20 Apr 2026
OWASP A09: You Can Log Everything and Still Miss the Attack That Matters
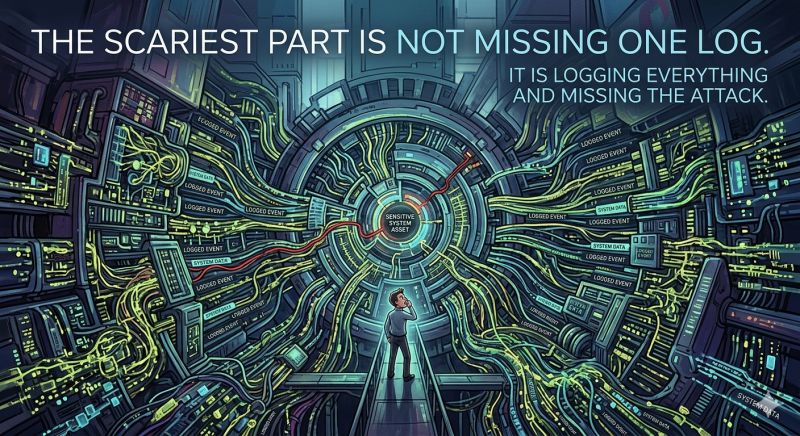
The scariest part of OWASP Security Logging and Alerting Failures is not that you might miss one log.
It is that you might log almost everything and still miss the attack that matters.
That is the uncomfortable question behind OWASP A09:2025 that keeps coming back for security teams, fraud teams, and application owners.
Are we logging enough for a real incident?
Are our logs rich enough to explain what actually happened?
If we are already storing huge amounts of data, can we truly monitor it in real time?
And when a new fraud pattern appears, will our monitoring adapt fast enough to catch it?
While working on this topic, I kept coming back to one fresh conclusion:
Security Logging and Alerting Failures is no longer mainly a logging problem.
It is an interpretation problem.
Most teams focus on collecting more events.
But attackers do not care how much data you store.
They care whether they can hide inside normal looking activity long enough to win.
That is where the real gap lives.
A failed login is easy to log.
A compromised session using valid credentials is much harder to recognize.
A suspicious device shift hidden inside a normal user journey is even harder.
A bot that behaves just enough like a human can pass through traditional thresholds without raising the right alert.
So the real answer is not just more logs.
It is continuous monitoring, adaptive risk detection, device fingerprinting, and behavioral biometrics working together.
That is why I believe the strongest response to OWASP Security Logging and Alerting Failures prevention is a system that does not only record activity, but continuously asks:
Is this still the same user?
Is this still a trusted device?
Does this behavior still match the real account owner?
Does this session still deserve trust right now?
This is exactly where CrossClassify becomes powerful.
By combining continuous monitoring for account takeover protection, device fingerprinting for suspicious session detection, behavioral biometrics fraud detection, and adaptive risk scoring for bot and abuse protection, CrossClassify helps teams move from passive logging to active trust assessment.
That shift matters.
Because in modern applications, the biggest failure is often not lack of visibility.
It is lack of intelligent visibility.
If your team is discussing OWASP A09, fraud detection for modern applications, continuous monitoring for suspicious user behavior, or real time alerting for adaptive fraud prevention, this is the conversation worth having now.
