16 Apr 2026
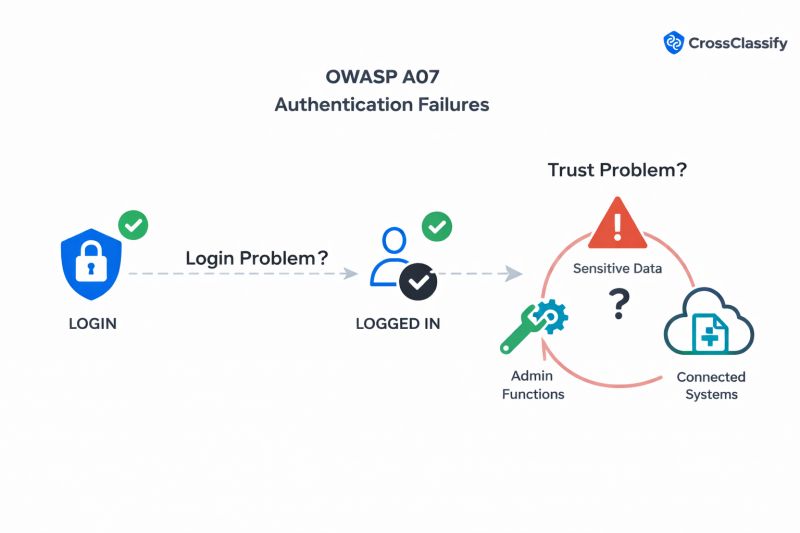
OWASP A07: Authentication Failures Don't End at Login
A user passes MFA.
The WAF stays quiet.
The credentials look valid.
And the account still gets taken over.
That is the part too many security teams still refuse to admit:
OWASP A07 Authentication Failures is not just a login problem.
It is a trust problem after login.
Credential stuffing does not care that you enabled MFA.
Session hijacking does not care that your login page looks secure.
Human fraud does not care that your perimeter controls passed the request.
Because once the wrong actor gets inside, most systems keep trusting them for far too long.
That is the real gap.
Not failed login.
Successful attacker login.
And that is exactly why stronger authentication alone is not enough anymore.
You need continuous trust assessment.
You need to keep asking:
Is this still the same user?
Is this still the same device?
Does this behavior still match the real account owner?
That is where CrossClassify changes the game.
With device fingerprinting and behavioral biometrics, CrossClassify helps detect the signals traditional controls miss:
reused credentials
session hijacking
device spoofing
post login abuse
fake account behavior
bot and abuse fraud
The strongest defense against Authentication Failures is not just blocking bad logins.
It is detecting bad trust after login.
That is the shift.
And teams that do not make it will keep wondering why accounts are still getting taken over even after they "did everything right."
