25 Apr 2026
OWASP A10: Mishandling of Exceptional Conditions Is a Trust Problem After the Error
Most teams think they have solved OWASP A10 once the user no longer sees the stack trace.
That is wrong.
The real danger in OWASP Top 10 2025 Mishandling of Exceptional Conditions is not the ugly error page.
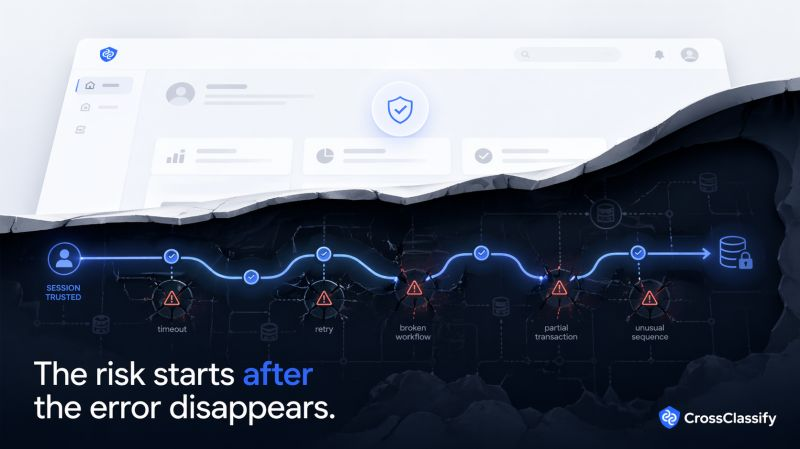
It is the moment your application quietly keeps trusting the wrong session after a timeout, a retry, a broken workflow, a partial transaction, or an unusual sequence of events.
I keep seeing the same pattern.
A team hides the stack trace.
They replace the raw error with “Please try again.”
They add logging.
They feel safer.
But the attacker is not looking at the message.
They are watching how the application behaves when things go off script.
Does it fail closed?
Does it leak clues through repeated retries?
Does it keep trusting the same device after impossible behavior?
Does it let a bot, a fraudster, or an account takeover session keep exploring the edges of the workflow?
That is the fresh take many teams miss:
OWASP A10 is not just an error handling problem.
It is a trust problem after the error.
And that changes the solution.
Rule based protection still matters.
You need safe exception handling, rollback, throttling, input validation, centralized logging, and alerting.
But that is only the baseline.
The bigger gap is what happens next.
Who is continuously monitoring the repeated failures?
Who is connecting suspicious retries across accounts?
Who is checking whether the same device, the same behavior, and the same session should still be trusted?
That is where CrossClassify becomes powerful.
By combining continuous monitoring, behavioral biometrics, device fingerprinting, account takeover protection, account opening protection, and bot and abuse protection, CrossClassify helps security teams detect when an exceptional condition is not just a technical fault, but the early signal of fraud, abuse, or compromised trust.
In other words, the strongest Mishandling of Exceptional Conditions prevention strategy is not only to hide the error.
It is to continuously evaluate the actor behind it.
That is the real shift.
Not “Did the app throw an error?”
But “Should this user, this device, and this session still be trusted after it?”
That is the full article I have been working on, and I think this is one of the most important lessons inside OWASP Top 10 2025 for modern applications.
Full article: OWASP Top 10 2025 A10 Mishandling of Exceptional Conditions Prevention Guide
