Last Updated on 26 Feb 2026
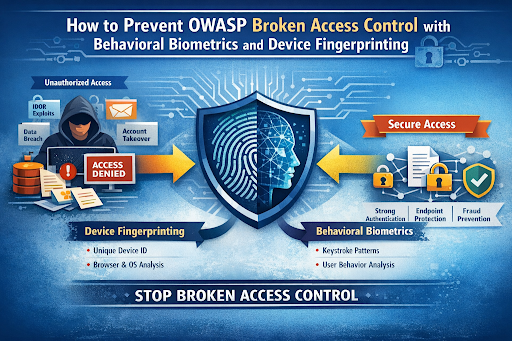
How to Prevent OWASP Broken Access Control with Behavioral Biometrics and Device Fingerprinting
Share in
Introduction
The OWASP Top 10 is one of the most authoritative security awareness documents in the world. It highlights the most critical web application security risks based on global data, real world breach analysis, and expert consensus. In the 2025 edition, Broken Access Control remains one of the most severe and frequently exploited vulnerabilities affecting modern applications. For organizations seeking application security solutions for OWASP Top 10 compliance, this category represents a high priority risk area.
Broken Access Control is responsible for a significant percentage of reported vulnerabilities. According to OWASP community data from previous editions, access control flaws were present in more than 90 percent of tested applications, and they continue to be among the most exploited weaknesses in real world attacks. These vulnerabilities often lead to account takeover, account opening abuse, bot and abuse frauds, and large scale data exposure incidents. For application owners searching for enterprise grade broken access control protection tools, the challenge is not only to configure roles and permissions but to continuously monitor abnormal behavior across sessions and devices.
This is where advanced protection layers such as behavioral biometrics fraud detection software and device fingerprinting for web application security become essential components of a modern defense strategy.
OWASP Top 10 2025 List Overview
Below is a brief explanation of each OWASP Top 10 2025 category to provide context before focusing on Broken Access Control.
•
A01 2025 Broken Access Control
This category covers failures in enforcing authorization policies. It includes vertical privilege escalation, horizontal privilege escalation, and direct object manipulation such as IDOR. When access control is broken, attackers can access sensitive data or administrative functions. This often leads to account takeover protection failures and unauthorized data exposure.•
A02 2025 Security Misconfiguration
This refers to improperly configured servers, cloud services, APIs, or security headers. Default credentials, open S3 buckets, and exposed admin panels are common examples. Misconfigurations create easy entry points for attackers. Proper configuration management and continuous monitoring are essential to reduce this risk.•
A03 2025 Software Supply Chain Failures
This category includes compromised third party libraries and dependency vulnerabilities. If a malicious or vulnerable package is included in the application, it can introduce hidden backdoors. Continuous dependency scanning and verification are critical countermeasures. Organizations must monitor their CI CD pipelines for tampering risks.•
A04 2025 Cryptographic Failures
Weak or outdated encryption algorithms expose sensitive data. Improper key management can result in complete compromise of encrypted assets. Cryptographic failures frequently lead to compliance violations. Secure key storage and strong encryption standards are mandatory.•
A05 2025 Injection
Injection flaws such as SQL injection and command injection allow attackers to execute unintended commands. They often result in data theft or system compromise. Input validation and parameterized queries are effective mitigation strategies. Security testing must include injection scenarios.•
A06 2025 Insecure Design
Insecure design refers to architectural flaws that cannot be fixed with simple patches. Lack of threat modeling often results in insecure workflows. Secure by design principles should be applied early in development. Business logic abuse often stems from insecure design decisions.•
A07 2025 Authentication Failures
Weak password policies and broken session management fall into this category. These issues commonly lead to account takeover attacks. Multi factor authentication and behavioral monitoring help mitigate the risk. Continuous authentication can further strengthen security.•
A08 2025 Software or Data Integrity Failures
This involves trusting data without verifying its integrity. Unsigned updates and insecure CI pipelines are common examples. Data tampering can go undetected without proper integrity checks. Secure update mechanisms are required.•
A09 2025 Security Logging and Alerting Failures
Without proper logging, attacks can go unnoticed. Lack of monitoring prevents early detection of breaches. Security teams rely on logs to investigate incidents. Real time alerting reduces dwell time.•
A10 2025 Mishandling of Exceptional Conditions
Improper error handling can expose sensitive information. Stack traces and verbose errors give attackers insights into system structure. Applications must sanitize error messages. Robust exception handling prevents information leakage.
Definition of Broken Access Control
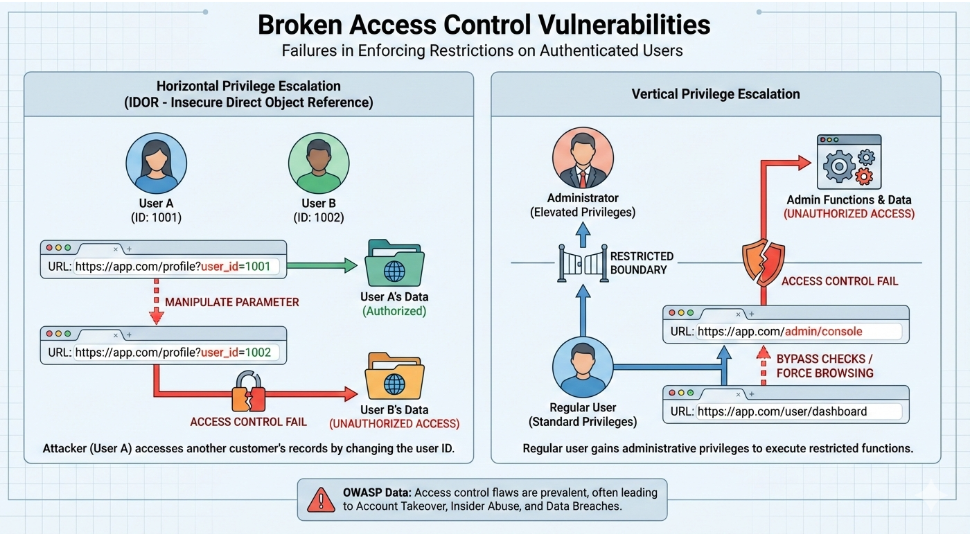
Broken Access Control refers to failures in enforcing restrictions on what authenticated users are allowed to do. Access control mechanisms must ensure that users can only access resources and perform actions according to defined policies. When these controls fail, attackers can access unauthorized data or execute restricted functions.
One of the most common examples is IDOR, which stands for Insecure Direct Object Reference. In this case, an attacker manipulates parameters such as user id in a URL to access another user's data. For example, changing user id from 1001 to 1002 may expose another customer's records. This horizontal privilege escalation is a classic Broken Access Control vulnerability.
Vertical privilege escalation is another variation, where a regular user gains administrative privileges. According to OWASP community testing data, access control flaws are among the most prevalent issues discovered in application assessments. These vulnerabilities frequently lead to account takeover, insider abuse, and large scale data breaches.
Variations of Broken Access Control
Broken Access Control can manifest in multiple forms, each with severe consequences.
IDOR and Object ManipulationInsecure Direct Object Reference occurs when applications expose internal identifiers without verifying ownership. Attackers exploit this by modifying parameters such as account numbers or file paths. Studies from OWASP testing initiatives show IDOR vulnerabilities appear in a large portion of web applications. Proper server side authorization checks are essential.
Endpoint and API Vulnerabilities
Modern applications rely heavily on APIs. If endpoints do not enforce strict authorization rules, attackers can directly call privileged APIs. Rate limit bypass and token reuse often amplify this problem. API level broken access control is particularly dangerous in mobile and SaaS platforms.
Weak Authentication and Session Controls
Although authentication and access control are distinct, weak authentication enables access control abuse. Stolen sessions or hijacked tokens allow attackers to bypass intended restrictions. According to industry reports, a significant percentage of breaches involve credential abuse. Strong session validation and behavioral monitoring are necessary defenses.
Privilege Escalation and Role Abuse
Improper role configuration can allow users to escalate privileges. Insider threats often exploit such weaknesses. Organizations must implement strict role based access control combined with continuous monitoring. Static role definitions alone are insufficient.
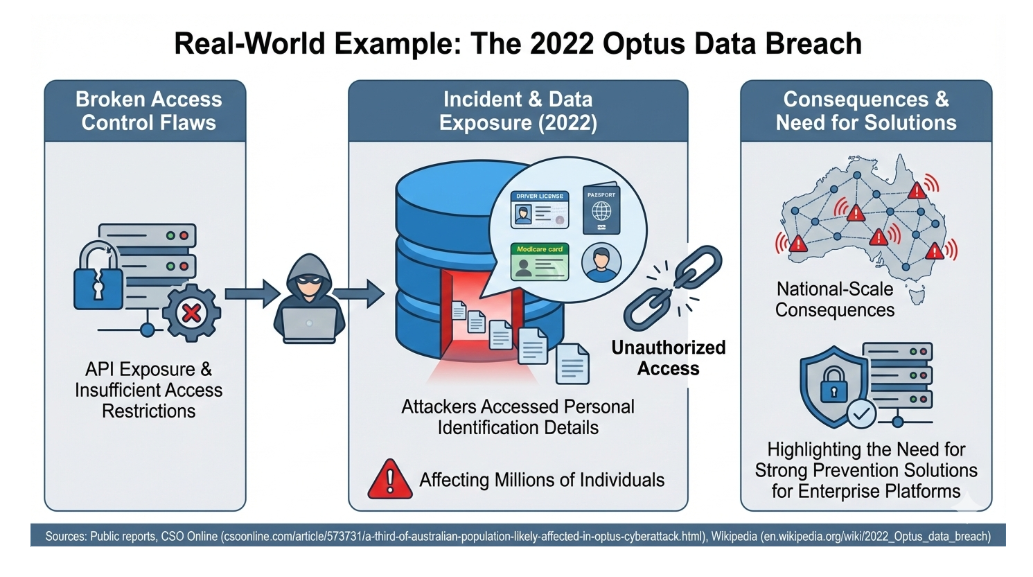
Real Examples of Broken Access Control
One of the most significant real world examples connected to access control failures is the 2022 Optus data breach involving Optus. Public reports from CSO Online describe how sensitive customer data was exposed, affecting millions of individuals. Analysis available at this CSO Online report explains how API exposure and insufficient access restrictions contributed to the breach.
Further documentation available at Wikipedia's Optus breach overview outlines how attackers accessed personal information including identification details. This incident demonstrates how broken access control and API misconfiguration can lead to national scale consequences. It highlights the need for strong broken access control prevention solutions for enterprises operating large digital platforms.
Protection and Prevention Methods for Broken Access Control
All access requests should be denied unless explicitly permitted. This reduces the risk of accidental exposure. Developers must implement explicit authorization checks for every endpoint. The benefit is strong baseline protection, while the downside is increased implementation complexity.
Rate Limit Endpoints
Rate limiting reduces brute force and enumeration attempts. It limits how frequently APIs can be called. This protects against automated bot and abuse frauds. However, rate limiting alone does not stop sophisticated attackers using distributed infrastructure.
Strong Authentication
Multi factor authentication significantly reduces account takeover risk. It ensures that stolen passwords alone are insufficient. It is highly effective against credential stuffing. However, MFA fatigue attacks and phishing can still bypass it.
Role Based Access Control and Least Privilege
RBAC ensures users only have necessary permissions. Least privilege minimizes damage in case of compromise. Implementation requires careful role design. Maintenance complexity is a challenge in large enterprises.
Protection Tools for Broken Access Control
DAST tools test running applications from an external perspective. They simulate attacks to identify vulnerabilities including access control flaws. DAST is useful in staging environments. However, it may miss logic level authorization errors.
ZAP Zed Attack Proxy
OWASP ZAP is an open source security testing tool designed for finding vulnerabilities in web applications. It can detect certain access control issues through active scanning. ZAP is accessible and widely used. It requires skilled configuration for accurate results.
SAST Static Application Security Testing
SAST analyzes source code for vulnerabilities. It identifies insecure patterns before deployment. It is valuable during development phases. However, it may not detect runtime authorization bypass issues.
The Gap That Still Exists in Broken Access Control Defense
Even with rate limiting, strong authentication, RBAC, and security testing, attackers still find ways to bypass controls. Insider threats, session hijacking, endpoint manipulation, and sophisticated account takeover campaigns exploit behavioral gaps rather than configuration flaws. Just like a football team relies on a goalkeeper to compensate for defensive mistakes, cybersecurity needs a final intelligent layer of defense.
This final layer must detect abnormal behavior even when credentials are valid. It must recognize suspicious devices even when sessions appear legitimate. Traditional access control mechanisms cannot always detect subtle abuse patterns. This is where CrossClassify becomes the intelligent goalkeeper of your application.
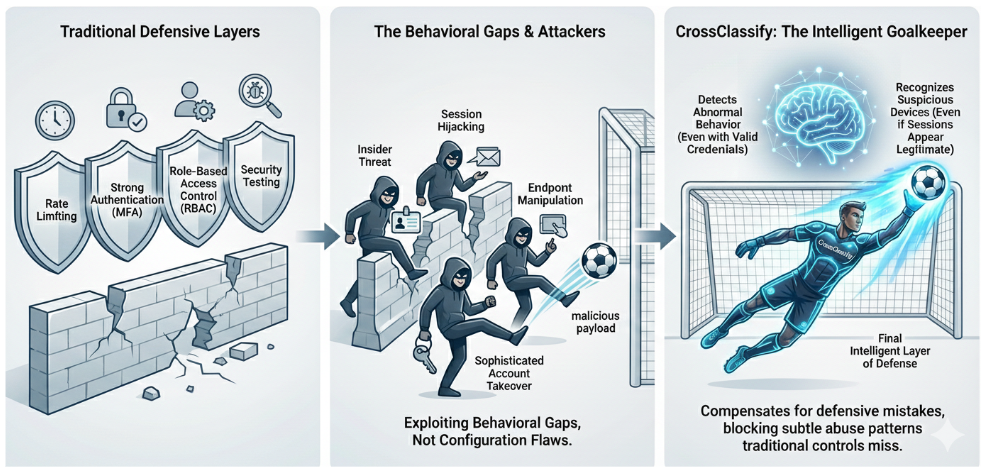
Device Fingerprinting as a Core Protection Layer
Device fingerprinting for broken access control prevention creates a unique identifier for each device interacting with the application. Even if attackers use stolen credentials, their device characteristics reveal anomalies. CrossClassify provides advanced fingerprinting technology that analyzes browser, network, and behavioral signals. More details can be explored at CrossClassify Device Fingerprinting where device intelligence is described as a proactive defense mechanism.
By linking user accounts to trusted device profiles, organizations can detect unauthorized device access attempts. This approach significantly strengthens broken access control protection. Device fingerprinting also supports bot and abuse protection strategies by identifying automated infrastructures. It reduces account takeover and insider attack risks by continuously evaluating device reputation.
Behavioral Biometrics as Continuous Authorization
Behavioral biometrics fraud detection software analyzes how users interact with applications. It observes typing patterns, mouse movements, navigation flows, and session timing. Even if credentials are correct, abnormal behavior can indicate compromise. CrossClassify integrates this approach into its platform as detailed at CrossClassify Behavioral Biometrics where continuous authentication is emphasized.
Behavioral biometrics adds a dynamic authorization layer beyond static roles. It detects subtle anomalies associated with account takeover, insider misuse, and bot automation. This significantly reduces the window of exposure caused by broken access control. Continuous monitoring ensures that authorization is not just a one time check but an ongoing validation process.
Integrating Device Fingerprinting and Behavioral Biometrics
Combining device fingerprinting and behavioral biometrics creates a powerful defense against OWASP Broken Access Control. Device intelligence verifies whether the access originates from a trusted environment. Behavioral analytics ensures that the user behavior aligns with historical patterns.
This dual layer approach addresses insider attacks, session hijacking, endpoint abuse, and account takeover scenarios. Even if access control logic is partially bypassed, abnormal signals trigger alerts and automated responses. For enterprises seeking commercial broken access control protection solutions, this integrated strategy provides comprehensive risk reduction.
Conclusion
Broken Access Control remains one of the most critical vulnerabilities in modern applications. Traditional measures such as RBAC, MFA, and rate limiting are necessary but not sufficient. Advanced threats require intelligent detection layers that analyze devices and behavior in real time.
CrossClassify provides enterprise grade solutions that combine device fingerprinting and behavioral biometrics to close the security gap. Organizations can explore these capabilities further at Device Fingerprinting and Behavioral Biometrics. By integrating these technologies, application owners can significantly reduce the risk of account takeover, bot abuse, and unauthorized data exposure associated with OWASP Broken Access Control.
Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required
