01 Apr 2026
Your biggest breach risk is not a hacker. It is a valid user doing the wrong thing.
CISOs, CTOs, and Heads of Fraud in fintech, telecom, and SaaS know this pattern:
• Credentials are valid
• MFA is enabled
• RBAC is configured
• The API passed review
And still… sensitive data gets exposed.
This is OWASP A01 2025 Broken Access Control.
Not injection.
Not malware.
Just a perfectly authenticated session accessing what it should not.
Here is the uncomfortable truth:
Broken Access Control is rarely a permissions problem.
It is a context problem.
A security team I spoke with had everything by the book.
MFA. Rate limiting. Least privilege. Security testing.
Yet suspicious activity kept slipping through.
The breakthrough came when they stopped asking:
"Was the user authenticated?"
And started asking:
"Does this look like the same human?"
Modern account takeover, account opening abuse, and bot driven API exploitation do not break the front door.
They walk in with stolen keys.
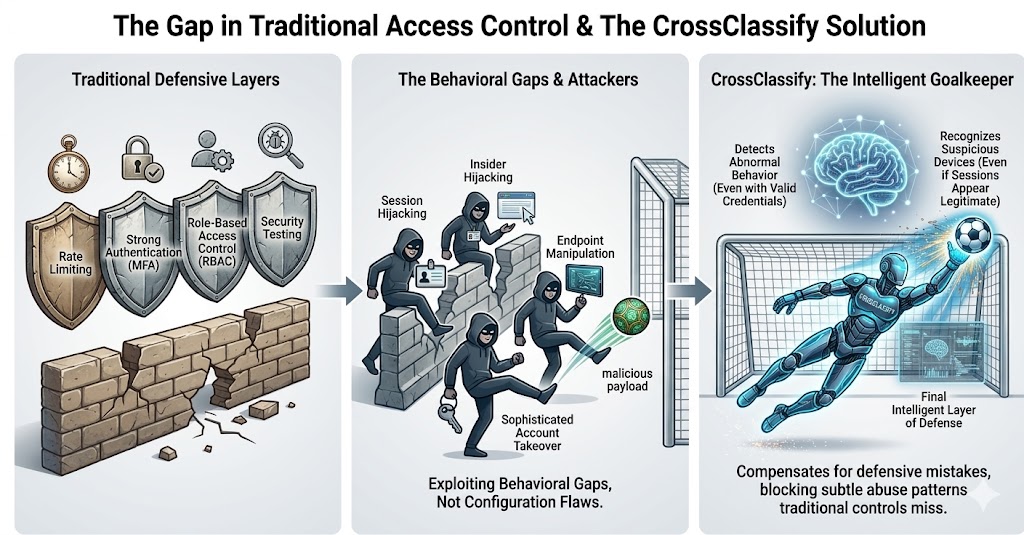
Traditional OWASP Top 10 mitigation is necessary.
But not sufficient.
CrossClassify acts as the goalkeeper of your application.
Device fingerprinting for enterprise broken access control prevention detects untrusted devices even when credentials are valid.
Behavioral biometrics fraud detection software continuously validates user interaction patterns to expose insider misuse and session hijacking.
RBAC and MFA are your defenders.
CrossClassify protects the goal line.
The real competitive advantage is not just blocking known vulnerabilities.
It is detecting when a legitimate session is actually malicious.
That is the shift.
That is where CrossClassify plays.
