Last Updated on 30 Mar 2026
OWASP A02:2025 Security Misconfiguration Prevention Platform
Share in

Introduction
OWASP Top 10 is one of the most widely used awareness references for modern application security. Teams use it to align development, DevOps, and security priorities around the risks that most often lead to real incidents, data exposure, account takeover, and business disruption. In the 2025 edition, OWASP highlights that misconfiguration risk is rising as software becomes more configurable across cloud services, containers, frameworks, and deployment pipelines.
Security Misconfiguration is ranked A02 in OWASP Top 10:2025, and OWASP reports a striking data point: 100% of tested applications had some form of misconfiguration, with 719,084 total CWE occurrences mapped to this category and 1,375 total CVEs associated with the mapped CWEs. That is why this topic is not only a security hygiene discussion, it is a growth and trust discussion for any product handling logins, onboarding, payments, or high value actions. If you operate fintech, ecommerce, SaaS, telecom, logistics, or any consumer platform, misconfiguration becomes a multiplier for fraud like account takeover, account opening abuse, and bot driven exploitation.
Top 10:2025 List
•
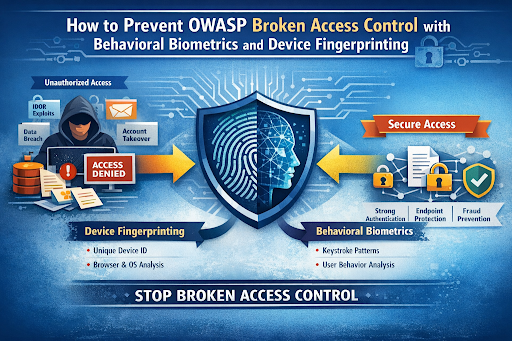
A01:2025 Broken Access Control
This risk is about users gaining access to data or actions they should not have, often through missing object level checks or weak authorization logic. It frequently results in data exposure and privilege escalation.•
A02:2025 Security Misconfiguration
This risk happens when systems, applications, or cloud services are configured insecurely, leaving unnecessary features enabled or permissions too open. It often becomes the easiest entry point because it is exploitable without sophisticated payloads.•
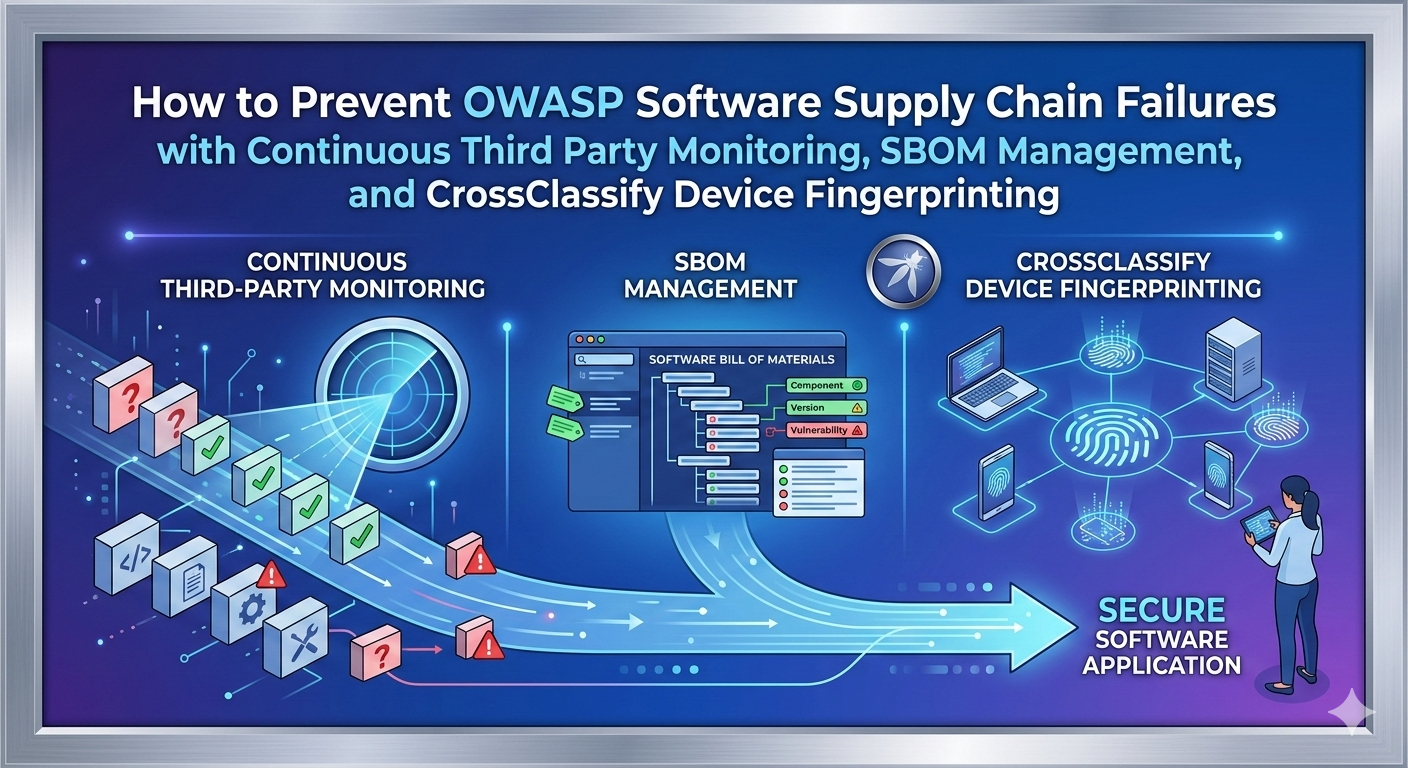
A03:2025 Software Supply Chain Failures
This risk focuses on third party components, build pipelines, and dependencies that can introduce vulnerabilities or malicious code. Compromise can happen upstream, then propagate downstream into production.•
A04:2025 Cryptographic Failures
This risk covers broken or missing protection of sensitive data due to weak encryption choices, incorrect key handling, or insecure protocols. The result is often data disclosure or tampering.•
A05:2025 Injection
This risk occurs when untrusted input is interpreted as commands or queries, such as SQL injection or command injection. It can lead to data theft, remote code execution, or full compromise.•
A06:2025 Insecure Design
This risk is about missing security controls at the design level, even if code is clean and patched. It often shows up as workflows that can be abused for fraud or bypassed under real attacker behavior.•
A07:2025 Authentication Failures
This risk includes weak login protections, poor session management, and credential attacks like credential stuffing or password spraying. It is a direct driver of account takeover at scale.•
A08:2025 Software or Data Integrity Failures
This risk covers untrusted updates, insecure CI CD processes, and missing integrity checks that allow data or code manipulation. It can turn a routine update process into an attacker controlled delivery channel.•
A09:2025 Security Logging and Alerting Failures
This risk happens when detection is weak, logs are incomplete, or alerting does not trigger when it should. The outcome is longer dwell time, slower response, and larger financial and reputational impact.•
A10:2025 Mishandling of Exceptional Conditions
This is new in 2025 and focuses on unsafe error handling, failing open, and unpredictable states triggered by abnormal conditions. It often enables deeper exploitation because errors reveal sensitive context or break business logic.
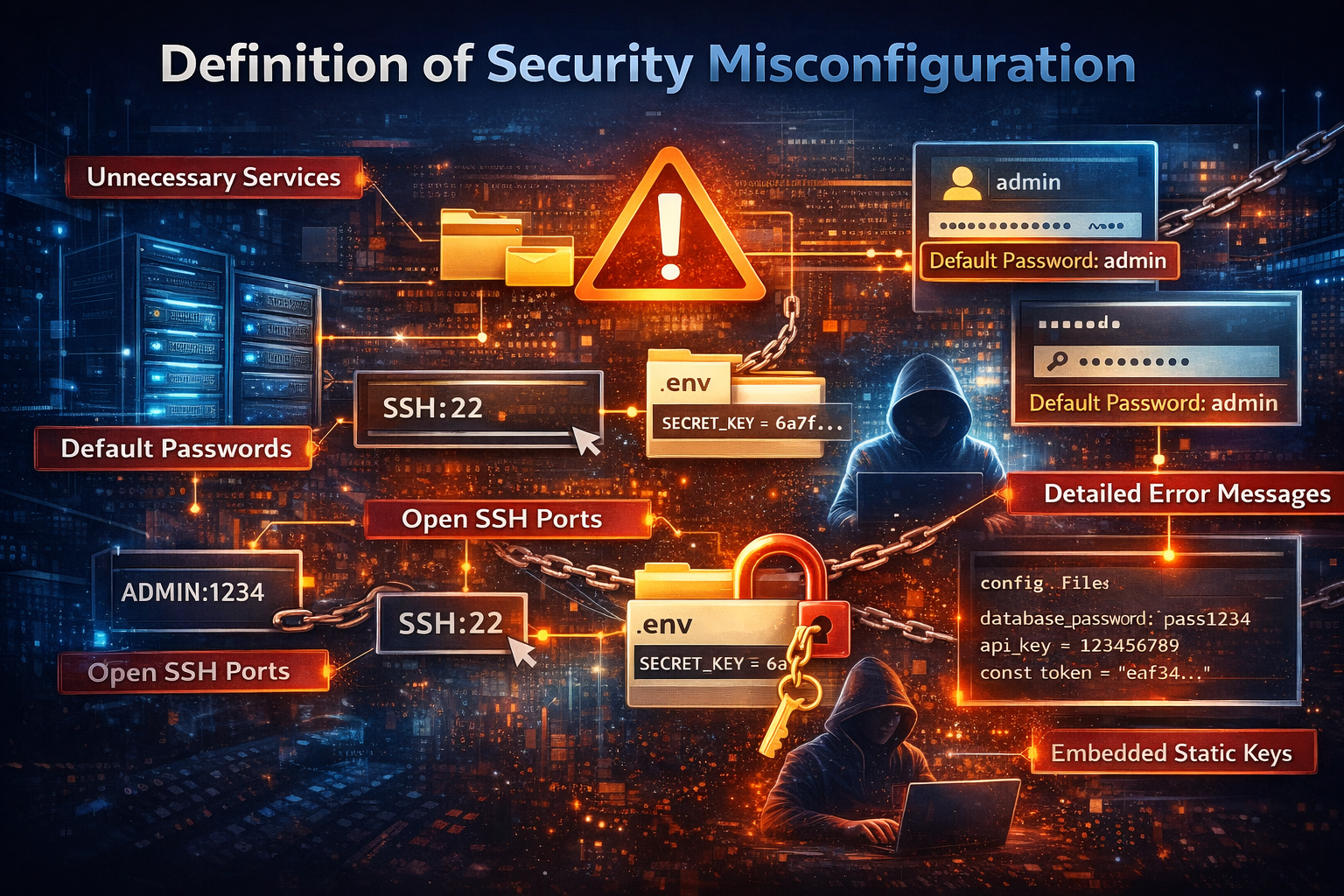
Definition of Security Misconfiguration
Security Misconfiguration means a system, application, or cloud service is set up incorrectly from a security perspective, creating avoidable weaknesses that attackers can exploit. OWASP emphasizes that misconfiguration can exist across any layer of the stack, including servers, frameworks, libraries, databases, and cloud services, especially when hardening is missing or permissions are configured improperly. A product becomes vulnerable when unnecessary features are enabled, such as extra services, pages, ports, or sample applications that were never meant to run in production. It is also vulnerable when default accounts remain enabled with unchanged passwords, because attackers can guess or reuse defaults to gain immediate access. Error handling is another common contributor: overly detailed messages and stack traces leak sensitive operational details that accelerate attacker reconnaissance and targeting.
This category also overlaps with credential exposure mistakes, like embedding static keys in configuration files or build pipelines instead of using short lived credentials or identity federation. OWASP explicitly recommends avoiding embedded static secrets and preferring platform provided role based access mechanisms, because configuration mistakes around secrets are repeatedly abused in the real world. When security misconfiguration exists in a production platform, it can become the first domino that leads to account takeover, automated abuse, and large scale fraud attempts that look like "valid" traffic.
Variations of Security Misconfiguration
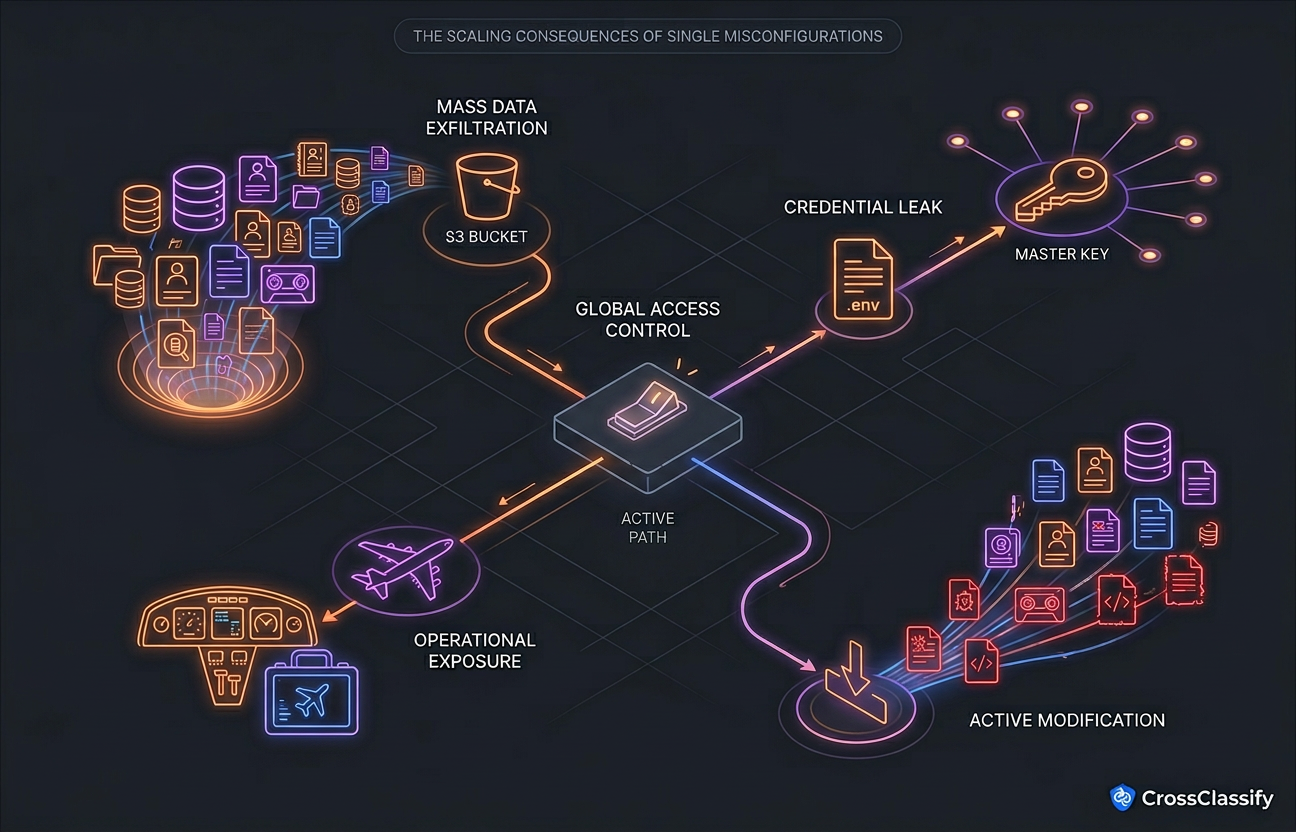
One of the most damaging forms is cloud storage misconfiguration where buckets or blobs are accidentally exposed to the public internet. A widely cited Lightspin analysis reported that 46% of analyzed AWS S3 buckets could be misconfigured and should be treated as unsafe, which shows how frequently permission complexity defeats teams under time pressure. A separate study discussed by Tripwire found that 20% of publicly accessible buckets were writable, which is especially dangerous because attackers can upload malware or replace content served to users. This variation often turns into brand damage quickly because exposed storage tends to contain logs, exports, invoices, identity documents, or backups that were never meant to leave private networks.
2. Exposed secrets and environment files in production
Another variation is when configuration files that contain secrets become publicly reachable, such as exposed environment variable files. A detailed investigation by Palo Alto Networks Unit 42 described an extortion campaign that leveraged exposed env files across at least 110,000 domains, collecting large volumes of leaked variables and cloud related credentials. Once attackers obtain keys, the misconfiguration is no longer theoretical because they can access storage, take snapshots, exfiltrate data, or ransom cloud assets. This is a configuration failure first, but it quickly becomes a fraud and account compromise problem because the stolen credentials can unlock admin panels, payment systems, and customer data.
3. Default accounts, default passwords, and forgotten hardening
Default accounts and unchanged passwords remain a classic misconfiguration, especially in admin consoles, dashboards, and internal tools that get exposed during rapid launches. Security guidance sources describe this as a pattern where default settings are left in place, making systems easy to compromise because attackers already know the defaults. This mistake often combines with missing rate controls, allowing password spraying and credential stuffing attempts to run longer than they should, which increases the probability of account takeover. Once attackers gain a foothold through defaults, they usually escalate by changing configurations, creating new users, or enabling remote access paths.
4. Unnecessary services and open management ports, including SSH port 22 exposure
OWASP explicitly calls out unnecessary ports and services as a misconfiguration driver, because every exposed surface becomes a scanning target. Leaving SSH broadly exposed, especially on port 22, is common in early stage deployments where teams prioritize uptime and convenience over hardening. This exposure is not automatically a breach, but it invites brute force attempts, credential reuse attacks, and exploitation of weak key handling in automation. The risk becomes much higher when SSH is paired with weak passwords, shared keys, or missing network segmentation that would otherwise limit blast radius.
5. Overly informative error messages and stack trace leakage
Security misconfiguration also includes a lack of centralized configuration to intercept excessive error messages. OWASP notes that stack traces and overly informative error pages can reveal sensitive implementation details, including component versions and internal paths, which speeds up targeted exploitation. This variation often shows up during production incidents because teams enable debug output temporarily and forget to disable it. Attackers then treat error pages as free reconnaissance, mapping your tech stack and identifying weaknesses faster than a normal scan would allow.
6. Configuration drift across environments
Even when teams harden production, drift happens when development, QA, staging, and production are not configured identically. OWASP recommends repeatable, automated hardening so environments match and changes are verifiable, because drift creates hidden inconsistencies that attackers discover before defenders do. In practice, drift is common after urgent fixes, scaling events, or migration projects where teams patch one environment and forget another. This variation produces incidents that feel mysterious because "it works in staging" becomes "it leaked in production" due to small configuration differences.
Real Examples of Security Misconfiguration
Security misconfiguration is one of the few OWASP categories where "small mistakes" repeatedly scale into "global headlines." The reason is simple: configuration controls are often a single checkbox or a single policy statement, so one wrong value can instantly expose terabytes of sensitive data. OWASP itself highlights cloud sharing defaults as an attack scenario where sensitive data becomes accessible if a provider or tenant settings allow open sharing. When this happens, attackers do not need advanced exploitation, they just need discovery and access.
A high profile example frequently referenced in cloud security discussions is the Lightspin analysis of AWS S3 permissions, described here https://venturebeat.com/ai/lightspin-46-of-aws-s3-buckets-could-be-misconfigured-and-unsafe where the reported finding was that 46% of analyzed buckets could be misconfigured. This matters because S3 is often used as the storage layer for backups, exports, logs, and customer documents, meaning a single policy mistake becomes a massive data exposure risk. The practical lesson is that "cloud by default" does not mean "secure by default," especially when teams inherit templates or copy policies without verifying least privilege.
Another widely discussed real world pattern is exposed env files that leak cloud credentials, and a detailed campaign write up is here https://unit42.paloaltonetworks.com/large-scale-cloud-extortion-operation/ where Unit 42 reported an operation targeting at least 110,000 domains and collecting large volumes of leaked variables. Once attackers find long lived keys, they can access cloud services directly, and misconfiguration becomes an active compromise rather than a passive weakness. This is also why OWASP recommends role based access, identity federation, and short lived credentials instead of embedding static keys in code or configuration.
A third example shows how misconfigured storage can expose extremely sensitive operational data, and the Pegasus Airlines incident is covered here https://hackread.com/pegasus-airlines-leak-tb-data-aws-s3-bucket-mess-up/ with reporting that a large S3 bucket containing airline related data was left exposed and later remediated after notification. Additional reporting noted the exposure related to an electronic flight bag environment and sensitive operational information, which highlights that misconfiguration is not only about customer data, it can also affect safety adjacent systems. The key business takeaway is that a single storage permission mistake can expose intellectual property, operations, and regulated data in one event.
Finally, "public and writable storage" is a particularly dangerous sub case because it enables active malware hosting, content replacement, and follow on attacks, and Tripwire's discussion is here https://www.tripwire.com/state-of-security/public-aws-s3-buckets-writable where it highlights that 20% of publicly accessible buckets were writable in the referenced research. Writable exposure changes the risk profile because it turns your infrastructure into an attacker controlled distribution channel. Once this happens, fraud follows quickly because attackers can inject scripts, serve malicious downloads, or replace assets used in authentication and onboarding flows.
Protection and Prevention Methods for Security Misconfiguration
A secure baseline is a documented and enforced configuration standard for every environment, including production, QA, and staging. OWASP recommends a repeatable hardening process that enables fast deployment of new environments that are appropriately locked down, while ensuring environments are configured identically with different credentials per environment. The biggest benefit is consistency because you remove "tribal knowledge" from setup and reduce the chance of someone forgetting a critical step during a rushed launch. The downside is that baseline work feels slow at first, but it quickly pays back by reducing incident response time and configuration drift.
2. Minimal attack surface and removal of unnecessary features
This method focuses on disabling or removing anything you do not need, including sample apps, unused services, and unnecessary ports. OWASP explicitly lists unnecessary ports, services, pages, accounts, testing frameworks, and privileges as common misconfiguration drivers. This approach should be applied by platform engineering, DevOps, and security teams, and it is highly effective because attackers cannot exploit what does not exist. The main tradeoff is operational convenience because developers sometimes rely on debugging features, so you need a controlled process to enable them safely only in non production contexts.
3. Patch management and configuration review tied to security advisories
Misconfiguration is often amplified by outdated components where newer security features exist but are disabled or not configured securely. OWASP recommends reviewing and updating configurations alongside security notes, updates, and patches as part of patch management, which keeps you aligned with evolving defaults and best practices. This is most effective when combined with automated scanning that flags insecure defaults introduced by upgrades. The downside is operational risk if patches are applied without testing, so mature teams pair this method with staging parity and rollout controls.
4. Segmentation and tenant isolation by architecture
Segmentation reduces blast radius when misconfiguration happens, because one exposed component does not automatically expose everything. OWASP recommends segmented architecture using separation between components or tenants, often implemented through security groups, ACLs, containerization, and network policies. This method should be applied by architects and infrastructure teams, and it is effective because it limits lateral movement after initial discovery. The tradeoff is complexity because segmentation requires clear service boundaries and careful debugging practices, especially in microservice environments.
5. Security headers and secure client directives
Many misconfigurations are not only server side, they also involve missing security directives delivered to browsers and clients. OWASP mentions missing security headers or insecure header values as part of misconfiguration risk, and these controls reduce exposure to clickjacking, mixed content, and some classes of injection amplification. This method should be applied by app teams and platform teams together, because headers often live in reverse proxies, gateways, or application frameworks. The downside is occasional compatibility issues with legacy clients, but the security gains are usually worth the controlled rollout.
6. Automated verification and continuous configuration assessment
OWASP recommends an automated process to verify configuration effectiveness in all environments, and if automation is not possible, at least annual manual verification. Continuous assessment is effective because it detects drift and accidental exposure quickly, which is essential when teams scale infrastructure and ship frequently. This is typically owned by security engineering and DevSecOps teams, and it works best when it is integrated into CI CD and cloud inventory workflows. The tradeoff is alert fatigue if rules are noisy, so successful programs prioritize risk based alerts and clear ownership for remediation.
7. Secure secrets strategy using short lived credentials and identity federation
OWASP explicitly recommends using identity federation, short lived credentials, or role based mechanisms instead of embedding static keys or secrets in code, configuration files, or pipelines. This directly addresses the real world pattern where leaked env files and exposed configs give attackers long term access. This method should be applied by platform teams and engineering leaders because it affects how services authenticate across the stack. The tradeoff is implementation effort, but the benefit is huge because it turns many credential leaks into short window events rather than persistent compromise.
Protection Tools for Security Misconfiguration
Security misconfiguration prevention is easiest when tools support visibility, enforcement, and verification, rather than relying only on manual review. Security configuration assessment tooling is designed to discover unsafe settings at scale and support hardening workflows across endpoints, servers, and cloud assets. Vendor ecosystems describe this as continuous configuration checks that help teams reduce risk and maintain compliance over time.
For cloud storage and permission drift, native cloud monitoring can help teams detect risky policy changes early, such as monitoring S3 bucket policy changes using cloud audit logs and alerting mechanisms. A practical reference is here https://aws.amazon.com/blogs/storage/rapid-monitoring-of-amazon-s3-bucket-policy-changes-in-aws-environments/ where AWS describes monitoring and alerting patterns for policy updates. This does not replace least privilege design, but it helps catch accidental changes before they become public exposure events. When combined with automated hardening checks and remediation workflows, these tools reduce the time window in which attackers can exploit misconfiguration.
For exposed secrets and credential leaks, secret scanning and configuration validation tools are essential, but they still miss a key fact: attackers often look valid once they have credentials. MITRE describes credential hunting in files as a common attacker technique, which shows why configuration mistakes around secrets are repeatedly exploited. Tools can reduce exposure, but detection must also focus on behavior, session anomalies, and device level trust signals. That is where CrossClassify becomes a meaningful layer in a security misconfiguration prevention platform.

The Gap That Still Exists: Why Security Misconfiguration Still Turns Into Real Breaches
Most organizations treat security misconfiguration as a checklist problem, and checklists do help, but reality is harsher. Configuration is often set in the chaotic early days of a product launch when teams are busy shipping features, meeting deadlines, and keeping systems alive under load. Later, when traffic grows into thousands or millions of users, teams focus on scalability, uptime, and product velocity, and the early configuration shortcuts remain hidden until an attacker discovers them. What you took lightly in the beginning can come back as a strong security punch later, jeopardizing the entire business, because misconfiguration issues scale with your success.
The deeper gap is that most misconfiguration programs are static, while attackers are adaptive. A misconfigured admin console, a leaked secret, or an exposed storage bucket does not always look like a vulnerability in logs until it is exploited by a real human or a bot at scale. Once attackers have valid credentials, the system often treats them like normal users, which is why you need controls that validate identity continuity, not only authentication validity. CrossClassify closes this gap by adding device fingerprinting and behavioral biometrics as trust layers that detect exploitation patterns even when the configuration mistake already exists.

OWASP highlights default accounts, unnecessary features, open services, and cloud permission issues as typical misconfiguration triggers, and attackers often exploit them through repeated probing across many sessions. Device fingerprinting gives you a stable way to recognize returning devices, detect suspicious device changes, and connect sessions that would otherwise look unrelated. CrossClassify's device fingerprint intelligence is designed to detect devices, reveal fraud, and support continuous monitoring, which is valuable when misconfiguration leads to suspicious access attempts from new or rapidly rotating devices. The practical win is that even if a configuration weakness exposes an entry point, you can still block or challenge access based on device reputation, device reuse, and device anomaly signals before the attacker escalates.
Device fingerprinting also helps in cloud abuse scenarios caused by leaked secrets, because attackers often pivot through multiple tools, IP ranges, and automation stacks, yet device and client characteristics still reveal patterns. If your platform suddenly sees admin console access from never seen devices, or repeated configuration endpoints being hit by device clusters, that is a strong indicator of exploitation. CrossClassify can convert those observations into risk scoring and real time decisions, which gives security teams time to fix the configuration while still containing the attack. This approach turns misconfiguration from "we must patch immediately or we are doomed" into "we can contain and control blast radius while we remediate."
Behavioral Biometrics should be a core layer in a Security Misconfiguration prevention platform
Security misconfiguration is often invisible until behavior changes, because the system may still respond correctly to requests even when it is overly permissive. Behavioral biometrics focuses on how sessions behave, including navigation patterns, interaction rhythm, step sequencing, and anomaly signatures that differ between legitimate humans and automated abuse. CrossClassify explicitly positions behavioral biometrics as a way to fuse device signals with behavioral patterns to preserve trustworthiness across channels, including cases where VPNs, shared hardware, or private browsing would otherwise break continuity. This matters because misconfiguration exploitation is rarely one request, it is a sequence of probing, scanning, and escalation behaviors that behavioral models detect earlier than manual review.
Only with behavioral biometrics analysis across varied log types and session flows can you reach a high level of confidence that your system is configured properly in practice, not only on paper. When behavior deviates from normal, such as abnormal admin navigation, repeated error triggering to harvest stack traces, or high velocity attempts that look like scripted enumeration, it becomes a red signal even before data loss is confirmed. This is especially important for credential stuffing adjacent scenarios where misconfiguration, such as missing throttling or verbose error output, increases success rates for attackers. CrossClassify helps teams detect these deviations and respond with friction or blocking at the right moments, reducing both fraud impact and false positives.
Integrating Device Fingerprinting and Behavioral Biometrics for Security Misconfiguration makes applications safer
Security misconfiguration is a setup failure, but exploitation is a behavior story. That is why the strongest strategy combines configuration hardening with continuous trust evaluation at runtime. When you integrate device fingerprinting and behavioral biometrics, you gain the ability to detect exploitation even when the attacker has valid credentials and even when misconfiguration created the opening. This combination helps application owners protect onboarding, authentication, admin workflows, and sensitive actions against account takeover, account opening abuse, and bot driven exploitation that often follows misconfiguration incidents.
CrossClassify's approach aligns with the OWASP message that secure configuration must be repeatable and verifiable, because runtime signals become part of verification. You can confirm whether changes reduce abnormal patterns, whether suspicious device clusters disappear, and whether high risk automation attempts are blocked. Over time, this becomes a closed loop: configuration controls reduce exposure, while behavioral and device intelligence reduces exploitation success and highlights where misconfiguration still exists. In other words, you do not only harden the system, you continuously prove it is behaving securely under real traffic.
Conclusion
Security Misconfiguration is ranked A02 in OWASP Top 10:2025 for a reason: OWASP reports that every tested application showed some form of misconfiguration, and the category is associated with large volumes of CWE occurrences and CVEs. Misconfiguration is not only about forgetting a secure header or leaving an extra service enabled, it is about how small defaults can compound into large scale exposure once your product grows. Real incidents involving public storage, leaked credentials, and exposed operational systems show that configuration mistakes can become business ending events if they are discovered by attackers first.
The most reliable strategy is layered: harden configurations, automate verification, and reduce drift, but also assume attackers will test your system in production. Device fingerprinting and behavioral biometrics close the runtime gap by detecting suspicious devices and abnormal session behavior even when credentials are valid or a misconfiguration already exists. CrossClassify brings these layers together so security teams can contain exploitation while engineers remediate the underlying settings, which is crucial during high pressure growth phases. To explore how this works in practice, the behavioral biometrics approach is explained at https://www.crossclassify.com/solutions/behavioral-biometrics/ and it becomes even stronger when combined with device intelligence described at https://www.crossclassify.com/solutions/device-fingerprint/ because identity continuity and behavior context are what attackers struggle to fake consistently.
Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Related articles
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required