Last Updated on 25 Apr 2026
The Smart Account Takeover Protection Layer for Indeed Style Employer Accounts
Share in

Introduction
Employer and recruiter accounts are high value targets because they can post jobs, message candidates, access resumes, and represent a company’s hiring brand. When attackers compromise or fake these accounts, they can turn a trusted recruitment channel into a tool for phishing, data theft, fake job scams, and brand impersonation. This is why account takeover protection for recruitment platforms must protect the full employer journey, from signup and login to posting and messaging.
Searches around “Indeed employer account,” “Indeed verification code,” “why does Indeed keep asking for verification,” and “how to create an Indeed employer account” reveal how important account security has become in hiring systems. This article discusses Indeed related search behavior and similar recruitment platform concerns, not a partnership with Indeed. The goal is to show why recruiter account security requires identity aware fraud detection, not only passwords and one time verification codes.
CrossClassify helps recruitment platforms protect employer accounts by combining account takeover protection, account opening protection, device fingerprinting, behavioral biometrics, and continuous risk scoring. The CrossClassify recruitment solution connects these controls to fake recruiter protection and recruitment fraud prevention. This makes it relevant for job boards, staffing portals, employer dashboards, and hiring marketplaces.
What Indeed Related Keywords Reveal About Account Security
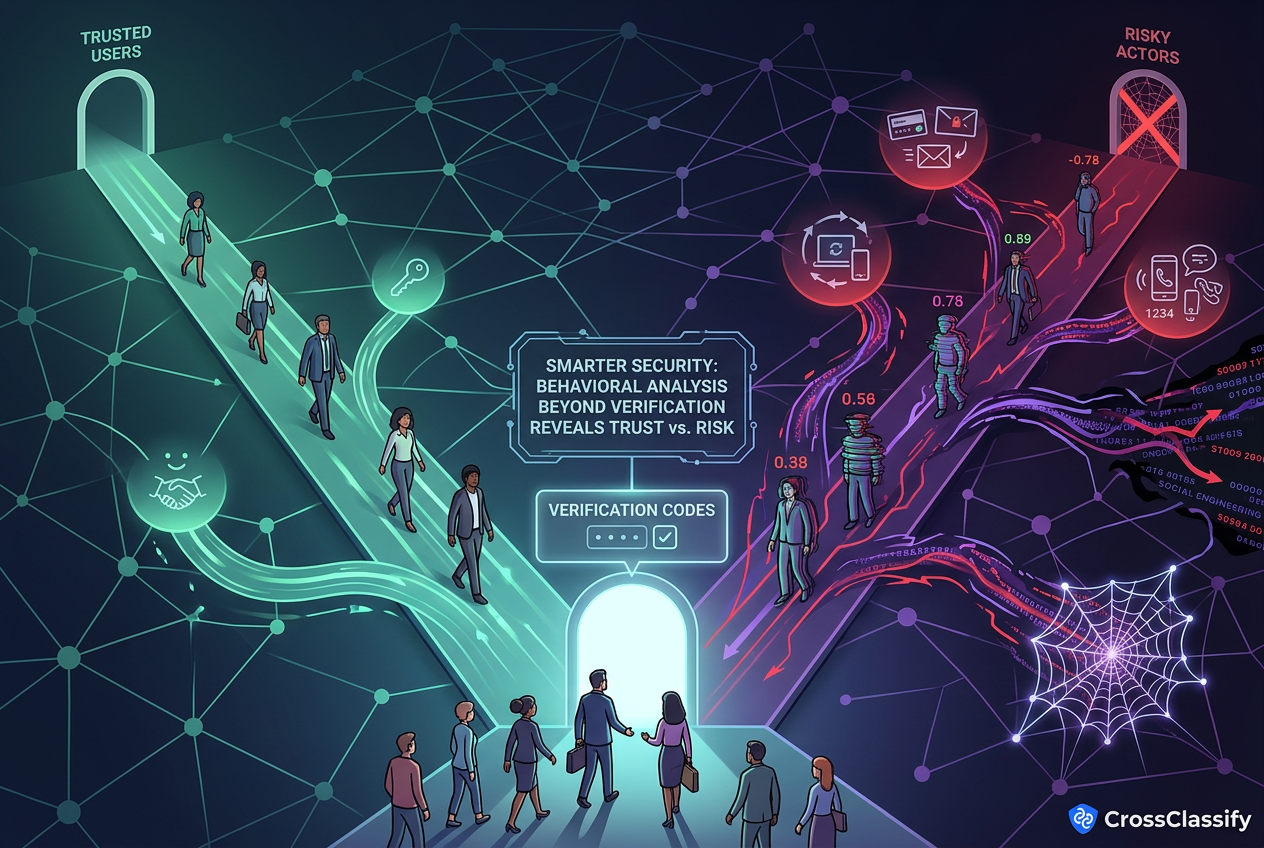
Keywords such as “Indeed verification code,” “why does Indeed require phone number,” “why did my Indeed account disappear,” and “how to create an Indeed employer account” show that users already connect recruitment with identity verification. Employers want easy access, but platforms must also protect recruiter accounts from suspicious creation, suspicious login, and suspicious usage. This tension creates the need for smarter security that can separate real employers from risky actors without adding unnecessary friction for trusted users.
Verification codes can help, but they are not enough on their own. Attackers may use stolen credentials, compromised emails, temporary phone numbers, social engineering, or device switching to bypass basic checks. A recruitment platform needs to know whether the account behavior after verification still looks trustworthy.
CrossClassify can support this by scoring every important account event. The account takeover protection solution helps detect risky login behavior, suspicious device changes, and abnormal activity after access. This gives recruitment platforms a deeper protection layer beyond simple verification prompts.
Why Recruiter Accounts Are Attractive to Attackers
A compromised recruiter account gives attackers direct access to candidate trust. Candidates are more likely to reply when a message appears to come from a real employer, especially if the company name looks familiar. This makes recruiter account takeover dangerous because attackers can use platform credibility to make scams more convincing.
Attackers can use recruiter accounts for fake job posts, phishing links, candidate data theft, fake interview requests, and brand impersonation. They can also redirect candidates to external forms that collect personal data, identity documents, or payment information. The attack may look like normal recruiting activity unless the platform monitors account behavior and risk changes.
CrossClassify helps detect these patterns by watching for suspicious device, IP, geo, behavior, and posting changes. The recruitment fraud protection solution is useful because it focuses on fraud risks specific to hiring environments. This means platforms can detect when a recruiter account starts behaving like a scam channel.
Account Takeover Risks in Recruitment Platforms
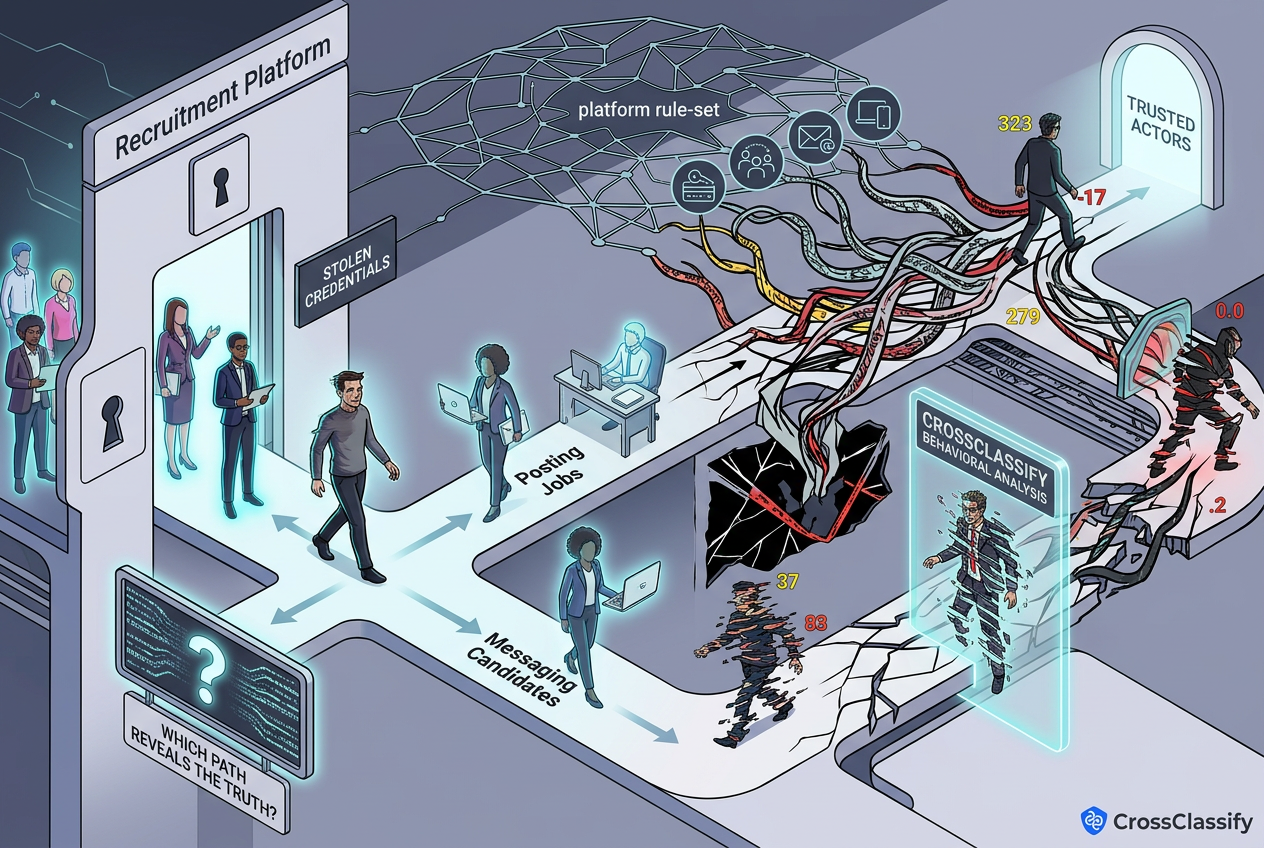
Stolen recruiter credentials can enter the platform through phishing, password reuse, malware, or leaked account data. Once attackers have access, they may post fake jobs, message candidates, or change account settings to support fraud. The account may look legitimate because it has history, employer details, and previous activity.
CrossClassify can detect suspicious login and post login behavior by comparing device, location, and behavior patterns against expected account activity. The account takeover protection solution helps platforms identify when a trusted account is accessed in a risky way. This allows earlier intervention before attackers misuse the recruiter identity.
Suspicious login locations
Suspicious login locations can reveal account takeover attempts or risky access behavior. A recruiter account that normally logs in from one region but suddenly appears from an unrelated location, anonymized network, or risky IP range should receive a higher risk score. Location alone should not decide the outcome, but it is an important signal when combined with device and behavior changes.
CrossClassify combines geo analysis with device fingerprinting and behavioral signals to reduce false positives. The device fingerprinting solution helps confirm whether the same trusted device is being used or whether access has shifted to a suspicious environment. This improves recruiter account security without blocking legitimate users only because they travel.
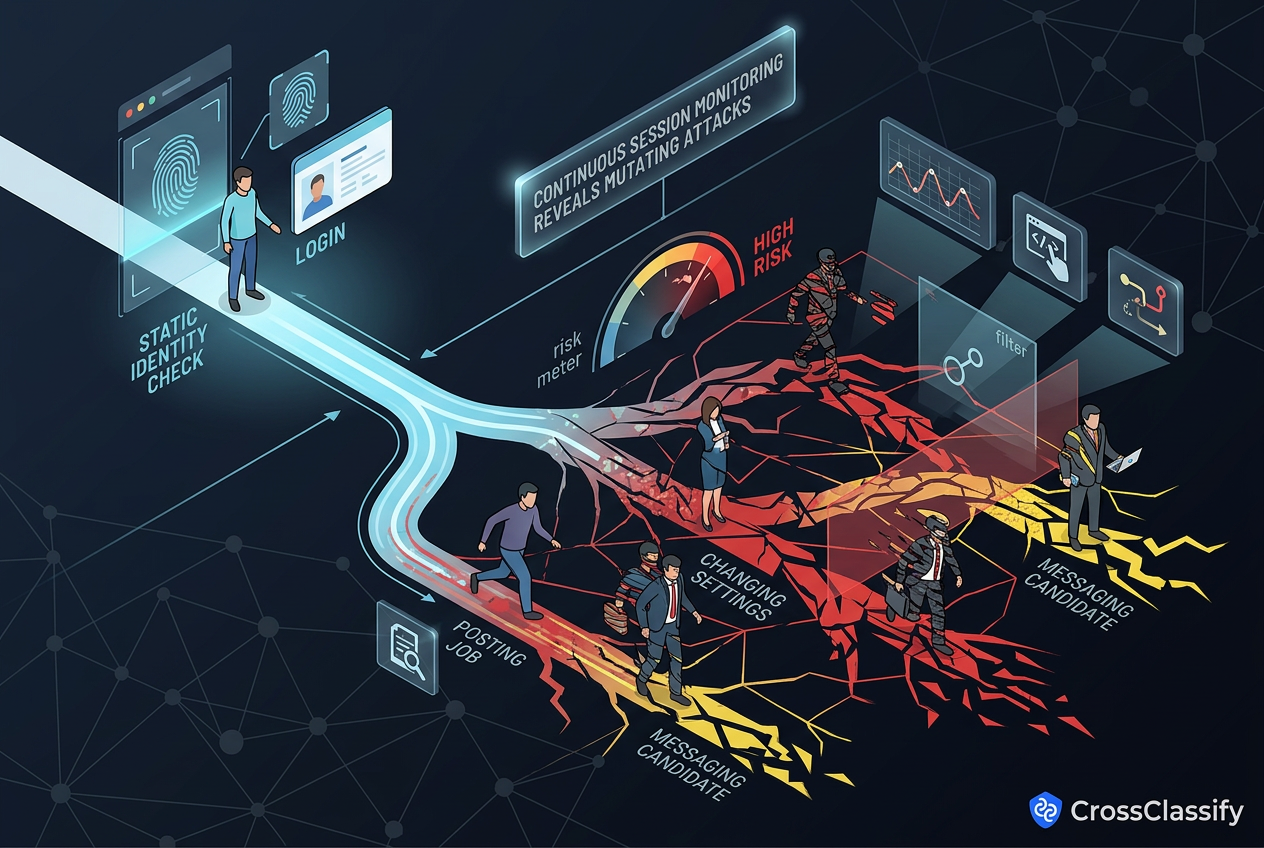
Device changes after login
Device changes after login can indicate that an attacker has gained access or that an account is being shared in risky ways. If a recruiter account logs in from a new device and immediately starts posting jobs, changing contact details, or messaging candidates, the platform should treat that behavior as higher risk. Device changes are especially important in recruitment because a single employer account can affect many job seekers.
CrossClassify can track device trust and detect sudden device shifts that happen around sensitive actions. The account takeover protection page supports this kind of protection for accounts that must remain trusted after login. This helps platforms detect account misuse during the active session, not only at the login screen.
Hijacked candidate messaging
Candidate messaging is one of the most valuable tools attackers can abuse after account takeover. A hijacked recruiter account can send phishing links, request documents, redirect candidates to external sites, or ask for payments under the appearance of a hiring process. This can damage both candidate safety and employer brand reputation.
CrossClassify can monitor messaging behavior for abnormal velocity, repeated templates, suspicious links, and behavior that does not match the recruiter’s usual pattern. The behavioral biometrics solution helps detect when user behavior shifts in a way that suggests account misuse. This makes candidate messaging safer without relying only on keyword filters.
Fake employer account creation
Fake employer account creation is closely related to account takeover because attackers can either compromise existing accounts or create new employer identities. Fake accounts may use stolen company names, temporary contact information, suspicious devices, and copied job templates. If the platform does not score signup risk, fake employer accounts can begin posting scams quickly.
CrossClassify supports signup risk checks by analyzing device, IP, geo, behavior, and account creation patterns. The account opening protection solution helps platforms detect suspicious employer account creation before fake jobs reach candidates. This is critical for recruitment platforms that want prevention rather than cleanup.

How CrossClassify Protects Employer Accounts
CrossClassify protects employer accounts by treating account security as a continuous journey. The risk does not end after signup or login because attackers can behave normally at first and become risky after gaining access. Continuous risk scoring helps platforms detect suspicious activity across account creation, login, session behavior, posting behavior, and candidate messaging.
Account takeover protection helps detect stolen recruiter credentials and suspicious access patterns. Account opening protection helps detect fake employer accounts before they can post jobs. Device fingerprinting, behavioral biometrics, and bot and abuse protection help identify repeated fraud, scripted behavior, and coordinated recruiter abuse.
The CrossClassify recruitment solution connects these capabilities to recruitment fraud prevention. It gives hiring platforms a practical way to detect fake recruiters, suspicious employer accounts, and account misuse. This helps protect candidates, employers, and marketplace trust at the same time.
Recommended Protection Workflow
A signup risk check evaluates whether a new employer account looks legitimate before it receives full platform access. The system can analyze device fingerprint, IP risk, geo consistency, email pattern, company information, and behavior during registration. This helps stop suspicious employer account creation early.
CrossClassify can assign a risk score at signup and route suspicious accounts to review, step up verification, or blocking. The account opening protection solution is designed for this type of early fraud prevention. For recruitment platforms, this means fake recruiter accounts can be detected before they post jobs or message candidates.
Login risk check
A login risk check evaluates every access attempt using device, IP, geo, and behavior signals. Even if the password and verification code are correct, the platform should ask whether the login context makes sense. A login from a new device, risky IP, unusual location, or abnormal interaction pattern should raise the risk score.
CrossClassify helps recruitment platforms make login security more adaptive. The account takeover protection solution supports risk based detection that can trigger review or additional verification when access looks suspicious. This protects recruiter accounts without creating unnecessary friction for every normal login.
Session monitoring
Session monitoring detects suspicious behavior after the user logs in. This is important because many attacks only become visible when the account starts posting jobs, changing settings, or messaging candidates. A platform that stops monitoring after login can miss the most harmful part of the attack.
CrossClassify can detect behavior changes during the session and increase risk scores when activity becomes abnormal. The behavioral biometrics solution helps identify suspicious interaction patterns that may not appear in static identity checks. This gives platforms a way to respond before candidate harm spreads.
Posting behavior monitoring
Posting behavior monitoring identifies sudden or unusual job posting activity. A recruiter account that posts many jobs quickly, changes industry focus, uses repeated templates, or adds suspicious external links may need review. These signals are especially important when a previously normal employer account changes behavior after login.
CrossClassify can connect posting behavior with device, session, and account history. The recruitment fraud protection solution helps platforms detect fake recruiter behavior in the context of hiring activity. This supports faster action against suspicious job posts and compromised recruiter accounts.
Alerting and notification
Alerting and notification help fraud and trust teams act before suspicious activity becomes a larger incident. Alerts should be based on meaningful risk signals rather than simple volume, so teams are not overwhelmed by noise. Strong alerts help teams review risky accounts, pause suspicious posting, and protect candidates faster.
CrossClassify can send risk based alerts when account takeover signals, fake recruiter signals, or suspicious activity patterns appear. The bot and abuse protection solution is also useful when automated activity creates bursts of suspicious postings or messaging. This helps platforms respond quickly when abuse begins to scale.
Conclusion
Recruitment platforms need identity aware account security, not only passwords, verification codes, and manual review. Employer accounts can be abused for fake job posts, candidate phishing, brand impersonation, and sensitive data collection. Account takeover protection for recruitment platforms must include signup checks, login risk, session monitoring, posting behavior, and alerting.
CrossClassify helps platforms protect employer accounts with account takeover protection, account opening protection, device fingerprinting, behavioral biometrics, and continuous risk scoring. The CrossClassify recruitment solution brings these controls into the hiring fraud context. For platforms managing employer accounts, this creates a stronger defense against compromised recruiters and fake employer identities.
Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required
