency signals can still reveal that activity is connected.
CrossClassify’s device fingerprinting solution helps customers recognize risky device patterns across web and mobile journeys. The goal is not to block every unfamiliar device. The goal is to understand device risk in context.

Why this matters for partners
Cybersecurity service providers are already trusted to deploy and operate tools that customers cannot easily manage alone. Device fingerprinting fits this model because the value is not only in collecting signals. The value is in connecting those signals to business workflows.
A partner can help the customer answer practical questions. Which devices are creating repeated accounts? Which accounts are linked by device history? Which logins come from unusual device environments? Which sessions should be reviewed before a payout, profile change, or high risk action? Which suspicious devices should be monitored rather than immediately blocked?
These questions create service opportunities for MSSPs, system integrators, managed SOC providers, identity consultants, cloud security consultants, and application security teams.
The partner can package device fingerprinting as suspicious device monitoring, account abuse detection, signup fraud detection, account takeover protection, or fraud alert enrichment.
What device fingerprinting detects
Device fingerprinting can help detect repeated devices, tampered environments, emulator usage, browser manipulation, suspicious device reuse, abnormal device changes, and device clusters connected to multiple accounts.
On its own, device data is not enough. CrossClassify combines device signals with behavior, network context, account history, session timing, and graph relationships. This makes the signal more useful and less brittle.
For example, a new device may be normal. A new device with impossible location behavior, scripted navigation, high velocity signup activity, and shared links to other suspicious accounts is different.
For account creation risk, partners can connect this approach to account opening protection. That helps customers catch fake accounts and repeat abuse earlier in the journey.

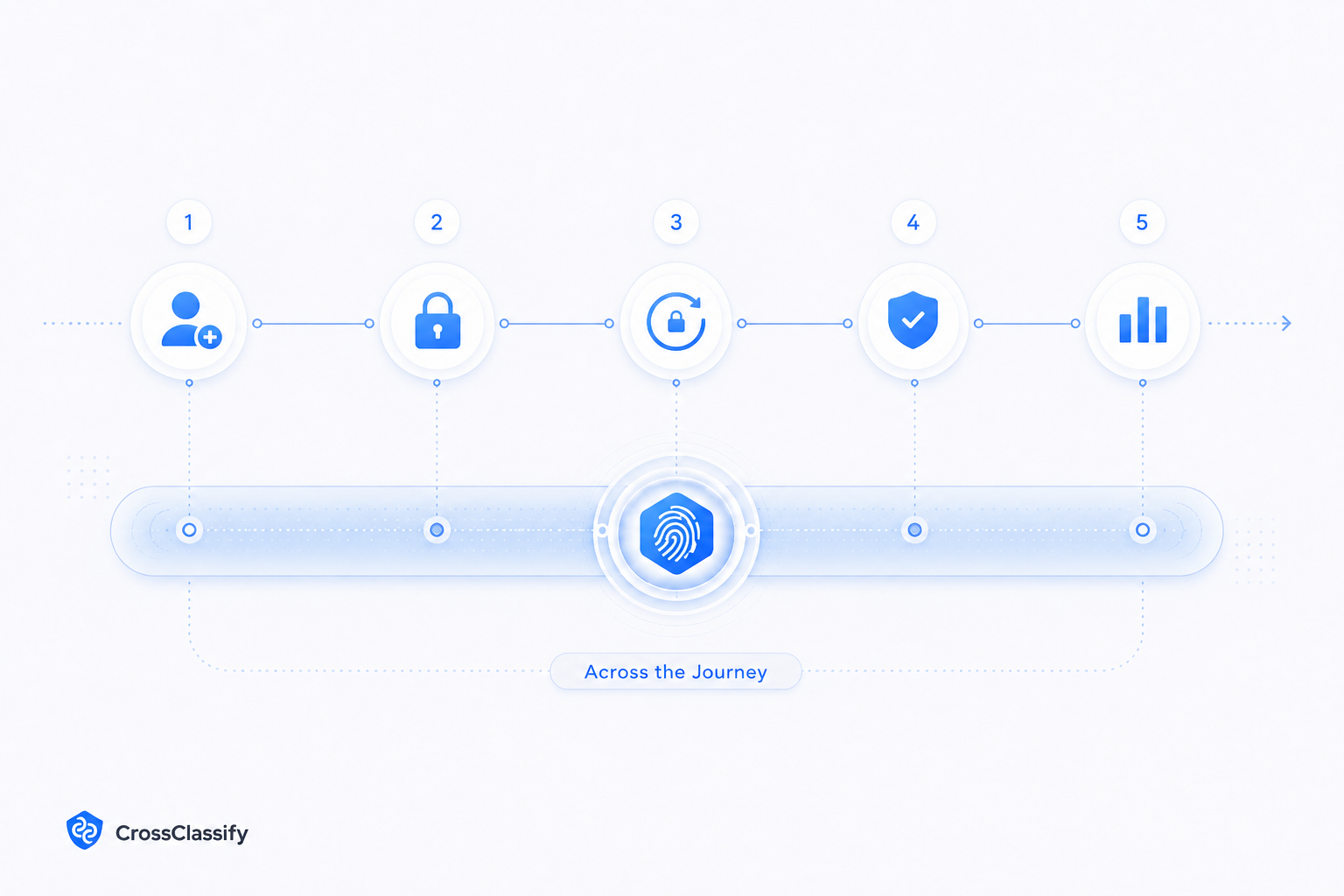
Where device fingerprinting fits in the customer journey
Device fingerprinting should not only sit at login. The most valuable deployments cover multiple points in the account lifecycle.
At signup, device intelligence can detect repeat account creation, emulator abuse, automated environments, and suspicious device reuse.
At login, device intelligence can compare the current environment with trusted account history.
At account recovery, it can help detect whether a recovery attempt comes from a risky or unfamiliar device.
At profile change, payout edit, or sensitive action, it can help decide whether the session deserves step up verification or manual review.
At post login activity, it can help connect abnormal behavior with device risk.
For login and session risk, CrossClassify connects naturally with account takeover protection. This gives customers more context before they decide whether to step up, review, hold, or allow activity.
How partners can make device intelligence operational
The mistake many teams make is treating device fingerprinting as a standalone technical feature. Partners should instead package it as an operational workflow.
A good partner package includes SDK deployment, backend API integration, risk threshold design, dashboard setup, SIEM event mapping, fraud queue routing, and monthly suspicious device reporting.
For managed SOC teams, device intelligence can become an alert enrichment layer. For system integrators, it can become a deployment project. For VARs, it can become a differentiated solution bundle. For identity consultants, it can become a risk based access improvement.
CrossClassify’s Multi Tenant Customer Management and Partner Usage Dashboard help partners manage customers without turning every deployment into a custom one off project.

Privacy and governance
Device fingerprinting should be implemented with purpose limitation, minimization, retention controls, access controls, transparency, and secure handling. Cybersecurity partners should not position it as a shortcut to compliance. They should position it as a risk signal layer that supports fraud prevention, suspicious activity detection, and access protection.
CrossClassify’s Fraud Risk Explanation Layer helps partners explain why an event was scored as risky. This makes device intelligence easier to review, govern, and tune.
A good implementation should define which signals are collected, why they are collected, how long they are retained, who can access them, and what action can be taken based on risk scores.
Conclusion
Device fingerprinting gives cybersecurity service providers a practical way to expand into fraud detection for customer facing platforms. It helps customers detect suspicious devices, repeated abuse, fake accounts, bot signups, and account takeover patterns that static controls often miss.
CrossClassify makes this partner friendly by combining device intelligence with behavioral biometrics, risk scoring, account abuse detection, SIEM templates, managed service dashboards, and explainable fraud signals.
See How Stop fraud with unique device identification
Create powerful device profiles to uncover hidden threats instantly

Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Related articles
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required