Last Updated on 30 Mar 2026
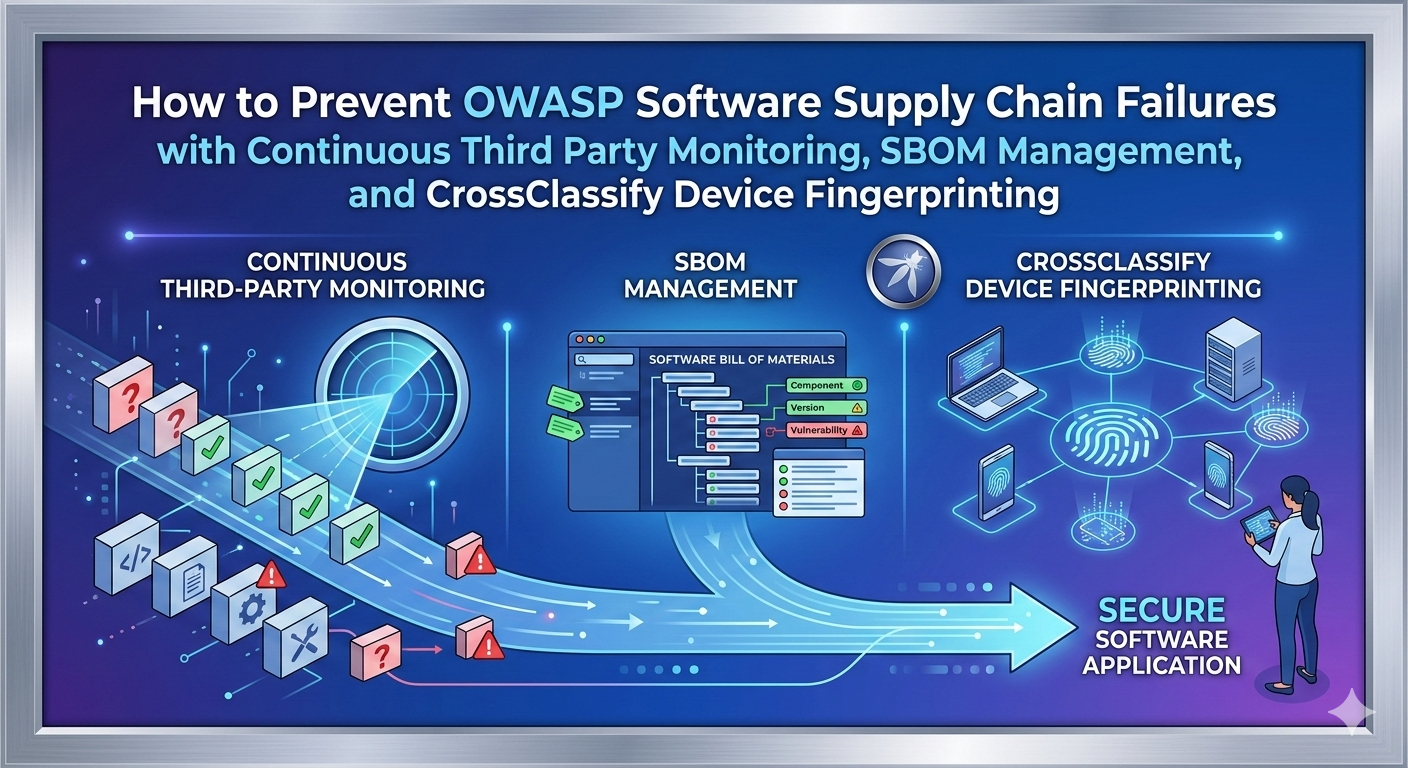
How to Prevent OWASP Software Supply Chain Failures with Continuous Third Party Monitoring, SBOM Management, and CrossClassify Device Fingerprinting
Share in
Introduction
OWASP Top Ten is one of the most widely used awareness references for web application security. It is not a compliance checklist, it is a prioritized map of where modern applications most often break in ways attackers can reliably exploit. The 2025 release keeps the focus on real world risk patterns across design, code, configuration, and operations, which is exactly where long tailed commercial intent searches tend to lead security leaders and product owners.
In OWASP Top Ten 2025, A03 Software Supply Chain Failures is ranked as the third category, and OWASP notes it was top ranked in the community survey with exactly fifty percent of respondents ranking it number one. OWASP also reports this category has the highest average incidence rate in the contributed data, and the score table shows hundreds of thousands of total occurrences, which is a strong signal that this is not an edge case. This is the world of third party code, third party build tools, third party pipelines, and third party SaaS that quietly becomes part of your production attack surface.
The fraud impact is usually indirect but brutal. A supply chain compromise commonly becomes credential theft, session hijacking, bot and abuse automation, and large scale account takeover once the malicious component reaches production and starts behaving like a trusted part of the system. That is why the protection strategy needs both preventive controls, like SBOM and dependency governance, and detective controls that continuously monitor for abnormal behavior even when the attacker is using trusted software paths.
Top 10:2025 List
•
A01:2025 Broken Access Control
This risk is about users reaching data or actions they should never be allowed to reach, often through ID based access errors. It stays at the top because it is easy to miss in large systems and it has immediate business impact once exploited.•
A02:2025 Security Misconfiguration
This category covers insecure settings across cloud, app servers, frameworks, and platform services that turn into real exposures at scale. It is a frequent root cause because speed and complexity create configuration drift across environments.•
A03:2025 Software Supply Chain Failures
This category covers compromises in building, distributing, or updating software, including third party components and tooling. It is dangerous because one compromised dependency can propagate across many downstream products that implicitly trust it.•
A04:2025 Cryptographic Failures
This risk is about weak or misused cryptography, such as sensitive data exposure due to poor encryption choices or key handling. It often appears as a symptom of deeper design or operational failures.•
A05:2025 Injection
Injection happens when untrusted input is interpreted as code or commands in a backend or interpreter. It persists because modern apps still compose many parsers, query layers, and templates that are hard to uniformly secure.•
A06:2025 Insecure Design
This category highlights architectural and product design decisions that create systemic weaknesses. It is a reminder that secure coding cannot compensate for insecure requirements, flows, and trust boundaries.•
A07:2025 Authentication Failures
This includes weaknesses in login, session management, and identity flows that allow impersonation. It matters because attackers constantly industrialize credential theft and automated login abuse.•
A08:2025 Software or Data Integrity Failures
This category is about trusting code, updates, or data without verifying integrity, signatures, and provenance. It overlaps with supply chain concerns because integrity is how you prove what you deployed is what you built.•
A09:2025 Security Logging and Alerting Failures
This covers missing visibility and weak alerting that let attacks continue undetected. It becomes catastrophic when combined with supply chain or access control issues because attackers can blend in for long periods.•
A10:2025 Mishandling of Exceptional Conditions
This risk focuses on error handling paths that leak data, crash services, or bypass controls. Attackers love exceptional paths because they are under tested and often inconsistent across services.
Definition of Software Supply Chain Failures
Software supply chain failures are breakdowns or compromises in the process of building, distributing, or updating software. OWASP emphasizes that these failures are often caused by vulnerabilities or malicious changes in third party code, tools, or other dependencies that the system relies on. The key idea is that the attacker does not need to break your application directly if they can break something you trust to build or run your application.
OWASP also gives a practical vulnerability checklist that reads like a warning label for modern product teams. If you do not track versions for all components including transitive dependencies, if you do not scan regularly and subscribe to security bulletins, and if you do not manage change across repositories, build systems, and artifact stores, you are likely exposed. OWASP explicitly calls out separation of duty, stating no single person should be able to write code and promote it all the way to production without oversight, and it also warns when your CI and CD pipeline has weaker security than the systems it builds and deploys.
For OWASP A03 in 2025, the mapped weakness themes include Use of Obsolete Function, Use of Unmaintained Third Party Components, Reliance on Component That is Not Updateable, and Dependency on Vulnerable Third Party Component. OWASP further notes that despite the scope and prevalence, only a small number of CVEs are tied to the related CWEs, which is another way of saying classic vulnerability lists do not fully capture supply chain reality. This is why an enterprise software supply chain security platform needs both governance and continuous monitoring of third party risk signals, not just one time scanning.
OWASP reports that A03 was ranked number one by fifty percent of respondents in the community survey and that contributed data shows this category has the highest average incidence rate, with the score table showing total occurrences in the hundreds of thousands. To connect this to ecosystem wide exposure, Synopsys reported that seventy four percent of assessed codebases contained high risk open source vulnerabilities in its 2024 OSSRA reporting. That is not "malware only", it is a broader signal that dependency risk is widespread and persistent even in commercial software.
Variations of Software Supply Chain Failures
This variation appears when production code relies on deprecated or unsafe functions that remain in place because refactoring is costly, risky, or simply never prioritized. It becomes a supply chain problem because those obsolete calls often live inside shared libraries, build scripts, plugins, or vendor SDKs that many services inherit automatically. OWASP maps this theme directly in A03, which is a strong framing for explaining why "we did not write this code" is not a valid defense.
A practical way to quantify the risk is to show that organizations routinely carry high risk vulnerabilities in their open source footprint, which correlates with long lived legacy patterns. Synopsys reported seventy four percent of assessed codebases contained high risk open source vulnerabilities, which is consistent with the idea that obsolete and risky constructs remain present across large portfolios.
Use of Unmaintained Third Party Components
This variation happens when the component you depend on stops receiving security fixes, maintainers disappear, or the project becomes effectively abandoned. The risk is not only known vulnerabilities, it is the inability to respond when the next issue is found because no patch is coming. OWASP explicitly calls out monitoring for unmaintained libraries and migrating when patching is not possible, which you can use as authoritative justification in your article.
The commercial takeaway is simple: the longer you run unmaintained dependencies, the more your product security becomes dependent on luck rather than engineering control.
Reliance on a Component That Is Not Updateable
This variation is common in regulated environments, legacy stacks, embedded systems, and brittle integrations where updates can break compatibility or require long approval cycles. The component might be technically updateable, but operationally it is frozen, which creates a permanent security debt that attackers can plan around. OWASP maps this directly in A03 and also warns about patching being treated as monthly or quarterly, leaving unnecessary exposure windows before fixes are applied.
A concrete way to illustrate the phenomenon is the persistence of known vulnerable versions in the wild even when fixed versions exist. Reporting based on Sonatype data around Log4j adoption has shown that a notable fraction of downloads and deployments remained vulnerable long after patches were available, and the root causes often match "we cannot update quickly" realities like version pinning and lack of oversight.
Dependency on Vulnerable Third Party Components, libraries, or tools
This is the classic dependency risk, but OWASP 2025 frames it more broadly than "a CVE in a library." It includes client side and server side components, transitive dependencies, build tools, IDE extensions, artifact repositories, and the entire chain that transforms source code into production artifacts. OWASP explicitly warns that you are likely vulnerable if you do not track versions for all components including nested dependencies and if you do not continuously monitor sources like CVE, NVD, and OSV for new vulnerability disclosures.
For data that resonates with security buyers, Sonatype reported it logged hundreds of thousands of malicious open source packages and reported year over year growth in malicious packages. This helps explain that supply chain risk is not only "accidentally vulnerable", it is also "intentionally malicious" through typosquatting, dependency confusion, and poisoned package updates.
Weak governance: one person can ship to production, and the pipeline is weaker than production
This variation is organizational and operational, not purely technical, which is why it slips through many security programs. OWASP says supply chain systems should have separation of duty, and it explicitly warns that CI and CD pipelines are often weaker than the systems they build and deploy. That matters because attackers increasingly target developer workstations, CI runners, secrets in automation, and build caches to inject malicious behavior without touching the main source repository.
GitHub reported that secret scanning detected tens of millions of secret leaks in 2024, which reflects how often sensitive credentials escape into places where supply chain attackers can grab them. Once credentials are stolen, they are used to publish malicious packages, tamper artifacts, or silently change build outputs.
Real Examples of Software Supply Chain Failures
OWASP lists the SolarWinds compromise as a canonical scenario where a trusted vendor was compromised, and downstream organizations were exposed when they upgraded. The key lesson is that the victim organizations did not need to be individually exploited at first, because the initial distribution channel did the scaling for the attacker. In other words, supply chain attacks turn trust into a force multiplier.
US government reporting noted that approximately eighteen thousand SolarWinds Orion customers were affected by the compromised update, while only a smaller subset was actively targeted for follow on exploitation. That distinction is important because it shows how supply chain failures create broad exposure even when the attacker later becomes selective.
Bybit 2025 theft and the targeted condition activation pattern
OWASP also lists the 2025 Bybit theft as a scenario where a trusted vendor behaved maliciously only under a specific condition. This is the nightmare pattern for traditional controls, because everything looks normal until the exact trigger happens in production. It is also why one time assessments of a third party are not enough, you need continuous monitoring.
NCC Group described how the attack involved malicious JavaScript injected into the Safe wallet interface, and the changes were subtle and targeted, causing the application to function normally except when the targeted wallet was about to execute a transaction. Sygnia's reporting similarly described a multi stage chain involving a developer workstation compromise, AWS access, and modification of JavaScript resources with an activation condition aimed at a specific Bybit wallet.
Shai Hulud in the npm ecosystem and automated propagation
OWASP lists Shai Hulud as an example of a self propagating npm supply chain compromise, highlighting how the malware harvested sensitive data and attempted to spread through tokens and package publishing rights. CISA published an alert describing a widespread supply chain compromise impacting the npm ecosystem and explaining how attackers authenticated as compromised developers and injected code into additional packages for rapid propagation.
Independent security research also described Shai Hulud as a self replicating worm that compromised hundreds of packages, which helps show this was not a small incident limited to obscure modules. The lesson here is that once attacker automation enters the supply chain, speed becomes the attacker advantage.

Protection and Prevention Methods for Software Supply Chain Failures
This section uses the OWASP prevention guidance directly. OWASP explicitly recommends centrally generating and managing SBOM, tracking transitive dependencies, reducing attack surface by removing unused components, and avoiding deploying updates to all systems simultaneously through staged rollouts or canary deployments. The additional guidance around continuously inventorying components and monitoring CVE, NVD, and OSV is also crucial for the continuous monitoring narrative.
1. Centrally generate and manage the SBOM of your entire softwareAn SBOM is your inventory of what you run, and it becomes the foundation for continuous third party risk monitoring because you cannot monitor what you cannot name. Engineering teams typically generate SBOMs, while security and governance teams own the policy on where SBOMs are stored, how they are validated, and how they are used in release gates. It is highly effective for speeding up incident response, because when a new vulnerability or malicious package is announced, you can quickly answer "are we exposed" and "where."
The main benefit is visibility, especially across microservices and polyglot stacks, but the main drawback is that SBOM programs fail when they are treated as paperwork instead of automation. The practical approach is to generate SBOMs per build, attach them to artifacts, and use them as a living input to continuous monitoring and third party exposure management.
2. Track not just direct dependencies, but also transitive dependencies
Most supply chain exposures hide in transitive dependencies because developers do not directly choose them, yet production still loads them. This protection is usually applied by application teams and platform teams that manage build tooling, along with security teams who set rules for allowed repositories and signing requirements. A good program combines dependency graphs with exploitability context, business criticality, and release cadence, so teams fix what matters first.
3. Reduce attack surface by removing unused dependencies and unnecessary components
Attack surface reduction works because every unused dependency is a potential future incident with no business value. It is effective because it cuts both vulnerability exposure and malicious package exposure, and it also makes incident response simpler because there is less to triage. In practice, teams get the best results when they treat dependency reduction like performance work: measure, remove, verify, repeat.
4. Avoid deploying updates to all systems simultaneously using staged rollouts and canary deployments
Staged rollouts limit blast radius, which is critical when a trusted vendor update turns out to be compromised. Platform and DevOps teams usually implement this control, with security teams defining which updates require canary stages and what signals must be clean before promotion. When paired with SBOM plus vulnerability monitoring, staged rollouts become a practical "trust but verify" strategy for third party software updates.
Protection Tools for Software Supply Chain Failures
Syft, CycloneDX tooling, and SPDX based generators are commonly used to create SBOMs as part of CI pipelines, and OWASP also maintains SBOM related guidance in its cheat sheet series. These tools help you produce machine readable inventories that can be attached to artifacts and checked in release gates. The benefit is speed and consistency, but the limitation is that they need to be integrated into every build path, including containers and serverless packaging, otherwise you create blind spots.
Software composition analysis and vulnerability alerting
OWASP Dependency Track and OWASP Dependency Check are widely referenced as practical starting points, and commercial SCA tools build on similar concepts with richer policy, remediation workflows, and IDE integration. The value is continuous monitoring of known vulnerabilities across direct and transitive dependencies, aligned with OWASP guidance to monitor CVE, NVD, and OSV. The drawback is alert fatigue, so mature teams prioritize by exploitability, asset criticality, and real world exposure rather than raw CVSS alone.
CI and CD hardening, signing, and provenance
Supply chain attacks often succeed because build and deployment systems are easier to compromise than production itself, which OWASP explicitly warns about. Tools like artifact signing frameworks, provenance attestations, and controlled release promotion help you prove that what you deployed came from the build process you intended. The benefit is integrity assurance at scale, while the tradeoff is that you must invest in key management, developer workflow changes, and enforcement, otherwise signing becomes performative.
Secrets scanning and developer workflow protection
Secrets scanning helps reduce the chance that attackers obtain the credentials needed to publish packages, modify build outputs, or access artifact stores. GitHub reported secret scanning detected more than thirty nine million secret leaks in 2024, which shows how common leakage is even in mainstream workflows. The benefit is that it blocks a common supply chain entry point, while the downside is that remediation still requires discipline: rotation, least privilege, and reducing where secrets are used at all.
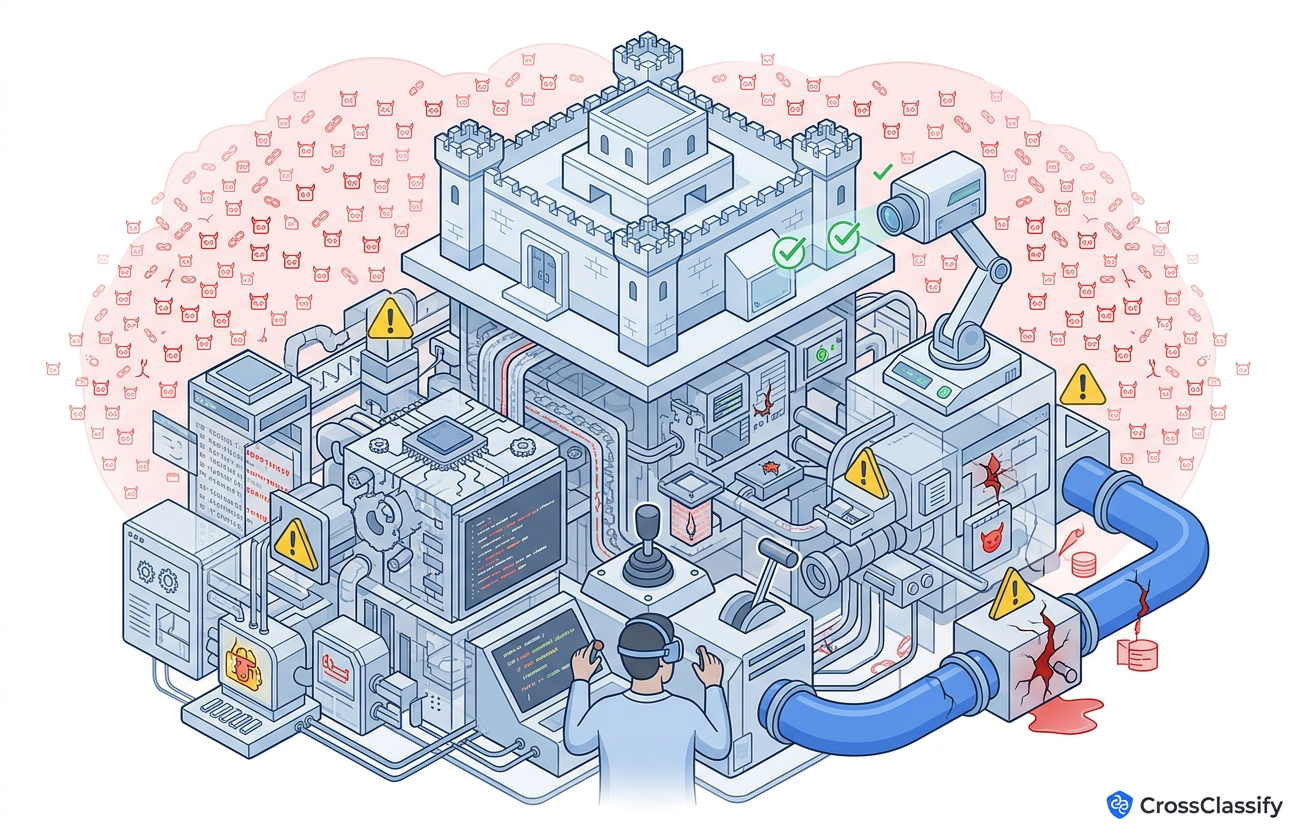
The Gap That Still Exists: Why One Time Supply Chain Checks Miss Live Third Party Abuse
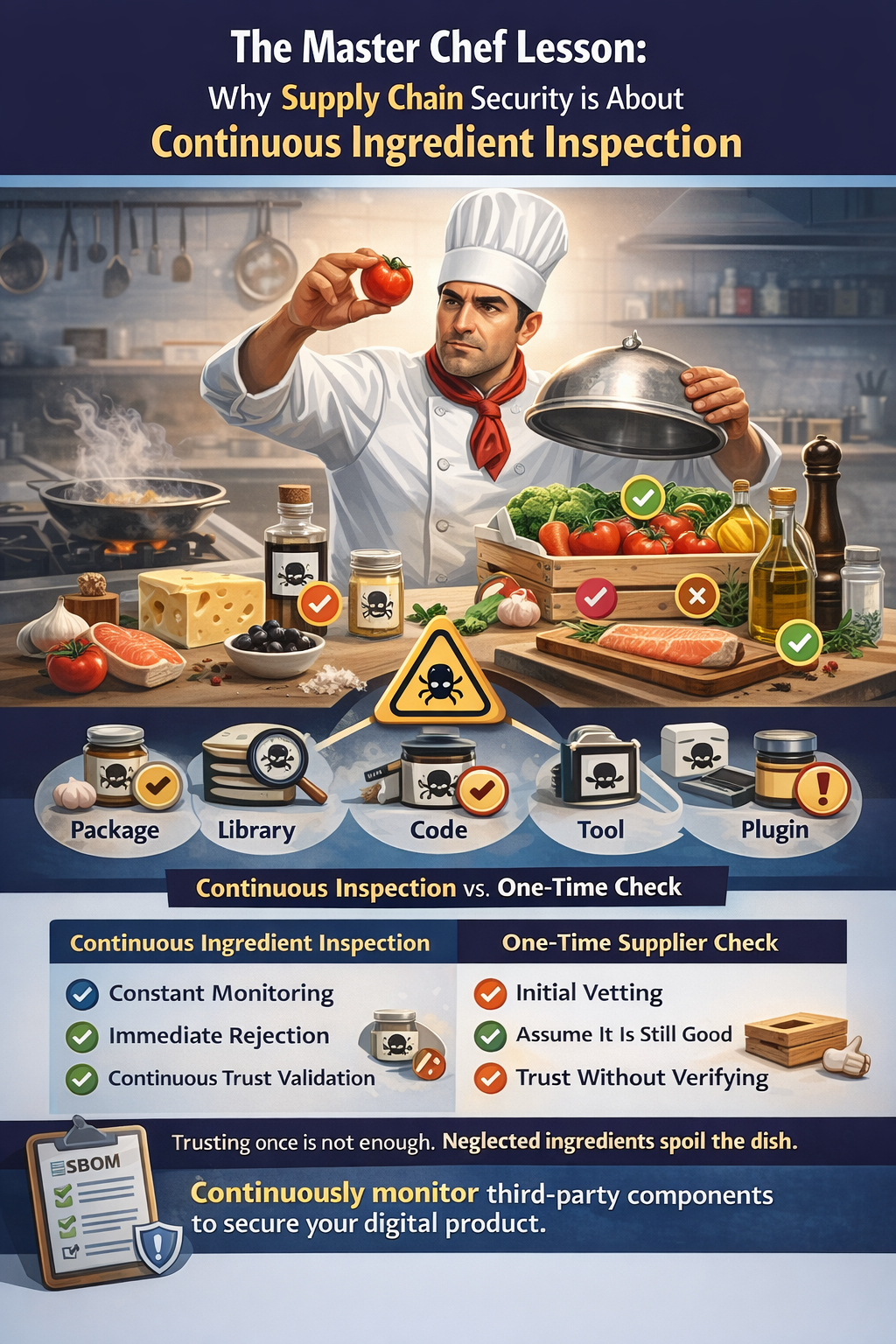
Think about building a digital product like a master chef preparing a signature dish for a high profile customer. The chef might be excellent, but the final outcome still depends on hundreds of ingredients sourced from other suppliers. If one ingredient is spoiled, the whole dish fails, and the customer blames the chef, not the supplier, because the chef chose what to use. That is exactly how Software Supply Chain Failures behave in production: one compromised dependency, one poisoned build plugin, or one malicious update can collapse the security of the whole system.
Most organizations now do some level of dependency scanning, SBOM generation, or vendor review, and those are essential. The gap is that these controls are often periodic and static, while modern supply chain attacks are adaptive and conditional, meaning they behave normally until a trigger condition happens. The Bybit case is a clear example of malicious behavior that activated only when a specific target wallet was used, which means a general audit could miss it even if it looked clean yesterday.
OWASP itself reinforces the idea that supply chain defense requires ongoing monitoring and lifetime planning, not just one time approval. OWASP explicitly says organizations must ensure an ongoing plan for monitoring, triaging, and applying updates or configuration changes for the lifetime of the application or portfolio. That lifetime focus creates the perfect bridge to CrossClassify's strengths: continuous monitoring of devices and behaviors to detect when trusted third party paths start producing abnormal outcomes like account takeover, bot abuse, or suspicious automation.
Device fingerprinting helps because many supply chain incidents quickly turn into user facing exploitation. Once malicious code reaches production, attackers use it to steal sessions, automate abuse, or bypass controls, and those actions show up as device inconsistencies, abnormal device reuse, and impossible continuity across sessions. CrossClassify's device fingerprint solution describes continuous device monitoring across sessions and the ability to detect returning fraudsters, device manipulation, and multi account patterns even when IPs, browsers, or cookies change.
This approach does not replace SBOM, SCA, and provenance controls, it complements them as a detection layer that reduces time to discovery. When a third party script, SDK, or dependency starts behaving maliciously, device identity continuity can break in measurable ways across login flows and sensitive actions. CrossClassify explicitly frames device fingerprints as a way to flag unusual device signatures during login or sensitive actions, which aligns with preventing account takeover outcomes after a supply chain compromise.
Continuous monitoring with behavioral biometrics for continuous authentication
Behavioral biometrics gives you continuous authentication without forcing friction on every user action. CrossClassify frames this as verifying real customers with behavioral biometrics and device intelligence, and it highlights detecting bots, mules, and stolen credentials without adding friction. This matters for supply chain failures because when a compromised dependency helps an attacker obtain credentials or tokens, the session can still look legitimate to classic authentication systems, but it often cannot mimic the genuine user's behavior over time.
In OWASP A03 terms, this is an answer to the "conditional" nature of supply chain attacks: you need monitoring that continues after login and after deployment, not only at build time. Behavioral biometrics can monitor navigation patterns, typing cadence, and interaction flows to spot deviations from a user's baseline, and it can flag scripted automation and suspicious activity during payouts, profile edits, and other high risk moments.
Necessity of Continuous Monitoring of Device Fingerprints and Behavioral Biometrics for Software Supply Chain Failures
Software supply chain failures are hard to prevent perfectly because modern applications are ecosystems, not isolated binaries. OWASP makes this clear by listing a wide set of vulnerable conditions, from not tracking transitive dependencies to weak change management and weak CI security. Even with strong preventive controls, incidents still happen, and the business question becomes how quickly you detect and contain the blast radius.
This is where continuous monitoring of devices and behaviors becomes a practical safety net. Supply chain incidents often convert into fraud events like account takeover, account opening abuse, and bot and abuse automation, because attackers monetize access quickly once they gain a foothold. CrossClassify's solution pages consistently emphasize continuous monitoring, risk scoring, device changes, and session anomalies as real time signals, which makes them well aligned with "continuous third party monitoring" as a protection method. When you position CrossClassify this way, you are not claiming it replaces SBOM or SCA, you are claiming it closes the time gap between compromise and detection by watching what the compromise causes in production.

Conclusion
OWASP A03 Software Supply Chain Failures is a top tier risk because modern applications are built from third party components, tools, and services that are constantly changing. OWASP data highlights both strong concern in the community survey and high incidence in contributed findings, which makes this a high intent topic for long form educational and commercial content. The right prevention program starts with SBOM and dependency governance, expands into transitive dependency visibility and attack surface reduction, and uses staged rollouts to limit blast radius when trusted vendors fail.
But the gap that still hurts most teams is detection speed in production when the compromise is conditional, targeted, or designed to look normal. Continuous monitoring of device fingerprints and behavioral biometrics is a powerful way to shorten time to discovery because it detects abnormal outcomes like session hijacking, credential stuffing, and bot automation even when authentication and trusted update channels appear valid. If you want to explore these detection layers, start from https://www.crossclassify.com/solutions/device-fingerprint/ to understand how CrossClassify builds continuous device identity signals, and then connect it to https://www.crossclassify.com/solutions/behavioral-biometrics/ to see how continuous authentication and anomaly detection can reduce fraud impact after a supply chain event.
Explore CrossClassify today
Detect and prevent fraud in real time
Protect your accounts with AI-driven security
Try CrossClassify for FREE—3 months
Share in
Frequently asked questions
Let's Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required
